Browser Security: Essential for CMMC 2.0 Compliance in 2026
Browser security plays a pivotal role in achieving CMMC 2.0 compliance, especially for organizations in the Defense Industrial Base handling sensitive Federal Contract Information (FCI) and Controlled Unclassified Information (CUI). As web browsers evolve into superapps where users spend over 90% of their workday, they have become prime targets for highly evasive adaptive threats (HEAT). In 2026, with cyber threats leveraging AI-powered attacks and zero-day exploits rising by 25% year-over-year according to recent cybersecurity reports, robust browser security for CMMC 2.0 compliance is non-negotiable to align with NIST SP 800-171 standards.
The streamlined CMMC 2.0 model features three levels—Foundational, Advanced, and Expert—making Level 2 critical for CUI protection. Without dedicated browser defenses, vulnerabilities can lead to data breaches, non-compliance fines up to $100,000 per violation, and loss of DoD contracts. This guide explores why browser security is indispensable, implementation strategies, and best practices to fortify your cybersecurity posture.
What is CMMC 2.0 and Why Does Browser Security Matter?
CMMC 2.0, the Cybersecurity Maturity Model Certification, safeguards the Defense Industrial Base by enforcing standardized cybersecurity practices. It replaced the more complex CMMC 1.0 with three tiers to reduce barriers for contractors while ensuring protection of FCI and CUI.
Understanding the Three CMMC 2.0 Levels
Level 1 (Foundational) requires basic hygiene like safeguarding FCI through 15 NIST controls, suitable for non-CUI handlers. Level 2 (Advanced) demands full NIST SP 800-171 compliance with 110 controls for CUI, often needing third-party assessments. Level 3 (Expert) adds 24 NIST 800-172 practices against advanced threats.
- Level 1: Self-assessment; focuses on awareness training and access control.
- Level 2: Critical for 80% of DoD contractors; includes vulnerability management and incident response.
- Level 3: Government-led audits for high-risk environments.
Browser security integrates across all levels, particularly Level 2, where web traffic carries 70% of malware per Verizon’s 2025 DBIR.
Connection Between NIST SP 800-171 and Browser Security
NIST SP 800-171 outlines 14 families of controls, including access control, system integrity, and media protection. Browsers, as endpoints for web apps handling CUI, must enforce these to prevent unauthorized access.
“Browsers are the new perimeter; unsecured ones expose CUI to browser-borne threats daily.” – Adapted from Gartner’s 2023 Enterprise Browser Report
How Do Browser Threats Impact CMMC 2.0 Compliance?
In today’s threat landscape, browsers face sophisticated attacks that bypass traditional defenses. The latest Menlo Security State of Browser Security Report (2025) reveals AI-driven phishing surged 40%, with 65% of breaches originating from web vectors.
Key Browser-Based Threats to Watch in 2026
HEAT attacks evade detection by mutating code in real-time. Zero-day vulnerabilities in browsers like Chrome and Edge exploit unpatched flaws, compromising endpoints before updates deploy.
- Phishing-as-a-Service (PhaaS): Kits enable non-experts to launch convincing attacks via collaboration tools like Microsoft Teams.
- Malicious Files in Archives: Password-protected ZIPs hide ransomware, invisible to network scanners.
- Brand Impersonation: 55% of phishing uses trusted domains, per Proofpoint’s 2025 report.
These threats directly violate CMMC’s risk assessment (3.11.1) and flaw remediation (3.14.1) controls.
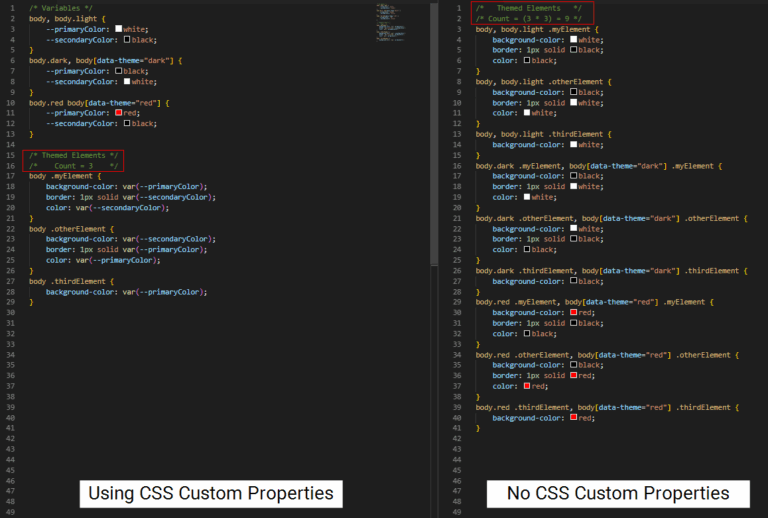
Pros and Cons of Traditional vs. Cloud Browser Security
Traditional endpoint detection struggles with browser isolation due to update lags—users avoid restarts, leaving 30% of systems vulnerable.
| Approach | Pros | Cons |
|---|---|---|
| Replacement Browsers | Simple isolation | Compatibility issues; no zero-day protection; requires restarts |
| Cloud-Based Security | Always-updated; sandboxing; 70% alert reduction | Higher initial setup; cloud dependency |
Cloud solutions offer disposable containers, aligning better with CMMC’s continuous monitoring requirements.
