The Shadow in Your Pocket: Intellexa’s Predator Spyware and the Evolving Threat of iOS Zero-Day Exploits
In an era where our smartphones are extensions of ourselves, containing our most intimate communications, financial data, and personal memories, the threat of sophisticated surveillance looms larger than ever. Despite increasing international pressure and public condemnation, mercenary spyware vendors continue to innovate, developing tools capable of bypassing even the most robust security measures. Intellexa, a company at the forefront of this shadowy industry, has once again demonstrated its alarming adaptability. Their potent surveillance tool, “Predator,” has been observed evolving to circumvent sanctions and restrictions, solidifying its position as one of the most prolific exploiters of zero-day vulnerabilities targeting mobile devices, particularly Apple’s iOS. Recent investigations by Google’s Threat Analysis Group (TAG) have shed crucial light on the alarming sophistication of this new exploit chain, painting a stark picture of the advanced surveillance capabilities available to those willing to pay the price.
The Evolving Landscape of Mercenary Spyware and Zero-Day Exploits
The market for sophisticated surveillance technology, often referred to as “mercenary spyware,” operates in a largely opaque ecosystem. These tools are not typically deployed by nation-states for national security purposes, but rather sold to governments and other entities for purposes that can range from counter-terrorism to the suppression of dissent. Intellexa and its Predator spyware represent a significant player in this space. Their ability to consistently develop and deploy zero-day exploits – vulnerabilities unknown to the software vendor and thus unpatched – allows them to maintain a critical advantage.
What are Zero-Day Exploits and Why are They So Dangerous?
A “zero-day exploit” refers to a previously unknown security flaw in software or hardware for which no patch or fix currently exists. The term “zero-day” signifies that the developers have had “zero days” to address the vulnerability since its discovery. This makes them incredibly potent weapons in the arsenal of cybercriminals and, in this context, mercenary spyware vendors.
Undetected Entry: Because the vulnerability is unknown, security software, including antivirus and intrusion detection systems, is unlikely to recognize or block the initial exploit.
Bypassing Defenses: Standard security patches, which are designed to fix known vulnerabilities, are ineffective against zero-day exploits. Users who diligently update their software may still be at risk if the exploit targets a flaw that hasn’t yet been publicly disclosed or patched.
Silent Operation: Once an exploit is successful, the spyware can often operate in the background, collecting data without the user’s knowledge or consent.
The development of zero-day exploits requires a high level of technical expertise, often involving reverse engineering, deep understanding of software architecture, and creative problem-solving. The fact that companies like Intellexa can consistently produce and weaponize these vulnerabilities underscores the significant resources and talent they command.
Intellexa and the Predator Spyware: A Deep Dive
Intellexa, an Israeli-based company, has been under intense scrutiny for its role in providing surveillance tools to various regimes. The Predator spyware is their flagship product, designed for advanced mobile device infiltration. While the specifics of its capabilities are often kept under wraps to protect its operational effectiveness, past reports and the recent Google TAG analysis point to a comprehensive suite of surveillance functions.
Capabilities of Predator Spyware (based on available intelligence):
Data Extraction: Accessing call logs, messages (SMS, WhatsApp, Signal, etc.), emails, photos, videos, contacts, and calendar entries.
Real-time Monitoring: Capturing live audio from calls, eavesdropping on conversations through the microphone, and activating the device’s camera for covert video recording.
Location Tracking: Pinpointing the device’s geographical location with high accuracy.
Keystroke Logging: Recording every keystroke made on the device, capturing passwords and sensitive information.
Browser History and Activity: Monitoring web browsing habits and online activities.
The sophistication of Predator lies not just in its functionality but in its delivery mechanism. Intellexa has proven adept at crafting exploit chains that leverage multiple vulnerabilities in sequence, increasing the likelihood of successful infiltration and making it harder for security researchers to unravel the entire attack path.
