North Korea’s Cybercriminals Break Records with $2 Billion…
In 2025, North Korean state-backed cybercriminals shattered long-standing records by siphoning more than $2.02 billion in cryptocurrency across exchanges, wallets, and DeFi protocols. This colossal operation marks the most lucrative year on record for sanctioned digital theft, even as the total number of publicly confirmed attacks declined versus prior eras of crypto crime. Analysts describe a meticulously compartmentalized campaign that blended bridge exploits, phishing campaigns, and stealthy wallet breaches into a sweeping, high-value enterprise. The numbers for the year reflect not only raw theft, but a strategic push that leveraged evolving technologies and a global supply chain of illicit actors, money mules, and on-chain laundering networks.
The 2025 Heist: What Happened and Why It Stands Out
To appreciate the scale, consider that the $2.02B figure represents a sea change in the threat landscape. It is not simply about a few dramatic heists; it is about a sustained, multi-vector operation that targeted the most valuable nodes in the crypto ecosystem. The attackers prioritized cross-chain bridges and hot wallets holding large liquid reserves, exploiting operational gaps in bridge governance, validator oversight, and multi-signature management. Several high-profile breaches underscored the vulnerability of touchpoints that connect traditional finance to decentralized ecosystems, including centralized exchanges with substantial reserves, DeFi protocols with fragile governance models, and wallet services entrusted with user funds.
Scale, Victims, and Schemes
The victims spanned the globe, from regional exchanges in Asia to high-volume platforms in Europe and the Americas. The attackers didn’t just raid a single platform; they relocated funds across hundreds of addresses and multiple chains, complicating attribution and incident response. The majority of the loot was moved through a web of liquidity pools, cross-chain bridges, and over-the-counter (OTC) desks designed to obscure provenance. In hindsight, the campaigns combined three core tactics: first, exploiting cross-chain bridge mechanics to drain assets; second, compromising hot wallets and exchange hot pockets via phishing and credential theft; and third, employing sophisticated money-laundering channels that used mixer services, layering, and shell companies to obfuscate origin and ownership.
As this piece notes, the year’s headline figure is a product of both large single-bite breaches and a cascade of smaller, high-yield thefts that, when tallied, created a perception of unprecedented profitability for a state-backed cyber unit. The operational tempo resembled a fleet of coordinated strikes rather than a one-off incident. That pattern mirrors the broader reality: in an era of ever-expanding on-chain activity, sophisticated criminal groups are optimizing for value capture and operational resilience rather than sheer spectacle.
Timeline of Key Events
During the first quarter of 2025, early indicators pointed toward an intensification of bridge exploits following intensified development in bridge architectures and governance processes. By mid-year, multiple high-liquidity events had occurred in rapid succession, punctuated by a handful of major breaches that exposed both hot wallets and liquidity pools. The final months sealed the record, with analysts noting that attackers had matured their playbook—reducing detection windows, fragmenting funds into numerous addresses, and leveraging legitimate service providers to facilitate rapid cash outflows. In aggregate, these steps created a persistent threat posture that is unsurprising to researchers who track the Lazarus Group and other state-aligned actors. The numbers also reflect a broader shift: as traditional exchange security improves, attackers pivot toward protocol-layer entitlements and cross-chain exposure where the financial upside remains high even under scrutiny.
Who Is Behind It? The Lazarus Group and State-Sponsored Operations
Attribution in cybercrime remains a delicate art, but the consensus among top cybersecurity firms is that a North Korean state-backed unit, long associated with the Lazarus Group, orchestrated a significant portion of the 2025 caper. Researchers point to a continuity of personnel, tooling, and deployment patterns that align with prior Lazarus campaigns—though this year’s scale appears to reflect a broader coalition effort that may extend beyond a single group. The operation’s institutional quality—granular planning, compartmentalized roles, and a clear chain-of-command—suggests state sponsorship intended to fund the regime’s strategic objectives beyond conventional weaponization of cyber tools.
