Traditional network defenses struggle to stop threats that get past the perimeter. Attackers often move inside corporate networks without much resistance. Zero Trust steps in with a strict rule: never trust, always check, no matter where a user or device connects from.
Businesses are now targets for more complex attacks than ever before. As a result, old security models leave too many openings. Zero Trust models help by limiting the damage a breach can cause, but building and maintaining them is a demanding process.
This post breaks down what Zero Trust means for company networks, the basic setup steps, and common pitfalls. You’ll see how this security model fits today’s risk landscape and why careful planning is the only way to get real protection. If you’re looking for related strategies or practical setup advice, check our guide on AI cybersecurity tools for beginners.
What Is a Zero Trust Model?
The Zero Trust model stands out as a direct answer to today’s network security problems. Instead of assuming anything within the network can be trusted, Zero Trust takes the opposite approach—no one and nothing gets a free pass. This policy treats every access request as suspicious until identity and permissions are proven, regardless of location or device.
Key Principles of Zero Trust
Several core ideas make up the foundation for any Zero Trust strategy. Let’s look at these core principles:
- Never Trust, Always Verify: Every access request, whether from inside or outside the network, undergoes strict checks. Verification doesn’t stop after initial login; it’s continuous.
- Least Privilege Access: Users and devices only get the permissions needed for their tasks. This limits what an attacker can do if they compromise an account.
- Micro-Segmentation: The network breaks into smaller zones. Crossing from one segment to another triggers new checks. This containment approach keeps breaches from spreading.
- Assume Breach: Systems operate as if someone is already inside. This leads to heavy monitoring and quick reactions to anything out of the ordinary.
These principles make it harder for threats to move around if they penetrate your defenses.
How Zero Trust Differs from Traditional Security
Traditional security often relies on strong perimeters and trusts users once they gain access. With Zero Trust, there are no safe zones; trust is always earned, never given.
| Traditional Security | Zero Trust |
|---|---|
| Perimeter-focused | Identity- and context-based |
| Trusts users inside the network | Verifies every user or device |
| Flat network structure | Segmented, with constant verification |
| Occasional authentication | Continuous risk evaluation |
Zero Trust removes implicit trust, whether users connect from a company office, remotely, or from any device.
Why Zero Trust Matters for Corporations
Complex attacks often target weak points in networks, especially where old policies assume too much trust. Zero Trust offers a response by shutting down the usual paths attackers take to move laterally or escalate privileges.
- Reduces attack surfaces by limiting user and device permissions
- Speeds up detection through granular logging and monitoring
- Fits hybrid and remote work setups, where users connect from anywhere
Many major cloud and security providers, such as Microsoft and CrowdStrike, offer resources on Zero Trust. For a detailed breakdown, check Microsoft’s Zero Trust overview and CrowdStrike’s Zero Trust security model guide.
As corporate networks keep expanding and attackers get smarter, the Zero Trust model equips organizations to stay ahead. With strict access controls and constant validation, Zero Trust helps create a more secure network foundation.
Key Elements of Zero Trust Architecture
To put Zero Trust into action within a corporate network, several technical elements work together to reduce risk. Each layer addresses a different point of entry or attack, helping catch threats before they spread. Here’s a breakdown of the most important Zero Trust components that shape a strong security model.
Continuous Verification and Least Privilege
In Zero Trust, access rights are never static. Organizations must check user identity, device state, and activity on an ongoing basis. This goes far beyond a single login. When a user moves across applications or tries to download files, the system evaluates risk with every action.
Continuous verification keeps attackers from moving freely if they compromise one account. If abnormal behavior appears—like accessing data at odd hours or from an unknown device—the system can challenge the user again or block the action entirely. This tight feedback loop helps spot threats before they become breaches.
Least privilege means users and devices only get the access needed to do their tasks. This limits the fallout from an attack. For example:
- Employees in HR shouldn’t have access to engineering project folders.