The New iOS Zero-Day Exploit Chain: A Detailed Analysis
Google’s Threat Analysis Group (TAG) has been instrumental in exposing the sophisticated operations of state-sponsored and mercenary spyware actors. Their recent findings regarding Intellexa’s new iOS zero-day exploit chain provide an alarming glimpse into the current threat landscape. This chain represents a significant advancement in their ability to target Apple devices, which are generally considered to have robust security.
The Technical Breakthroughs: How the Exploit Works
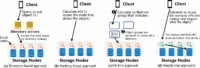
While the full technical details of the exploit chain are proprietary and closely guarded by Google and Apple for security reasons, the general principles outlined by TAG highlight the ingenuity of the attackers. The chain likely involves a series of vulnerabilities, each exploited in sequence to achieve the final objective: installing the Predator spyware and gaining persistent access to the device.
Hypothetical Stages of the Exploit Chain (based on common attack vectors):
1. Initial Access Vulnerability: This could be a flaw in how iOS handles web content (e.g., Safari browser rendering), image processing, or inter-app communication. Often, these vulnerabilities are triggered by the victim interacting with a malicious link or a specially crafted piece of data.
Example: A user might click on a phishing link that leads to a webpage designed to exploit a bug in the device’s web browser. This bug could allow the attackers to execute arbitrary code on the device.
2. Privilege Escalation Vulnerability: Once initial code execution is achieved, the attackers need to gain higher privileges to access more sensitive system resources and install persistent spyware. This involves exploiting another vulnerability that allows them to move from a limited user context to a more powerful system-level one.
Example: After gaining initial access, the attacker might exploit a kernel vulnerability. The kernel is the core of the operating system, and compromising it gives the spyware immense power over the device.
3. Persistence Mechanism: To ensure the spyware remains on the device even after reboots or after the initial exploit is no longer active, a persistence mechanism is crucial. This involves embedding the spyware in a way that it automatically restarts or reactivates when the device is turned on.
Example: The spyware might be disguised as a system process or inserted into legitimate application files, making it difficult to detect and remove.
The complexity of chaining multiple vulnerabilities together is significant. It requires meticulous planning and execution, as a single flaw in the chain can lead to the entire attack failing. Intellexa’s success in developing and deploying such chains indicates a dedicated and highly skilled offensive security team.
Targeting iOS: The Significance of Bypassing Apple’s Defenses
Apple has built a reputation for strong security, with its iOS operating system being a primary selling point for many users. Features like the App Store’s strict review process, sandboxing of applications, and robust encryption are designed to protect users from malware and unauthorized access. However, the consistent targeting of iOS by mercenary spyware vendors, including Intellexa, demonstrates that no platform is entirely impregnable.
Why is iOS a Prime Target?
Large and Influential User Base: Millions of high-profile individuals, including journalists, activists, politicians, and business leaders, use iPhones. Compromising these devices can yield valuable intelligence or disrupt critical communications.
Perceived Security: Many users assume their iPhones are inherently secure, leading to a potential complacency regarding cybersecurity threats.
High Value of Data: The data contained on an iPhone is often considered highly valuable due to the types of users who own them.
Intellexa’s ability to develop zero-day exploits for iOS is a testament to the ongoing arms race between security researchers and exploit developers. While Apple continuously works to identify and patch vulnerabilities, the discovery of new, unknown flaws by sophisticated actors like Intellexa presents a persistent challenge.
The Role of Sanctions and Restrictions
The international community has attempted to curb the activities of mercenary spyware vendors through sanctions and export controls. Intellexa, like many of its peers, has faced such restrictions. However, their ability to adapt and continue operations suggests that these measures, while important, may not be sufficient on their own.
Strategies for Evasion:
Corporate Restructuring: Companies might change their names, create shell corporations, or shift their operational bases to jurisdictions with less stringent regulations.
Supply Chain Diversification: Relying on a global network of suppliers and contractors can make it harder to trace the origin and ultimate destination of their tools.
Exploiting Legal Loopholes: Navigating international trade laws and regulations can be complex, and vendors may exploit ambiguities or gaps to continue their business.
Adapting Exploit Infrastructure: Shifting the technical infrastructure used for delivering exploits can also help evade detection.
