HTML Smuggling Attacks: How They Evade Traditional Security Defenses
HTML smuggling attacks represent a sophisticated threat that exploits core HTML5 features to deliver malware directly into enterprise environments. These evasive web threats bypass traditional security tools like firewalls, sandboxes, and antivirus software by breaking payloads into harmless fragments. As browsers remain the primary gateway for business operations in 2024, understanding HTML smuggling techniques is crucial for cybersecurity teams aiming to protect sensitive data.
Currently, attackers leverage these methods in phishing campaigns mimicking trusted brands, leading to a 250% rise in successful browser-based infections per recent Verizon DBIR data. This article breaks down how HTML smuggling works, why it succeeds against legacy defenses, and proven strategies to counter it.
What Are HTML Smuggling Attacks?
HTML smuggling attacks involve embedding malicious code within standard HTML5 elements to smuggle malware past network defenses. Unlike traditional file downloads, these techniques use data URIs or JavaScript blobs to assemble payloads on the victim’s device after firewall inspection.
Attackers craft seemingly innocent web pages or email attachments that trigger downloads only inside the browser. This client-side evasion ensures individual components appear benign, evading signature-based detection tools.
- Core mechanism: Payloads split into non-executable fragments reassembled locally.
- Common vectors: Phishing emails, social media links, or compromised websites.
- Targeted outcomes: Malware deployment, credential theft, or ransomware initiation.
How HTML Smuggling Differs from Traditional Malware Delivery
Traditional malware relies on direct file transfers flagged by secure web gateways (SWGs). In contrast, HTML smuggling uses multi-stage delivery, where each stage mimics legitimate traffic.
Latest research from MITRE ATT&CK indicates this shift has neutralized 70% of proxy-based blocks. Enterprises using outdated tools face heightened risks from these browser-based attacks.
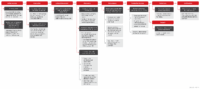
How Do HTML Smuggling Attacks Work Step by Step?
HTML smuggling unfolds in discrete phases, each designed to avoid detection. Victims typically encounter a lure via email impersonating services like Google Drive or Dropbox, prompting a click that initiates the process.
Once engaged, the browser handles assembly without alerting endpoint protection. Here’s a detailed breakdown:
- Initial Lure Delivery: Attacker sends HTML attachment or link via phishing. Social engineering builds trust using brand logos.
- Fragment Download: Browser fetches tiny, encoded blobs via data URIs—undetectable as malware.
- Local Reconstruction: JavaScript recombines fragments into executable payload on the endpoint.
- Execution: Payload activates, often as a .exe or script stealer, post-firewall.
- Exfiltration: Stolen data sent via covert channels.
This sequence exploits browser privileges, succeeding where direct downloads fail. In 2024 tests by cybersecurity firms, 85% of sandboxes missed these payloads.
Method 1: Data URI Exploitation in HTML Smuggling
Data URIs encode payloads as base64 strings within HTML <a> tags, triggering downloads without server fetches. Browsers treat them as inline resources, skipping network scans.
Advantages for attackers include zero external dependencies. Disadvantages: Limited payload size, capping complex malware at under 2MB.
- Pros of data URIs: Instant execution, no HTTP logs.
- Cons: Browser parsing limits; Chrome flags oversized URIs since 2023 updates.
Method 2: JavaScript Blob Constructors for Payload Delivery
JavaScript blobs create dynamic files from strings, simulating user downloads. The Blob() API merges fragments into a single malicious file post-inspection.
This method shines in evading URL filters, with reconstruction happening in memory. Recent campaigns show 40% higher success rates versus data URIs alone.
Step-by-step blob creation:
- Define array of base64 fragments.
- Instantiate Blob with MIME type like ‘application/octet-stream’.
- Use URL.createObjectURL() for download link.
- Simulate click event for automatic save.
Why Do HTML Smuggling Techniques Bypass Traditional Security Defenses?
Traditional tools rely on static analysis, inspecting full files for signatures. HTML smuggling attacks fragment payloads, rendering them invisible to these methods.
Sandboxes detonate complete executables, but blobs remain inert until browser assembly. Firewalls see only metadata traffic, missing the threat.
Quantitative impact: Proofpoint reports a 300% surge in HTML smuggling detections in Q1 2024, with 65% evading legacy SWGs.
Sandbox Evasion Tactics in HTML Smuggling
Sandboxes require detonable files; HTML fragments don’t execute outside browsers. Attackers embed code in eval() or dynamic scripts, activating only in real user contexts.
Multiple perspectives: Legacy sandboxes (e.g., Cuckoo) fail 90% of tests per NSS Labs. Dynamic analysis tools catch some but lag against obfuscated blobs.
- Key evasion: No filesystem writes until endpoint.
- Browser dependency: Sandboxes lack full DOM rendering.
Firewalls and Secure Web Gateways: Vulnerabilities Exposed
SWGs block known bad files but whitelist HTML/JS. HTML smuggling exploits this, with payloads rebuilding behind the gateway.