- An IoT device used for climate control should not connect to the company’s financial systems.
By enforcing least privilege at all times, Zero Trust reduces the “blast radius” of a compromise. If privileges are restricted to the smallest set needed, attackers hit more walls and have fewer opportunities to escalate.
Micro-Segmentation and Granular Access Control
Micro-segmentation divides the network into smaller pieces or “zones.” Each of these segments has its own access rules and policies. If attackers get into one zone, they can’t automatically reach the rest of the network. This is like having multiple locked doors inside a building, each requiring its own key.
Some ways companies use micro-segmentation include:
- Separating guest Wi-Fi from internal business systems.
- Isolating development environments from production systems.
- Giving third-party vendors access only to specific, limited areas.
Granular access control allows security teams to create specific rules for who can go where and do what inside each zone. A developer may access source code in a test environment, but is blocked from production databases. These controls adapt to user roles, data sensitivity, and even device health.
This layered defense makes it much more difficult for threats to move laterally or escalate inside the environment. For readers looking for additional guidance, the National Institute of Standards and Technology outlines practical micro-segmentation strategies for Zero Trust environments.
Identity Management and Multi-Factor Authentication
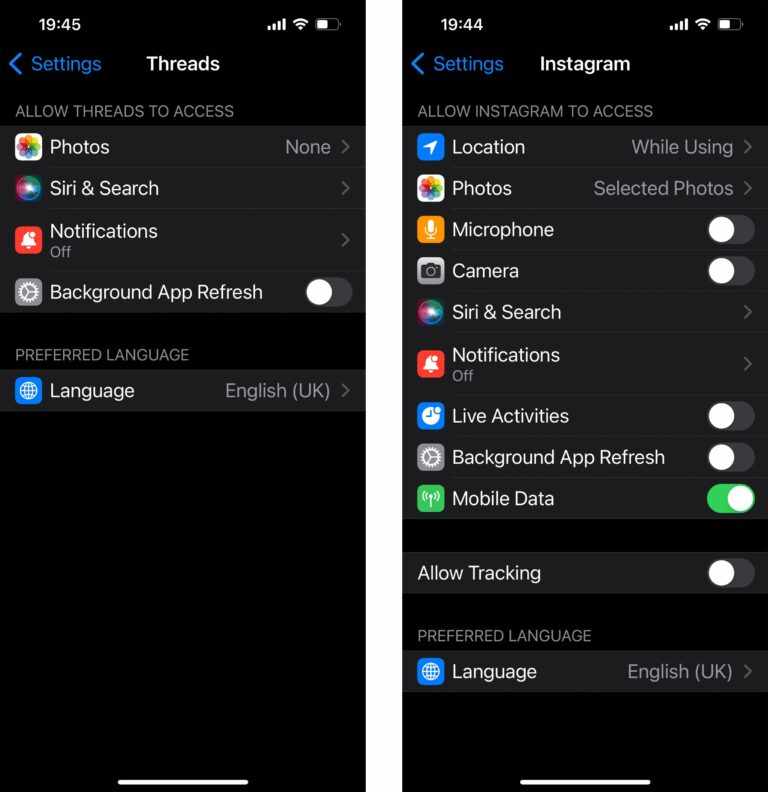
Identifying who is requesting access is the core of any security strategy. In a Zero Trust setup, identity management relies on more than just usernames and passwords. Modern approaches use a mix of:
- Biometric logins
- Security tokens
- Context (device health, network used, location data)
Multi-factor authentication (MFA) adds a strong layer by requiring two or more ways to verify identity. Even if a password leaks, an attacker still faces a barrier—like an app-generated code or fingerprint. This step stops most account hijacks.
Dynamic policies kick in based on risk. For instance, logging in from an unusual location could prompt extra checks. These systems adjust access in real-time.
To see how these principles influence applications beyond infrastructure, our review of AI content creation tools for bloggers and YouTubers covers how adaptive multi-factor authentication is changing digital content workflows.