Historical Context
The Lazarus Group has a documented history of targeting financial infrastructure, with notable episodes in the DeFi space and traditional financial interfaces. Past campaigns highlighted a proficiency in spear-phishing, credential harvesting, and the exploitation of flawed cross-chain bridges or governance mechanisms. The 2025 campaign appears to refine these techniques, prioritizing speed and breadth while maintaining a lower profile during the initial infiltration phases to avoid early detection. This historical continuity strengthens the premise that state actors are not merely experimenting with new techniques but systematically building capabilities to exploit the most consequential choke points in the modern crypto economy.
Operational Tactics
Analysts describe a multi-layered approach: high-value target selection, initial foothold via phishing or slept-on vulnerabilities, rapid movement between wallets and chains, and finally, covert liquidity relocation and laundering. The blend of on-chain analytics, network forensics, and traditional intelligence gathering enabled attackers to stay ahead of defenders for longer than usual. The operation also relied on a robust ecosystem of compromised service providers, including credential-stuffing services, malware distributors, and laundering channels that obfuscated flow and ownership. The result is a complex, adaptive threat that requires equally sophisticated defense and intelligence sharing to counter.
How The Attack Unfolded: Methods and Mechanisms
The 2025 breach sequence illustrates how attackers exploit the weakest links in a rapidly expanding ecosystem: bridges that enable cross-chain value transfer, wallets that hold large holdings, and exchanges that balance user convenience with risk management. Each stage deployed a different set of tools and protocols, underscoring the necessity for layered security across systems, processes, and personnel.
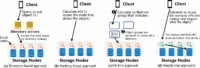
Bridge Exploitation
Cross-chain bridges function as essential infrastructure for liquidity and interoperability, yet they inherently introduce risk by translating tokens across networks with differing rules and security postures. The 2025 attacks heavily targeted bridge contracts and governance mechanisms, taking advantage of flawed upgrade processes, insufficient validator oversight, and weak access controls. Attackers forged unauthorized transactions, drained reserves, and then moved funds into a diversified network of addresses and liquidity pools to erode traceability. This pattern serves as a reminder that all bridges require rigorous formal verification, continuous auditing, and strict multi-party approval structures to minimize systemic risk.
Phishing and Credential Theft
Beyond technical exploits, a significant portion of the theft relied on social engineering—phishing campaigns, credential stuffing, and the subversion of legitimate user and staff accounts. Even with modern security measures, humans remain a critical vulnerability. Attackers used realistic impersonation, calls, and deepfake-like simulations to prompt legitimate-looking transactions, authorize withdrawals, or exfiltrate seed phrases. The outcome underscores the need for ongoing security awareness training, robust identity verification, and behavioral analytics to detect anomalous login or signing activity before funds move off hot wallets.
Malware, Wallet Breaches, and On-Chain Movement
On the technical side, attackers employed malware to harvest credentials, harvest session tokens, and harvest private keys stored in less-secure environments. Once access was established, they executed rapid transfers, distributing funds across many wallets to complicate tracing. The use of hot wallets for immediate liquidity contrasted with the need to preserve long-term value in more secure storages, creating a tiered risk posture where some funds were liquid with others reserved for longer-term laundering strategies. The result is a dynamic that keeps defenders guessing, as funds migrate across chains and through various intermediaries with increasing velocity.
Money Laundering and Attribution Challenges
Even when the theft is detected, tracing the flow of stolen assets is a nontrivial challenge. Attackers rely on layering, mixers, and shell entities to obscure provenance, and sophisticated techniques within the laundering pipeline complicate attribution for regulators and investigators. Blockchain analytics firms play a pivotal role in reverse-engineering flows, but the transparent nature of blockchains is a double-edged sword: it enables forensic clarity in many cases, while sophisticated criminal networks develop countermeasures to defeat shallow tracing. The 2025 campaign demonstrates how important cross-industry collaboration, advanced analytics, and international cooperation have become in turning the tide against high-value, state-sponsored thefts.
