Closing the Browser Security Gap: Strategic Choices and Systemic Impacts in 2026
Understanding the Browser Security Gap and Key Decision Points
In today’s digital landscape, securing browsers has become a critical concern for organizations aiming to protect against high-grade cyber threats. As of 2026, the persistent browser security gap—referring to the disconnect between endpoint protection tools and network security systems—remains a prominent vulnerability exploited by sophisticated, evasive cyber threats (HEAT). Organizations are faced with important architectural decisions on how to effectively close this gap, choosing between endpoint and cloud-based security solutions. Each approach offers distinct advantages and challenges, impacting application compatibility, system performance, and user experience.
What is the Browser Security Gap?
The browser security gap is the divide between traditional endpoint protections, such as antivirus and malware detection, and network security measures like firewalls and intrusion prevention systems. This gap creates an avenue for advanced threats that can bypass conventional defenses, particularly those that adapt in real-time to evade detection. HEAT attacks (Highly Evasive Adaptive Threats) exploit vulnerabilities in common browsers or leverage zero-day exploits to penetrate enterprise defenses without triggering alarms.
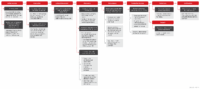
Architectural Approaches to Closing the Browser Security Gap
1. Endpoint Security Solutions
Endpoint strategies primarily involve deploying replacement browsers—uniform, hardened versions of popular browsers—across all organizational devices. Examples include Palo Alto Prisma Browser, Surf, Island, and similar solutions that replace legacy browsers with a single, secure alternative based on Chromium or other engines designed to minimize attack surfaces.
- Advantages: Standardized security profile, easier management, simplified patching, and consistent security policies.
- Disadvantages: Limited flexibility, potential application incompatibility, and reduced user satisfaction. For instance, when security hardening disables features like Just-in-Time (JIT) compilation or WebAssembly, performance and functionality can substantially decline.
2. Cloud-Based Security Solutions
Cloud security offers an alternative approach that complements or replaces endpoint solutions. It involves intercepting and analyzing web traffic in real-time, regardless of the browser used, without restricting or replacing the browser itself. This method secures all browser activity by mediating web access from the cloud, thus maintaining user choice and application functionality.
- Advantages: Preserves browser choice, maintains compatibility with diverse enterprise applications, and ensures minimal performance impact.
- Disadvantages: Requires reliable internet connectivity, potential privacy concerns, and the need for comprehensive cloud infrastructure.
Why the Choice of Browser Security Strategy Matters for Organizations
Deciding between endpoint and cloud-based browser security is more than a technical choice; it influences business operations, user productivity, and security posture. Each option carries implications for application compatibility, system performance, security coverage, and user satisfaction.
The Impact of Standardization and Browser Choice
Many organizations support multiple browsers—such as Chrome, Firefox, Safari, Edge, and even legacy IE-11—to meet diverse application requirements. The widespread use of multiple browsers aligns with business needs for flexibility and compatibility. However, enforcing a single, hardened replacement browser typically eliminates this flexibility, introducing risks such as:
- Application Incompatibility: Critical software may only support certain browsers, risking potential operational disruptions if a chosen replacement browser does not support those applications.
- Functionality Risks: Security measures that disable features like JIT or WebAssembly can hamper performance, disable key functions, or cause breakages in active workflows.
Case Study: Real-World Challenges of Browser Replacement
For example, a company selecting a replacement browser discovered that disabling the WebAssembly engine impaired a telephony component integral to customer support, illustrating how security priorities can unintentionally disrupt vital services. Such scenarios emphasize that security can’t be viewed in isolation—it must be balanced with usability and operational continuity.
How Companies Can Make Informed Browser Security Decisions in 2026
- Assess Business Needs and Application Compatibility: Conduct thorough evaluations of existing applications and workflows to identify potential incompatibilities.
- Evaluate Security Posture Requirements: Determine whether endpoint hardening, cloud security, or a hybrid approach best aligns with organizational risk tolerance.
- Test and Pilot Solutions: Implement trial runs with different browsers and security methods to gauge impact on performance and user satisfaction.
- Implement User-Centric Policies: Involve end-users in decision-making to balance security objectives with productivity and experience.
- Establish Continuous Monitoring: Regularly review browser performance, security effectiveness, and compatibility to adapt strategies as needed.
Emerging Trends and Future Directions for Browser Security
In 2026, the landscape of browser security continues to evolve rapidly. Key trends shaping this field include:
- Zero Trust Architectures: Increasing adoption of zero trust models that verify each web session regardless of browser choice.
- Enhanced Cloud Security Platforms: Development of more sophisticated cloud proxies capable of analyzing encrypted traffic without impacting performance.
- AI-Driven Threat Detection: Leveraging artificial intelligence to detect and block HEAT attacks proactively at both endpoints and in the cloud.
- Improved Application Compatibility: Building browsers and security tools that support a broader range of enterprise applications without compromising security.
Benefits and Drawbacks of Different Browser Security Strategies
Pros and Cons of Endpoint-Based Browser Security
- Pros:
- Consistent security policies across devices
- Simpler management and patching
- Enhanced control over browser configurations
- Cons:
- Reduced flexibility for users and applications
- Higher risk of incompatibility and performance issues
- Potential user dissatisfaction due to restrictions
Pros and Cons of Cloud-Based Browser Security
- Pros:
- Maintains browser diversity and compatibility
- Supports user preference and operational continuity
- Less intrusive, with adaptable security controls
- Cons:
- Dependence on internet reliability
- Potential privacy and compliance concerns
- Requires investment in cloud infrastructure and management
Conclusion: Making the Best Choice for 2026
When selecting a browser security strategy in 2026, organizations must carefully weigh benefits against risks, considering their specific operational needs and threat landscape. Cloud-based solutions offer flexibility, preserving application compatibility and user satisfaction, making them increasingly attractive. Still, endpoint strategies can provide robust, centralized control but at the cost of flexibility and potential compatibility challenges. The optimal approach often involves a hybrid solution tailored to balance security, performance, and usability.
Frequently Asked Questions (FAQs)
What is the safest way to close the browser security gap?
The most effective approach combines cloud-based security measures with endpoint protections, ensuring comprehensive coverage while maintaining application compatibility and user satisfaction. Deploying adaptive, AI-powered security platforms that analyze traffic in real-time and support diverse browsers offers a balanced solution.
Are replacement browsers better for security?
Replacement browsers can enhance security by reducing attack surfaces through standardization and hardening. However, they may introduce compatibility issues and reduce user flexibility, which can impact productivity and application functionality.
What are the risks of enforcing a single, hardened browser?
Key risks include breaking support for critical business applications, impairing workflows due to disabled features (like JIT or WebAssembly), and decreasing user satisfaction. It can also lead to potential operational disruptions if compatibility issues are overlooked during deployment.
How does cloud security improve browser protection?
Cloud security provides a flexible, scalable layer that monitors all web traffic, regardless of browser choice. It blocks threats like HEAT attacks before they reach endpoints, maintains application compatibility, and supports remote work environments effectively.
Will AI enhance browser security in the future?
Yes, AI is increasingly used to predict, detect, and block sophisticated cyber threats in real-time. AI-driven security platforms offer adaptive defenses that evolve alongside emerging threats, making them essential for future browser security strategies.




Leave a Comment