Security Analytics and Continuous Monitoring
Zero Trust depends on real-time analytics to keep visibility high in every part of the network. Security teams need to know when patterns break, such as an employee suddenly accessing large volumes of sensitive files outside of work hours.
Continuous monitoring tools collect and analyze:
- User and device activity logs
- Behavior patterns and anomalies
- Access requests and denials
Automated systems flag suspicious behavior as it happens, not hours or days later. Analytics platforms can even predict risks by learning what normal activity looks like, so anything odd stands out quickly.
This all-around visibility, combined with automated alerts, empowers teams to investigate incidents early and contain threats before they spread to other areas of the business. For more about the shift toward AI-powered security analytics, check solutions like IBM’s Security QRadar platform which support these continuous monitoring workflows at scale.
How to Set Up a Zero Trust Model in Corporate Networks
Implementing a Zero Trust model in corporate networks requires a clear understanding of existing resources, designing precise access controls, and adopting robust identity verification systems. This model challenges traditional security by enforcing strict verification for every access attempt, regardless of user or device location. Successful deployment depends on systematic planning across four key areas: assessing network assets, defining granular access policies, deploying identity and monitoring solutions, and educating staff on security practices.
Assessing Existing Network and Resources
Before establishing Zero Trust, you need a detailed picture of your current network. Start by identifying critical assets including servers, applications, data stores, and devices. Map out data flows to understand how information moves within and across network boundaries. This helps pinpoint where sensitive data resides and which paths require the most protection.
Analyze user roles and their usual tasks to classify who needs what level of access. Don’t overlook service accounts or automated processes that also interact with network resources.
A thorough evaluation includes:
- Cataloging hardware and software assets with their vulnerabilities
- Documenting data sensitivity and compliance requirements
- Reviewing existing access patterns and user privileges
This foundation ensures your Zero Trust architecture targets genuine risk points instead of applying broad rules that may disrupt operations.
Defining Access Policies and Micro-Segments
Zero Trust depends on breaking the network into smaller, manageable units called micro-segments. This approach stops attackers from moving freely once inside your network. Each segment should have its own tailored access rules based on the sensitivity of contained resources.
When setting policies, apply the principle of least privilege strictly. Design rules to control who can access what, when, and from which device or location. These policies should consider:
- User roles and responsibilities
- Device security posture
- Application sensitivity
- Network traffic types and origins
Logical segmentation creates layers of defense. For example, isolate financial databases from general user areas, or separate third-party vendor access from core systems. By tightly controlling east-west traffic between segments, you reduce the risk of lateral movement from a compromised point.
Implementing Identity, MFA, and Analytics Solutions
Identity is the cornerstone of Zero Trust. Deploy strong identity verification methods including multi-factor authentication (MFA) to ensure users and devices prove who they claim to be. MFA incorporates something the user knows (password), has (token or app), or is (biometrics) for solid security beyond simple passwords.
Integrate identity solutions with real-time analytics tools that monitor user behavior continuously. Analytics detect anomalies such as unusual login times, impossible travel between locations, or access to non-typical resources. These insights enable immediate adjustments to access controls or trigger alerts for investigation.
Effective Zero Trust platforms combine:
- Centralized identity and access management (IAM)
- MFA enforcement across all access points
- Behavioral analytics and risk scoring
Monitoring is not a one-time process but ongoing vigilance to catch threats early and automatically respond to suspicious activities.
Education and Training for Staff
Technology alone cannot secure your Zero Trust deployment. Users must understand how their behavior affects security and what new procedures are expected of them. Training programs should emphasize the importance of strong passwords, recognizing phishing attempts, and following access policies without shortcuts.
Regular awareness sessions help reduce risky behavior, improve compliance with access controls, and smooth transitions as new security tools roll out. Empowering staff with knowledge also creates a security-first mindset, turning every employee into a line of defense.