Immediate and Long-Term Impacts
The consequences of a record-breaking theft of this scale ripple through markets, platforms, and users. Exchanges may face liquidity shocks, withdrawal suspensions, and increased regulatory scrutiny, while users experience direct financial losses, decreased confidence, and heightened concern about the security of wallets and DeFi protocols they interact with daily. Beyond the immediate disruption, long-term effects include heightened risk awareness, stronger security standards, and shifts in how the crypto economy conceptualizes risk at protocol and ecosystem levels.
On Exchanges
Centralized exchanges confronted the need to reassess hot wallet security, multi-signature configurations, and the adequacy of ongoing risk monitoring. The attacks underscored the value of independent security audits, real-time anomaly detection, and robust incident response planning that can contain breaches and prevent rapid drain of user funds. In some cases, exchanges enacted enhanced withdrawal controls, stricter KYC protocols, and more aggressive collaboration with threat intelligence networks to identify and block suspicious activity before it escalates.
On DeFi Protocols
DeFi protocols faced amplified scrutiny for governance risks, vulnerability in bridge contracts, and the fragility of liquidity pools when confronted with large, sudden withdrawals. The year’s events accelerated discussions around formal security models, independent audits of bridge logic, formal verification of critical contracts, and the adoption of multi-party computation (MPC) or threshold signatures to reduce single points of failure. Protocol developers and auditors began prioritizing upgrades to bridge contracts and deploying safety nets such as circuit breakers to pause suspicious transactions during suspected attacks.
On Retail Investors
For everyday users, the specter of large-scale theft translates into a heightened need for best practices in personal security. The most common guidance focuses on never leaving large sums on hot wallets, diversifying storage across cold wallets and hardware wallets, enabling hardware-based authentication, and maintaining up-to-date firmware on devices involved in wallet management. Education and awareness campaigns became critical in helping the broader user base recognize phishing signs, avoid risky click patterns, and understand how to verify transaction details before signing approvals.
Temporal Context and Trends: 2020s in Perspective
Looking back across the last several years reveals a trajectory: while the number of publicly disclosed breaches may ebb and flow, the total value stolen has trended upward in aggregate as the crypto economy expands. The 2025 figure, while shocking, sits within a pattern where adversaries capitalize on growth phases—when liquidity is high and the cross-border nature of exchange activity is most active. In this context, 2024 saw a burst of educational and regulatory responses that aimed to harden bridges and wallets; 2025, in contrast, exposed gaps that can only be closed with coordinated industry action and smarter automation in threat detection. As the ecosystem matures, defenders must translate high-profile breaches into repeatable security improvements rather than one-off patchwork fixes.
Year-Over-Year Patterns
To contextualize the 51% YoY increase, analysts compare this year’s growth with multi-year trends in crypto crime. While global asset thefts fluctuated due to regulatory pressure and improved diligence by major platforms, the average value per incident rose for the most dramatic campaigns. The ratio of theft value to total on-chain activity grew, suggesting attackers are focusing on high-liquidity targets with significant on-chain footprints. The trend underscores a central paradox: as the legitimate crypto market expands, so too does the potential payoff for well-resourced threat actors, creating a persistent incentive for sophisticated campaigns to continue.
Cross-Border Enforcement and Forensics
Policy responses accelerated across major jurisdictions in 2025, with regulators enforcing stricter AML/KYC controls and requiring exchanges to share threat intelligence more openly. International cooperation intensified, and sanctions regimes expanded to cover more crypto-facilitating services, including mixers and opaque OTC desks. For investigators, the combination of on-chain analytics and cross-border cooperation proved crucial in identifying laundering networks, even when initial transaction paths appeared to be obfuscated. Sector-wide, the lesson remains clear: without continued investment in forensic capabilities and cross-agency collaboration, the window for sophisticated state-sponsored theft remains substantial.
Policy, Security, and Industry Response
The scale of the 2025 attack forced a reevaluation of security best practices across the crypto ecosystem. Governments, industry groups, and individual platforms began articulating a more unified approach to risk management, with emphasis on bridging security, wallet hardening, and standardized incident-response playbooks. The following sections summarize the key responses that emerged in the wake of the breach.