The persistence of Intellexa despite international pressure highlights the difficulty in regulating the highly lucrative and secretive surveillance technology market.
Implications and Consequences: Who is at Risk?
The proliferation of advanced iOS zero-day exploits like those employed by Intellexa has far-reaching implications for individuals and society at large. The targets are not random; they are often individuals or groups whose communications and activities are of interest to the entities purchasing such spyware.
Targeted Individuals and Groups
The primary targets of mercenary spyware are typically those whose activities are deemed a threat or of high intelligence value. This includes:
Journalists: Exposing corruption, human rights abuses, or sensitive government information.
Human Rights Activists: Organizing protests, advocating for social change, or documenting abuses.
Political Dissidents: Opposing authoritarian regimes or advocating for democratic reforms.
Lawyers and Legal Professionals: Representing clients involved in sensitive cases.
Business Executives: Involved in competitive industries or sensitive negotiations.
Government Officials: Involved in policy-making, intelligence, or diplomatic activities.
The ability to conduct advanced surveillance on these individuals can have a chilling effect on free speech, press freedom, and democratic participation. The fear of being constantly monitored can deter people from speaking out or engaging in legitimate activism.
The Erosion of Privacy and Trust
The use of sophisticated spyware fundamentally erodes the concept of privacy. When personal devices can be infiltrated and monitored without consent or knowledge, the boundaries of private life become blurred. This can lead to a pervasive sense of insecurity and a decline in trust, not only in technology but also in the entities that wield such powerful surveillance tools.
Psychological Impact: The knowledge that one might be under constant surveillance can lead to anxiety, paranoia, and self-censorship.
Chilling Effect on Free Expression: Individuals may refrain from discussing sensitive topics or expressing dissenting opinions, fearing reprisal.
Undermining Democratic Processes: The ability to surveil political opponents or journalists can skew elections and suppress legitimate public discourse.
The Global Reach of Digital Espionage
The global nature of the internet and mobile communication means that such exploits can have a worldwide impact. Mercenary spyware vendors operate across borders, selling their tools to clients in various countries. This makes it challenging for any single nation to fully combat the threat.
Statistics and Trends:
While specific statistics on the deployment of zero-day exploits by mercenary groups are difficult to obtain due to their clandestine nature, reports from cybersecurity firms consistently show an increase in the use of advanced persistent threats (APTs) and sophisticated surveillanceware. The commercial spyware market is estimated to be worth billions of dollars annually, fueling further innovation and development in this sector.
Defending Against Advanced Surveillance: What Can Be Done?
While the threat posed by sophisticated zero-day exploits is significant, there are steps individuals and organizations can take to mitigate their risk. It’s an ongoing battle, and a multi-layered approach is essential.
For Individuals: Enhancing Personal Cybersecurity
Keep Devices Updated: Always install the latest iOS updates as soon as they are released. While zero-days are unknown, vendors like Apple work rapidly to patch vulnerabilities once discovered.
Be Wary of Links and Attachments: Exercise extreme caution with unsolicited messages, emails, or texts that contain links or attachments, even if they appear to be from trusted sources. Phishing attempts are a common vector for exploit delivery.
Use Strong, Unique Passwords and Two-Factor Authentication (2FA): While not directly preventing an exploit, these measures make it harder for attackers to gain access to your accounts if they do compromise your device or steal credentials.
Limit App Permissions: Regularly review app permissions and revoke access to sensitive data (like microphone, camera, location) if an app doesn’t genuinely need it.
Consider a Second Device: For highly sensitive communications, consider using a separate device dedicated to those conversations, with minimal apps installed and a very strict usage policy.
Stay Informed: Follow reputable cybersecurity news sources to stay aware of emerging threats and best practices.
For Organizations and Governments: A Proactive Stance
Implement Robust Security Policies: Develop and enforce comprehensive cybersecurity policies for all employees and devices.
Invest in Advanced Threat Detection: Utilize threat intelligence platforms and endpoint detection and response (EDR) solutions that can identify anomalous behavior indicative of an attack.
Employee Training: Conduct regular cybersecurity awareness training for all staff, focusing on recognizing phishing attempts and safe online practices.