Why is Browser Security Crucial for Protecting CUI Under CMMC 2.0?
Level 2 mandates protecting CUI from unauthorized access, where browsers serve as the gateway. Without defenses, a single click can exfiltrate gigabytes of data.
Defending Against Unauthorized Access
Implement managed configurations, DLP policies, and MFA for web apps. Browser security enforces granular controls like clipboard restrictions, preventing copy-paste leaks.
- DLP scans full files, including encrypted ones, blocking 95% of data exfiltration attempts.
- MFA integration reduces unauthorized entry by 99%, per Microsoft stats.
Mitigating Malicious Code and Zero-Days
CMMC requires vulnerability scanning (3.14.2). Cloud browser security applies patches instantly via remote browsers, shielding users from exploits without disruptions.
Currently, zero-days account for 20% of breaches; AI-powered shields detect them up to 6 days faster than legacy AV.
Best Practices for Implementing Browser Security in CMMC Compliance
Achieving CMMC 2.0 compliance demands a layered approach. Here’s a step-by-step guide to integrate browser security.
Step-by-Step Checklist for CMMC 2.0 Browser Security
- Assess Current Risks: Audit browser usage; identify CUI-handling apps. Use tools mapping to NIST 800-171.
- Choose Architecture: Opt for cloud-native over replacements for scalability. Ensure sandboxing for all sessions.
- Secure File Traffic: Deploy file inspection, AV, and hashing for archives—critical as 40% of malware hides in web downloads.
- Enable Secure App Access: Replace VPNs with browser-based zero-trust access for BYOD and contractors, reducing attack surface by 50%.
- Integrate DLP with Context: Monitor browser behaviors like uploads/downloads; limit paste actions.
- Train and Monitor: Combine awareness with automated blocks; aim for <70% alert fatigue reduction.
- Audit and Certify: Document controls for C3PAO assessments.
Quantitative Benefits of Browser Security
Organizations report 70-80% fewer incidents post-implementation. SOC efficiency improves with 70% alert reduction, per industry benchmarks.
- Cost Savings: Avoid $4.45M average breach cost (IBM 2025).
- Compliance Speed: Accelerate Level 2 certification by 40%.
Future Trends: Browser Security and CMMC in 2026 and Beyond
The latest research indicates generative AI will amplify threats, with GenAI phishing rising 300% by 2026 (Gartner). CMMC 2.0 will evolve to include AI governance.
Different Approaches to Emerging Threats
Pros of AI-driven shields: Proactive blocking. Cons: False positives (5-10%). Hybrid models combining rules and ML offer balance.
Secure enterprise browsers will dominate, providing isolation for GenAI tools while maintaining productivity.
Topic Cluster: Related CMMC Challenges
- Zero-Trust Integration: Browsers as enforcement points.
- Supply Chain Risks: Secure third-party web apps.
- Remote Work: BYOD policies under CMMC.
- GenAI Security: Protecting browser-based AI from prompt injection.
Conclusion: Secure Your Path to CMMC 2.0 Success
Browser security is the linchpin for CMMC 2.0 compliance, bridging NIST requirements with real-world threats. By adopting cloud-based solutions, checklists, and ongoing training, Defense contractors can protect CUI, streamline SOC operations, and win more contracts.
In 2026, as threats accelerate, proactive measures will differentiate compliant organizations. Start with a risk assessment today to build a resilient cybersecurity maturity model.
Frequently Asked Questions (FAQ)
What is the role of browser security in CMMC 2.0 Level 2?
It enforces NIST SP 800-171 controls like access management and vulnerability remediation, protecting CUI from web threats.
How does cloud browser security differ from traditional methods for CMMC compliance?
Cloud versions provide instant updates and sandboxing without user disruptions, outperforming replacements that lag on zero-days.
Can browser security help reduce SOC alert fatigue?
Yes, by up to 70%, allowing focus on high-priority incidents.
What are common browser threats under CMMC scrutiny?
Phishing, zero-days, and file-based malware, which violate integrity and media protection controls.
How long does CMMC 2.0 certification take with strong browser security?
Typically 6-12 months for Level 2, accelerated by integrated defenses.



Leave a Comment