Regulatory Moves
Regulators in several jurisdictions signaled a tougher stance on crypto exchanges, bridges, and service providers that facilitate cross-chain activity. Enhanced reporting requirements, stricter licensing standards, and mandatory participation in threat intelligence coalitions became more common. Some authorities proposed standardized security frameworks that would govern bridge design, vault allocation, and the use of hardware security modules (HSMs) for critical signing operations. While these measures aim to reduce systemic risk, they also raise questions about regulatory clarity, operational costs, and the potential for overreach—especially for smaller, compliant players who already contend with a complex compliance burden.
Security Best Practices
Industry groups and leading platforms advanced a menu of security enhancements, including mandatory multi-signature schemes for hot wallets, time-delayed withdrawals, auditable on-chain governance, and real-time breach dashboards. Best practices also emphasized the deployment of secure enclave technologies, robust access controls, device-based authentication, and proactive monitoring for abnormal transactional patterns. A growing trend is the adoption of incident response exercises and tabletop drills that simulate a major cross-chain attack, enabling teams to refine playbooks and shorten detection-to-containment cycles.
Incident Response and Collaboration
Incident response workflows evolved from a primarily internal concern to a cooperative effort involving threat intel sharing, law enforcement liaison, and cross-platform collaboration. Information sharing is crucial when attackers leverage shared infrastructure or common laundering routes. Several industry bodies established formal channels for rapid disclosure of suspected breaches, enabling platforms to619 block suspicious accounts, retract compromised credentials, and reduce the risk of follow-on incidents. The overarching aim is to convert every major breach into a learning opportunity that strengthens the ecosystem rather than a standalone tragedy.
Defensive Playbook: What The Industry Can Do
In the face of a record-breaking year for state-backed crypto theft, practitioners must implement a robust, multi-layered defensive strategy. The following playbook outlines practical steps that platforms, wallets, and regulators can take to reduce exposure and shorten the attack cycle.
Technical Controls
Core technical measures include enforcing strong multi-signature requirements for governance and withdrawals, deploying hardware-secure environments for private keys, and integrating hardware wallets for cold storage. Regular, automated security audits of bridge contracts, upgrade processes, and ecosystem dependencies are essential. Continuous monitoring with anomaly detection engines, rigorous access management, and prompt patching of known vulnerabilities are non-negotiable in a high-risk environment. In addition, the use of formal verification for critical smart contracts, along with independent penetration testing, can dramatically reduce the probability and impact of exploits.
Operational and Governance Controls
Alongside technical safeguards, organizations should implement strict operational protocols for incident response. This includes clear roles and responsibilities, rapid decision-making trees, and predefined containment strategies for suspected breaches. Governance models must incorporate multi-party approval for significant actions, such as large transfers or bridge upgrades, to minimize the risk of unilateral, high-impact decisions. Regular red-teaming exercises should stress-test incident response, with post-incident reviews driving continuous improvement.
Threat Intelligence and Collaboration
Proactive threat intelligence becomes a competitive advantage in this environment. Platforms should participate in information-sharing consortia, subscribe to reputable threat intel feeds, and coordinate with law enforcement when breaches occur. Collaboration between major exchanges, wallet providers, and security researchers improves the speed and quality of attribution, enables faster blacklisting of compromised addresses, and supports more effective traceability of stolen funds across chains.
User Education and Awareness
Human factors remain a persistent vulnerability. Ongoing user education about phishing, credential hygiene, and safe signing practices is essential. Clear, user-friendly warnings about suspicious requests, transaction details, and the importance of confirming recipient addresses before approving transfers can reduce the success rate of social engineering campaigns. Public awareness campaigns, combined with accessible security tooling, empower users to be the first line of defense in the crypto economy.
Pros and Cons: A Risk-Balanced View
Pros for Criminal Actors
From an adversary’s perspective, the evolving crypto landscape presents few barriers to high-value theft when security controls lag behind financial incentives. The low friction of cross-border movement, the opacity of certain workflows, and the sophistication of money laundering channels create a favorable environment for large-scale theft. The record-breaking windfall of 2025 also signals strong potential returns for future operations, incentivizing continued investment in tooling and infrastructure that facilitate stealth and speed.