Supply Chain Security: Scrutinize the security practices of third-party vendors and partners.
Advocacy and Regulation: Support efforts to increase transparency and accountability within the commercial spyware industry. Advocate for stronger international regulations and enforcement mechanisms.
Incident Response Planning: Have a well-defined incident response plan in place to swiftly address any security breaches.
Conclusion: The Unseen Battle for Digital Sovereignty
The revelation of Intellexa’s new iOS zero-day exploit chain is a stark reminder that the digital frontier is a constant battleground. While Apple invests heavily in securing its ecosystem, the ingenuity and resources of mercenary spyware vendors like Intellexa present an ever-evolving threat. The ability to circumvent cutting-edge security with unknown vulnerabilities allows for advanced surveillance that can silence journalists, activists, and dissidents, undermining fundamental rights and freedoms.
The implications are profound, extending beyond individual privacy to impact the very fabric of open societies. As these tools become more sophisticated and accessible to a wider range of actors, the need for vigilance, robust defense strategies, and greater accountability within the digital surveillance industry becomes increasingly critical. LegacyWire will continue to monitor these developments, striving to bring you the most important news that impacts our digital lives and the principles we hold dear. The shadow cast by these digital eavesdroppers requires our collective attention and a steadfast commitment to protecting our digital sovereignty.
—
Frequently Asked Questions (FAQ)
Q1: Is my iPhone truly vulnerable to advanced spyware like Predator?
A1: While iOS is generally considered very secure, no operating system is completely immune to sophisticated attacks. Zero-day exploits, like those developed by Intellexa, target previously unknown vulnerabilities. While Apple works diligently to patch these, the window of vulnerability before a patch is released can be exploited. Individuals who are high-profile targets (journalists, activists, political figures) are more likely to be targeted.
Q2: How do I know if my phone has been compromised by spyware?
A2: Detecting sophisticated spyware can be very difficult, as it’s designed to be stealthy. However, some potential signs include:
Unusual battery drain (spyware often runs in the background).
Increased data usage.
Strange noises or echoes during calls.
The device becoming unusually hot even when not in heavy use.
Unexpected reboots or slowdowns.
Seeing unfamiliar apps or processes.
However, these symptoms can also be caused by legitimate software issues, so they are not definitive proof of spyware. Professional forensic analysis is often required for certainty.
Q3: Can I prevent zero-day exploits from affecting my device?
A3: It’s nearly impossible to fully prevent zero-day exploits because they are, by definition, unknown. However, you can significantly reduce your risk by:
Keeping your iOS updated: This is the most crucial step. Apply updates as soon as they are available.
Being extremely cautious with links and attachments: Avoid clicking on suspicious links or downloading attachments from unknown senders.
Using strong security practices: This includes strong passwords and two-factor authentication.
Limiting app permissions: Be mindful of what access you grant to applications.
Q4: What is the difference between commercial spyware and government-sponsored malware?
A4: Both can be highly sophisticated and used for surveillance. “Commercial spyware” (like Intellexa’s Predator) is developed by private companies and sold to governments, law enforcement agencies, or even private entities. “Government-sponsored malware” is developed and deployed directly by state intelligence or military agencies for their own intelligence-gathering operations. The lines can blur as commercial vendors often have ties to or are utilized by governments.
Q5: What is Intellexa and what is Predator spyware?
A5: Intellexa is an Israeli-based company that develops and sells advanced surveillance technology, including “Predator” spyware. Predator is a potent tool designed to infiltrate mobile devices (like iPhones and Android phones) to extract data, monitor communications, and gain real-time access to the device’s camera and microphone. It has been identified as a tool used by various governments.
Q6: Are Apple’s security features enough to protect me?
A6: Apple’s security features are among the best available for mobile devices, making it a challenging target for attackers. However, the existence of sophisticated zero-day exploit chains highlights that even robust defenses can be bypassed with enough expertise and resources. Continuous vigilance, prompt software updates, and cautious user behavior are essential complements to Apple’s built-in security.


Leave a Comment