Consider creating tailored materials and simulations that reflect real corporate scenarios. This practical approach makes lessons clear and relevant.
For organizations exploring AI-powered training resources to support security awareness, learning more about how nonprofits use AI for staff education offers useful insights into modern training methods.
This framework for setting up a Zero Trust model ensures your corporate network remains resilient against intrusions while maintaining efficient user access. Each step builds on the last, producing a layered and enforceable security system designed for today’s evolving threats.
Most Common Pitfalls and How to Avoid Them
Adopting a Zero Trust model in corporate networks is more than just installing new software or flipping a switch. Many organizations stumble over assumptions and missed steps that slow down or weaken their security efforts. Recognizing the usual mistakes helps keep your deployment on track and effective. Below are the most common pitfalls to watch out for and practical ways to avoid them.
Misunderstanding Zero Trust as a Product
A frequent error is treating Zero Trust as just a product or tool to buy. Zero Trust is not a single firewall, application, or software suite you install to “fix” security. Instead, it is a continuous strategy focused on verifying every access attempt with strict controls and monitoring.
Viewing Zero Trust as an ongoing process rather than a one-time project changes how you design and maintain it. It demands regular updates to policies, technology improvements, and staff training to respond to evolving threats. Security teams need to integrate many components—identity management, device health checks, segmentation, analytics—to enforce the model effectively.
This mindset shift avoids the trap of expecting instant results from technology alone. Success comes from adapting and reinforcing the strategy over time.
Underestimating Integration with Legacy Systems
Many corporate networks still rely heavily on legacy systems. These older platforms often lack the compatibility or built-in support required to fit into a Zero Trust framework. Ignoring this reality can create blind spots.
Incomplete coverage of legacy systems means attackers could exploit unprotected paths, bypassing the strict controls applied elsewhere. For example, legacy applications may permit broad access or fail to provide detailed logs needed for continuous verification.
To prevent gaps, it’s critical to:
- Inventory all legacy assets and evaluate their security limitations.
- Use additional controls like network micro-segmentation and protocol-level filtering.
- Consider phased upgrades or compensating security measures where integration is impossible.
Failing to properly address legacy systems compromises the overall effectiveness of Zero Trust.
Neglecting User Experience and Organizational Impact
A Zero Trust model alters how users access resources, which can cause frustration and resistance if not carefully managed. Overlooking usability or the business context risks slowing adoption or causing security measures to be bypassed.
If staff face too many hurdles or complex authentication steps, they may seek shortcuts, increasing risk. Similarly, if policies don’t align with actual business workflows, teams may find them impractical, creating friction and delays.
To avoid these problems:
- Design access controls that balance security with reasonable user convenience.
- Involve business units early to understand operational needs.
- Educate employees on the reasons behind changes to foster cooperation.
Successful Zero Trust programs treat user experience as part of security, not a separate concern.
Skipping Continuous Monitoring and Policy Updates
Implementing Zero Trust is not a “set and forget” task. Threats change, users move roles, and new devices connect continuously. Sticking to static rules without ongoing review weakens defenses over time.
Without constant monitoring and policy tuning, suspicious activity can go undetected or legitimate changes can create gaps. Automated analytics help spot anomalies, but security teams must act on these insights quickly.
Effective Zero Trust requires:
- Continuous logging of user and device activity.
- Frequent review and adjustment of access policies based on risk.
- Incident response processes that adapt to new intelligence.
This dynamic management prevents your Zero Trust model from becoming outdated as the environment shifts.
Implementing Zero Trust is challenging, but being aware of these common pitfalls lets you build stronger, more adaptable security. Careful planning around strategy, legacy integration, user impact, and ongoing management is essential for real protection.
Future Directions and Innovations in Zero Trust
The Zero Trust model is not static. As cyber threats evolve, so must the defenses organizations deploy. Looking ahead, Zero Trust will continue to expand with new technologies and methodologies that strengthen protection while addressing current limitations. Understanding these future trends helps companies prepare better security architectures and improve their ongoing risk management.