Cons and Costs for Defenders
For defenders, the record year exposes structural vulnerabilities and the costs of maintaining resilience. Security upgrades require substantial capital, specialized expertise, and ongoing vigilance. The industry bears the burden of responding to sophisticated phishing campaigns, bridge exploits, and the rapid evolution of laundering techniques. The societal costs include reputational damage, diminished user trust, and the risk that regulatory overhead could inadvertently hamper legitimate innovation. Yet, the long-term view is that the asymmetry has shifted toward a more mature security posture as lessons from 2025 drive concrete improvements.
Balanced Take
Despite the allure of large payouts for criminals, there is an inverse relationship between attacker success and ecosystem stability. Each major breach catalyzes improvements in security practices, policy frameworks, and international cooperation. The 2025 incident, while devastating, also accelerated the adoption of best practices that reduce risk for countless users, firms, and developers. The field remains dynamic, with ongoing investment in threat intelligence, secure architecture, and transparent reporting as the backbone of trust in the crypto economy.
Conclusion
The 2025 record-breaking crypto heist marks a watershed moment for the digital asset landscape. It underscores that even as the market grows and matures, it remains a target for well-resourced, highly organized adversaries. The attackers’ success is not merely a financial statistic; it is a wake-up call that highlights the necessity of layered security, rigorous governance, and international collaboration to safeguard users and institutions alike. For readers, the takeaway is clear: protect your assets with robust personal security practices, stay informed about evolving threat vectors, and support policy and industry efforts that harden the entire ecosystem against future onslaughts. As the title of this piece suggests, this is a pivotal moment in the ongoing evolution of cyber risk in the crypto era, and the first paragraph of this report sets the stage for the granular analysis that follows across H2 and H3 sections. The story is not just about loss; it is a catalyst for resilience, innovation, and shared responsibility across a rapidly growing digital economy.
FAQ
- Who is most likely behind the 2025 crypto heist?
- The prevailing view among security researchers points toward a North Korean state-backed unit, often associated with the Lazarus Group, leveraging a multi-team approach to target bridges, wallets, and liquidity pools. Attribution in cyberspace remains probabilistic, but the convergence of tooling, patterns, and infrastructure aligns with prior campaigns attributed to state-sponsored actors.
- How did the attackers manage to steal $2 billion?
- By combining bridge exploits, credential theft, and rapid on-chain movement, attackers drained liquidity from cross-chain interfaces and hot wallets, then laundered funds through layered networks. The efficiency of the operation hinged on high-value targets, minimal early detection, and the ability to fragment funds across dozens of addresses and chains to frustrate tracking efforts.
- Which platforms were affected the most?
- While the breach impacted multiple exchanges and DeFi protocols, bridges and wallets holding large sums were the primary targets. Centralized exchanges faced withdrawal suspensions and enhanced security scrutiny, while DeFi protocols confronted governance vulnerabilities and liquidity shocks that exposed fragile contract logic and risk controls.
- Is this the largest cryptocurrency theft in history?
- Yes, by reported value for a single calendar year, the 2025 operation outpaced prior incidents in scale and value. While there have been other significant breaches, the combination of cross-chain exploitation and sustained liquidity drain in 2025 set a new high-water mark for state-sponsored crypto theft.
- What can individual users do to protect themselves?
- Users should prioritize storing most funds in cold wallets or hardware wallets, enable hardware-backed authentication, practice strict seed phrase hygiene, avoid sharing sensitive information, verify recipient addresses before signing transactions, and stay alert to phishing attempts that imitate exchanges or support staff. Importantly, users should implement layered security and consider using wallets with robust anti-phishing protections and transaction verification features.
- What does this mean for the crypto industry going forward?
- Industry-wide action is likely to intensify: stronger multi-signature practices, formal verification and auditing of critical contracts, enhanced cross-chain governance controls, and greater collaboration among exchanges, wallet providers, and regulators. While challenges persist, the incident could accelerate the maturation of security standards and risk management practices, ultimately benefiting users and the broader ecosystem through safer design, more transparent incident reporting, and faster threat intelligence sharing.

Leave a Comment