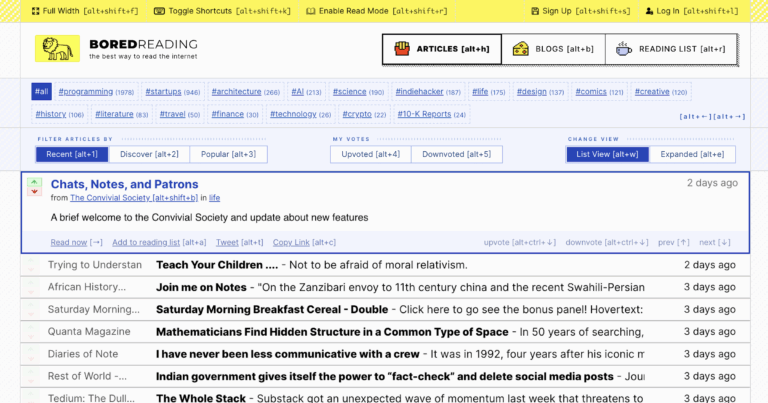
Unraveling the Mystery of Browser Visibility: A Critical Challenge in Modern Cybersecurity
In today’s digital landscape, achieving effective browser visibility remains one of the toughest puzzles for cybersecurity professionals, despite technological advancements and sophisticated security tools. As organizations increasingly depend on cloud-based applications and rely heavily on web browsers for everyday operations, understanding how to monitor, analyze, and secure web browsing sessions has become essential. This comprehensive guide explores the importance of browser visibility, the challenges faced, innovative solutions, and best practices to enhance security in 2026 and beyond.
Understanding the Significance of Browser Visibility in Cybersecurity
Browser visibility refers to the ability of security teams to see and analyze what happens during web browsing activities. This visibility is critical because malicious actors increasingly target browsers as primary attack vectors. With web browsers serving as gateways to cloud applications, email, and enterprise resources, they represent a significant security concern that traditional network monitoring tools often overlook.
In the context of cybersecurity, visibility into browsing sessions allows organizations to detect phishing attempts, drive-by downloads, malicious scripts, and other web-based threats. However, despite the wealth of security data available from networks, endpoints, and SaaS platforms, many organizations lack complete visibility into browser activity, leaving critical gaps in their security posture.
The Growing Importance of Browser Security in 2026
By 2026, the trajectory indicates that enterprise browsers will evolve from auxiliary tools to core security and productivity platforms. As companies increasingly adopt web apps and cloud solutions, especially in remote or hybrid work environments, the browser becomes the primary interface for most digital activities. Consequently, traditional security tools that monitor network traffic or endpoint behavior are no longer sufficient.
- According to recent studies, organizations use an average of 371 SaaS applications in 2024, with SaaS spending projected to grow by 20% during the same year.
- By 2030, enterprise browsers are expected to be the central platform for delivering security solutions and productivity applications across both managed and unmanaged devices.
Why Does Browser Visibility Present Such a Difficult Challenge?
Multiple factors contribute to the persistent difficulty of achieving full browser visibility. Chief among them is the fact that browsers operate as complex, dynamic environments constantly manipulating content, scripts, and data streams. Unlike traditional network monitoring, which can intercept and analyze traffic at fixed points, browsers run on local devices, often in ways that evade detection.
Key reasons for limited visibility include:
- High volume and diversity of web traffic — hundreds of millions of web sessions per day.
- Use of encryption protocols such as TLS/SSL, which encrypt traffic and mask malicious payloads from inspection.
- Rapid updates and vulnerabilities — browsers like Chrome and Edge report dozens of CVEs annually, reflecting their popularity but also their attack surface.
- Emerging exploits — browser-based vulnerabilities have increased by 56% in recent years, underscoring their attractiveness to cybercriminals.
- User resistance to security measures involving browser controls, especially when these interfere with productivity or preferences.
Risks Associated with Limited Browser Visibility
The consequences of insufficient browser monitoring are severe. Without proper visibility, organizations could be unaware of active threats, resulting in data breaches, sophisticated phishing campaigns, and ransomware infections. Attackers leverage the browser’s complexity to execute exploits that bypass traditional security layers.
Some typical risks include:
- Most initial compromises start with malicious links or downloads within the browser.
- Data exfiltration through browser sessions, especially via compromised cloud services.
- Persistence of malware hidden in browser cache or extensions.
- Remote code execution via malicious scripts embedded on legitimate websites.
Conventional Approaches and Their Limitations
Many enterprises have attempted to address browser security through strategies such as deploying alternative browsers or blocking specific web content. However, these approaches often lead to user frustration and reduced productivity, as they do not address the core issue of visibility.
Common strategies include:
- Forcing the use of a standardized enterprise browser.
- Blocking or restricting access to risky websites.
- Implementing endpoint security solutions with limited browser inspection capabilities.
- Utilizing traditional Web Application Firewalls (WAFs) that cannot see inside encrypted sessions.
