Comprehensive Guide to Purple Teaming in Cybersecurity
—
Introduction to Purple Teaming in Cybersecurity
In today’s rapidly changing digital landscape, cybersecurity professionals constantly need to adapt and evolve their defensive and offensive strategies. Traditional approaches often involve dividing efforts between the so-called Blue Team—focused on defense—and the Red Team—specializing in attack simulations. However, a growing trend in cybersecurity is the emergence of Purple Teaming, a collaborative approach that combines the strengths of both teams to enhance organizational security. In 2026, as cyber threats become more sophisticated and persistent, understanding the concept of Purple Teaming is more important than ever for cybersecurity practitioners, organizations, and enterprises aiming to create resilient defenses.
What Is Purple Teaming and Why Is It Critical?
Defining Purple Teaming in Cybersecurity
Purple Teaming in cybersecurity refers to an integrated approach where offensive and defensive teams work together seamlessly. Unlike traditional models where Red and Blue Teams operate independently—often in a competitive or isolated manner—Purple Teaming fosters collaboration to improve security posture actively. It aims to bridge the gap between attack simulation (Red Team activities) and defense mechanisms (Blue Team operations), ensuring continuous feedback, learning, and strategy refinement.
In essence, Purple Teaming transforms cybersecurity from a static, siloed process into a dynamic, cooperative cycle of testing, learning, and adapting.
The Importance of Purple Teaming in 2026
As cyber threats evolve in complexity, so must the strategies to counter them. The latest research indicates that organizations practicing Purple Teaming report faster detection times—up to 30% quicker—and improved incident response accuracy. In 2026, integrating offensive and defensive cybersecurity efforts is seen as a best practice for staying ahead of increasingly elusive hackers, ransomware operators, and nation-state cyber adversaries.
Core Principles and Benefits of Purple Teaming
Key Principles of Effective Purple Teaming
- Collaboration over confrontation: Encourages open communication and joint problem-solving.
- Shared knowledge: Facilitates continuous learning for both teams.
- Real-time feedback: Immediate analysis and response to simulated attacks or vulnerabilities.
- Continuous improvement: Iterative testing and refining of security controls.
- Goal-oriented: Focused on closing security gaps and strengthening defenses.
Advantages of Purple Teaming
- Enhanced Detection and Response: Faster identification and mitigation of vulnerabilities.
- Improved Security Posture: More resilient defenses through collaborative testing.
- Knowledge Sharing: Cross-team insights lead to better strategies and protocols.
- Cost Efficiency: Reduced redundancy and minimized resource waste by combining efforts.
- Increased Organizational Awareness: Cultivates a security-aware culture across departments.
Potential Challenges and Drawbacks
- Coordination Complexity: Aligning objectives and communication between offensive and defensive teams requires effort.
- Resource Intensive: May demand additional training, tools, and personnel.
- Possible Role Confusion: Clear boundaries and responsibilities must be established to avoid conflicts.
Implementing Purple Teaming: A Step-by-Step Guide
Step 1: Establish Clear Objectives
Define what your organization aims to achieve through Purple Teaming. Typical goals include improving threat detection, enhancing incident response protocols, or testing specific security controls. Setting measurable objectives ensures the collaboration stays focused and effective.
Step 2: Foster Collaboration and Communication
Create channels for frequent communication—such as regular meetings or shared platforms—between Red and Blue Teams. Establish a common language and shared understanding to facilitate knowledge transfer and coordination.
Step 3: Develop a Joint Testing Framework
Design coordinated attack simulations and defense exercises. Use frameworks like colored team exercises, penetration testing, or Red Team assessments, and integrate the Blue Team’s real-time defense responses. Employ automation tools and dashboards to monitor activities.
Step 4: Share Insights and Adjust Strategies
After sessions, hold debriefings to analyze successes, failures, and areas for improvement. Use this feedback to adjust security policies, refine detection systems, and update incident response plans.
Step 5: Iterate and Automate
Implement continuous cycles of testing and improvement. Incorporate automation to streamline testing, threat hunting, and response processes, reducing manual workload and increasing efficiency.