Advances in Identity and Access Management
Identity verification forms the core of Zero Trust, and innovations in this area promise more reliable and user-friendly methods. Passwords alone are becoming obsolete. The future will see wider adoption of biometric authentication, such as facial recognition and fingerprint scanners, integrated with adaptive risk scoring to verify users continuously. These systems analyze context like device health, location, and usage patterns to dynamically adjust access levels.
Decentralized identity platforms based on blockchain are also gaining traction. These reduce reliance on centralized identity providers, minimizing risks related to single points of failure and data breaches.
AI-Driven Threat Detection and Response
Artificial intelligence (AI) is reshaping how Zero Trust environments detect and respond to threats. Machine learning algorithms analyze vast amounts of network data to identify anomalies and suspicious behaviors that human analysts might miss. This capability allows faster detection of lateral movement and insider threats.
AI automation can trigger enforcement actions instantly, such as temporarily revoking access or isolating devices showing unusual activity, reducing response time to seconds.
Integration of Cloud Security Posture Management (CSPM)
With more corporate resources migrating to the cloud, Zero Trust strategies are increasingly incorporating Cloud Security Posture Management (CSPM) tools. CSPM monitors cloud configurations continuously to identify misconfigurations or compliance risks that could open doors for attackers.
Future Zero Trust frameworks will link CSPM insights directly into identity and access governance controls, ensuring that cloud environments adapt automatically to emerging threats and policy changes.
Quantum-Resistant Cryptography
Quantum computing presents potential risks to current encryption methods that Zero Trust relies upon for secure communications and authentication. Research into quantum-resistant cryptographic algorithms is underway, aiming to prepare Zero Trust models for a future where quantum machines could break traditional encryption.
This innovation will be critical to maintaining long-term data integrity and secure identity verification under the Zero Trust framework.
Zero Trust for IoT and Edge Devices
The growing number of Internet of Things (IoT) and edge computing devices introduces new challenges. These devices often lack strong built-in security and complicate identity management. Upcoming Zero Trust implementations will focus on:
- Device attestation methods to verify hardware integrity.
- Specialized micro-segmentation tailored to IoT traffic patterns.
- Lightweight authentication protocols that suit resource-constrained devices.
Strengthening IoT security within Zero Trust will prevent these devices from becoming weak links in corporate networks.
Enhanced User Experience in Security
Balancing security with usability remains crucial. Innovations aim to reduce friction by embedding Zero Trust checks invisibly. For instance, behavioral biometrics can continuously authenticate users in the background without interrupting workflows. Context-aware adaptive policies will reduce redundant prompts while maintaining rigorous checks.
This approach ensures users comply without feeling burdened—a critical factor for long-term success.
Staying informed about these developments will help security teams evolve their Zero Trust models effectively. The future points toward deeper automation, stronger identity guarantees, and broader coverage across all types of devices and infrastructure.
For further reading on emerging Zero Trust trends, you can explore detailed analyses such as The Future of Zero Trust by Birchwood University, which covers new identity management and AI techniques shaping this field. Also, IBM’s insights on next steps after Zero Trust highlight the role of AI and quantum computing in enhancing IT security frameworks.
Conclusion
Implementing a Zero Trust model requires treating security as an ongoing process, not a one-time fix. Organizations must continuously assess network conditions, update access policies, and monitor user behavior to keep defenses effective against evolving threats.
Avoiding common pitfalls such as over-reliance on tools or neglecting legacy systems ensures a more comprehensive security posture. Balancing strict controls with user experience helps secure access without disrupting daily operations.
Staying informed on emerging trends and maintaining vigilant monitoring will strengthen your Zero Trust approach over time. For those exploring broader cybersecurity strategies, understanding how to adapt and maintain security is a crucial next step. Consider following updates on how AI impacts security monitoring to keep your network defenses current and effective.



Leave a Comment