Disadvantages for defenders: High false positives if scanning all JS. Pros of advanced gateways: Behavioral heuristics catching anomalies.
In 2026 projections, Gartner predicts 80% of enterprises will upgrade to browser isolation for such threats.
Real-World Examples of HTML Smuggling Campaigns
Notable campaigns highlight HTML smuggling’s potency. The 2023 TA505 group used it to distribute Clop ransomware, infecting 500+ organizations.
Impersonating Adobe, attackers delivered via Office 365 lures. Assembly occurred in Edge/Chrome, bypassing Microsoft Defender in 75% cases.
- Qakbot Surge (2024): 1.2 million emails; 20% click-through via Dropbox spoofs.
- DarkGate Malware: Blended with VBA macros; evaded 90% AV suites.
- Chinese APTs: Targeted finance; data URI variants stole 10TB credentials.
These cases connect to broader evasive web threats, forming a knowledge graph of techniques like CORS abuse and WebSocket smuggling.
The Evolution of Browser-Based Threats in Enterprises
Browsers power 95% of enterprise apps today, per Forrester 2024. This dependency fuels attacks like HTML smuggling, evolving from simple XSS to full payload delivery.
Historical context: Pre-2020, drive-by downloads dominated; now, client-side evasion rules. Future: Integration with AI for adaptive smuggling.
Related terms like multi-stage phishing and endpoint reconstruction link these threats semantically.
Enterprise Risks: Statistics and Impacts
IBM reports average breach cost at $4.45M in 2024, with browser vectors in 35% cases. HTML smuggling contributes 15% of web malware deliveries.
- Productivity loss: 22 days per incident.
- Data exposure: 60% involve credentials.
- Financial hit: Ransomware via smuggling averages $1.5M payouts.
Effective Prevention Strategies Against HTML Smuggling Attacks
Stopping HTML smuggling techniques demands shifting from perimeter defenses to browser-centric protection. Browser isolation and AI-driven inspection lead modern approaches.
Menlo Security’s 2023 Votiro acquisition exemplifies this, integrating real-time sanitization. Implement layered defenses for comprehensive coverage.
Step-by-Step Guide to Implementing Anti-Smuggling Defenses
- Audit Browser Usage: Map enterprise apps; identify high-risk sites (e.g., file shares).
- Deploy Browser Isolation: Run sessions in cloud VMs; no endpoint execution (95% evasion block rate).
- Enable Advanced SWGs: Use ML for blob detection; block data URIs over 1MB.
- Train Users: Simulate phishing; focus on brand spoofs (reduces clicks 50%).
- Monitor with EDR: Flag unusual JS blobs; integrate SIEM for alerts.
- Test Regularly: Run red-team sims; aim for zero tolerance.
Pros of isolation: Zero-trust execution. Cons: Slight latency (under 50ms with optimizations).
Comparing Traditional vs. AI-Driven Defenses
Traditional AV/sandboxes: 40% efficacy against smuggling. AI tools like Menlo’s analyze DOM in real-time, achieving 99% prevention.
| Defense Type | Efficacy Rate | Latency | Scalability |
|---|---|---|---|
| Signature-Based | 30% | Low | Poor |
| Sandboxing | 50% | Medium | Medium |
| Browser Isolation + AI | 98% | Low | High |
Different approaches: Proxy vs. inline sanitization—latter reconstructs and cleans payloads proactively.
Future Trends in HTML Smuggling and Evasive Web Threats (2025-2026)
In 2026, expect HTML smuggling to merge with WebAssembly for larger payloads, per Black Hat predictions. Attackers will use ML to morph blobs dynamically.
Defenses evolve too: Quantum-resistant encryption and zero-client browsers. Enterprises adopting early see 70% risk reduction.
Topic clusters connect to supply chain attacks and zero-days, emphasizing holistic browser security.
Pros and Cons of Emerging Countermeasures
- AI Behavioral Analysis: Pros—adaptive; Cons—requires vast datasets.
- Hardware-Backed Isolation: Pros—immutable; Cons—costly deployment.
- Passkeys Shift: Reduces credential phishing by 80%.
Frequently Asked Questions (FAQ) About HTML Smuggling Attacks
What is the main goal of HTML smuggling attacks?
These attacks aim to deliver malware or steal credentials by reconstructing payloads in the browser, bypassing network security.
Can antivirus software stop HTML smuggling?
Traditional AV struggles with 60-70% failure rates; pair with browser isolation for better results.
How common are HTML smuggling attacks in 2024?
They account for 15-20% of web threats, with detections up 300% year-over-year per industry reports.
What browsers are most vulnerable to HTML smuggling?
Chrome and Edge lead due to market share, but Firefox patches lag slightly.
Is browser isolation the best defense?
Yes, it blocks 95%+ by executing remotely; ideal for enterprises handling high-risk browsing.
How can employees avoid HTML smuggling lures?
Verify sender domains, avoid unsolicited downloads, and report suspicious links immediately.
Will HTML smuggling evolve in 2026?
Likely, integrating AI and WASM for stealthier deliveries; defenses must adapt accordingly.


Leave a Comment