Tools and Technologies Supporting Purple Teaming
Automated Penetration Testing Tools
- Nmap
- Metasploit
- Burp Suite
- BloodHound
Security Information and Event Management (SIEM) Systems
- Splunk
- AlienVault
- IBM QRadar
Threat Intelligence Platforms
- Recorded Future
- Anomali
- VirusTotal
Collaboration and Communication Platforms
- Slack
- Microsoft Teams
- Confluence
Success Stories and Case Studies of Purple Teaming
Many leading organizations have adopted Purple Team strategies with measurable success. For instance, a Fortune 500 financial firm reported a 25% decrease in security incident response time after implementing joint Red and Blue team exercises. A government agency experienced a 40% increase in threat detection accuracy within six months of establishing a dedicated Purple Team.
Different Approaches to Purple Teaming in Practice
Fully Integrated Model
In this approach, Red and Blue Teams are combined into a single, cross-functional team working dynamically. This model fosters rapid learning and real-time adjustment of security measures.
Collaborative but Separate Teams
Here, Red and Blue Teams operate separately but collaborate closely during and after testing exercises. This approach maintains clear role boundaries while promoting information sharing.
Hybrid Approach
Some organizations blend both models, assigning specific personnel to perform joint activities intermittently, balancing independence with collaboration.
Pros and Cons of Different Purple Teaming Strategies
- Fully Integrated Model: High agility and fast feedback, but requires cultural change and flexible staffing.
- Separate Teams with Collaboration: Clear roles and accountability, yet potentially slower to respond.
- Hybrid Model: Combines benefits but may increase complexity and resource demands.
Future Trends in Purple Teaming: What to Expect in 2026
By 2026, cybersecurity experts anticipate that Purple Teaming will become standard practice across industries. Advances in automation, AI-driven threat simulations, and real-time analytics will enhance coordination. The role of the Purple Team will evolve into a core function—embedded within organizations’ security operations centers (SOCs)—driving proactive defense measures and resilience-building strategies.
FAQs About Purple Teaming in Cybersecurity
- What is the main goal of Purple Teaming in cybersecurity?
- The primary objective is to improve security by fostering cooperation between attack simulation (Red Team) and defense (Blue Team), leading to more effective detection, response, and prevention of cyber threats.
- How is Purple Teaming different from traditional Red and Blue Teams?
- While traditional Red and Blue Teams often operate independently with limited interaction, Purple Teaming emphasizes continuous collaboration, joint exercises, and shared insights for faster and more comprehensive security improvements.
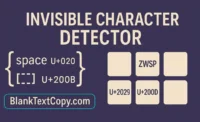
- What tools support Purple Teaming activities?
- Automated penetration testing platforms, SIEM systems, threat intelligence tools, and collaborative platforms like Slack or Teams are commonly used to facilitate Purple Team exercises.
- What are the challenges of implementing Purple Teaming?
- Challenges include aligning team goals, resource allocation, communication gaps, and maintaining effective coordination, especially in large or complex organizations.
- Can small businesses benefit from Purple Teaming?
- Yes, even small organizations can adopt simplified versions of Purple Team strategies, focusing on collaborative threat simulations and shared learning to strengthen their defenses without extensive resource investments.
Conclusion: Embracing Collaboration for Stronger Cybersecurity in 2026
As cyber threats become more sophisticated and persistent, adopting a collaborative security approach like Purple Teaming is increasingly vital. By integrating offensive and defensive efforts into a unified process, organizations can achieve faster detection, improved response times, and a more resilient security infrastructure. The future of cybersecurity lies in cooperation, continuous learning, and innovation—making Purple Teaming not just an option but a necessity for enterprises aiming to stay protected in the digital age. Whether you’re a cybersecurity beginner or an experienced professional, understanding and implementing Purple Teaming can significantly elevate your organization’s defense capabilities in 2026 and beyond.
Frequently Asked Questions (FAQs) about Purple Teaming in Cybersecurity
- What exactly is Purple Teaming?
It’s a cybersecurity strategy where offensive (Red Team) and defensive (Blue Team) professionals collaborate continuously to improve an organization’s security defenses through shared exercises and insights. - How does Purple Teaming benefit organizations?
It enhances threat detection speed, reduces incident response time, promotes effective knowledge sharing, and strengthens overall cybersecurity resilience. - What are common tools used in Purple Team exercises?
Popular tools include penetration testing software, security information and event management (SIEM) systems, threat intelligence platforms, and collaborative communication tools. - Who should lead Purple Team initiatives?
It’s often led by a cybersecurity manager or a dedicated Purple Team coordinator, who ensures cross-team communication and strategic alignment. - Can small businesses implement Purple Teaming?
Yes, with simplified exercises and focused collaboration, small organizations can effectively adopt Purple Team strategies to bolster their defenses.

Leave a Comment