While these measures can reduce some attack vectors, they are insufficient for comprehensive browser security, especially given the evolving threat landscape.
Innovative Solutions for Browser Visibility in 2026
The latest advancements in browser security focus on transforming the browser into a secure environment that can be monitored effectively without sacrificing user experience. One promising approach is deploying a **Secure Enterprise Browser**—a virtualized or cloud-based solution that provides real-time visibility and control.
Features of modern browser security solutions include:
- Cloud-based real-time analysis: Security teams can monitor and analyze web sessions in real time, identifying threats immediately.
- Adaptive Clientless Rendering: Rendering web content in the cloud rather than on local devices reduces vulnerabilities and enhances security.
- AI-powered threat detection: Use of artificial intelligence and computer vision to detect malicious content before it reaches users.
- Content integrity verification: Ensuring that web content has not been tampered with or loaded with malicious scripts.
- User transparency: Security measures are integrated seamlessly so users experience minimal disruption.
Advantages of adopting cloud-based secure browsers:
- Enhanced security: Reduces attack surface by executing browsing sessions in a controlled, cloud environment.
- Improved visibility: Provides detailed reports on browsing activities, threat detections, and incident responses.
- Reduced false positives: AI-driven analysis minimizes unnecessary alerts and focuses on genuine threats.
- Regulatory compliance: Better audit trails and data security for sensitive information.
- Scalability: Easily scalable across offices, remote workers, and unmanaged devices.
Implementing a Secure Enterprise Browser: Step-by-Step Guide
To leverage the benefits of browser visibility solutions effectively, organizations should follow a structured implementation process:
- Assessment of current security posture: Identify gaps in browsing session monitoring and define key threat vectors.
- Select a suitable cloud browser platform: Evaluate solutions like Menlo Secure Cloud Browser or equivalents that support real-time analysis and AI detection.
- Stakeholder engagement: Educate and involve security teams, IT admins, and end-users to ensure smooth adoption.
- Deployment and integration: Configure the cloud browser with existing security policies, SSL inspection, and threat detection rules.
- Monitoring and tuning: Continuously monitor browser session logs, threat alerts, and user feedback to optimize security settings.
- Training and awareness: Educate users on safe browsing practices and how to report suspicious activity.
Pros and Cons of Cloud-Based Browser Security
Pros
- Superior threat detection: Combines AI, computer vision, and cloud analysis for advanced security.
- Seamless user experience: Minimal impact on workflows while maintaining high security standards.
- Centralized control: Easy to enforce policies and update protections across all devices.
- Scalable and flexible: Adaptable to organizational growth and remote work models.
Cons
- Implementation complexity: Requires careful planning and integration with existing infrastructure.
- Potential latency: Depends on network quality and cloud server location.
- Cost considerations: Cloud solutions can incur additional expenses compared to traditional browsers.
Future Trends in Browser Security and Visibility
The evolution of browser security in 2026 suggests several emerging trends:
- Increased AI integration: More advanced threat recognition and automatic response capabilities.
- Standardization of security protocols: Development of industry-wide standards for browser security measures.
- Zero-trust adoption: Browser environments will be integrated into zero-trust architectures for more granular control.
- Enhanced user privacy: Balancing security with privacy through techniques like anonymized content rendering.
- Integration with broader security ecosystems: Seamless collaboration with SIEMs, SOAR platforms, and endpoint protection tools.
Frequently Asked Questions (FAQs) About Browser Visibility in Cybersecurity
What is browser visibility, and why is it important?
Browser visibility refers to the capability to monitor, analyze, and control web browsing activities within an organization. It’s essential because browsers are primary attack vectors used by cybercriminals to deliver malware, steal data, or conduct phishing campaigns. Effective visibility allows security teams to detect and prevent threats proactively.
How does limited browser visibility impact organizations?
Limited visibility can lead to undetected threats, data breaches, compromised user accounts, and unauthorized data exfiltration. It hampers incident response and increases risks related to evolving web-based attacks.
What are current solutions for improving browser visibility?
Modern approaches include deploying secure cloud-based browsers, integrating AI-powered threat detection, and using adaptive rendering techniques. These solutions provide real-time analysis without disrupting user productivity.
What are the advantages of using a cloud-based secure browser?
Benefits include enhanced threat detection, detailed security insights, better user experience, scalable deployment, and compliance support.
Are there any drawbacks to cloud-based browser security?
Challenges involve implementation complexity, potential latency issues, and additional costs. Proper planning can mitigate these concerns.
What trends are shaping the future of browser security?
AI advancements, zero-trust frameworks, standardization, privacy considerations, and ecosystem integration are key developments to watch in browser security.
Conclusion
In 2026, browser visibility remains a critical component of cybersecurity strategies. Addressing this challenge involves adopting innovative solutions like secure enterprise browsers that leverage AI, cloud computing, and adaptive rendering to monitor and protect web sessions proactively. Organizations that invest in these technologies will be better equipped to defend against web-based threats, ensuring safer digital environments for employees and customers alike.



Leave a Comment