Why Tax Season Is a Cybercriminal’s Goldmine
Tax filing periods worldwide are a magnet for cybercrime, and India is no exception. The convergence of high public engagement, time-sensitive actions, and the authoritative nature of tax authorities creates a psychological sweet spot for attackers. During these windows, individuals and finance teams are more likely to let their guard down when receiving what appears to be an official communication.
The Psychology of Urgency and Authority
Phishing lures succeed because they tap into deep-seated behavioral triggers. An email warning of a missed deadline or a pending refund plays on fear of penalty or anticipation of gain. When that message bears the logo and language of the Income Tax Department, it carries implied authority, reducing skepticism. For example, one recent campaign used subject lines like “Urgent: Your ITR Filing Requires Immediate Verification” to prompt hasty clicks.
Statistical Surge in Tax-Related Scams
According to the Indian Computer Emergency Response Team (CERT-In), phishing incidents related to financial and governmental services rose by nearly 63% in the first quarter of 2024 compared to the same period last year. Tax-themed scams accounted for over 40% of these, highlighting how sharply criminals are focusing on this sector. Globally, the trend mirrors this; the IRS in the United States reported a similar seasonal spike, confirming that this is a well-timed, not isolated, threat.
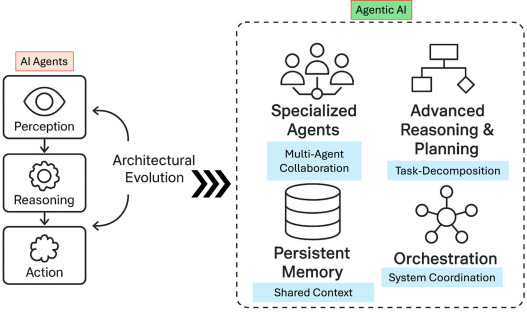
Deconstructing the Multi-Stage Malware Campaign
Unlike simple phishing emails that aim to harvest login credentials, these campaigns are far more insidious. They employ multi-stage malware, a layered approach that ensures persistence, evasion, and maximum damage.
Stage 1: The Lure and Initial Compromise
The attack begins with a highly targeted email, often sent to employees in finance or HR departments. These messages mimic official Income Tax Department notices, complete with forged sender addresses (e.g., noreply@incometaxindia.gov.in), authentic-looking logos, and language that mirrors government communication. Attachments might include:
- Fake ITR forms in PDF or Excel format
- Links to counterfeit e-filing portals
- “Secure” document download pages
Clicking the link or opening the attachment triggers the download of a first-stage payload, often a lightweight downloader script.
Stage 2: Establishing a Foothold
Once the downloader is executed, it contacts a command-and-control (C2) server to fetch additional malware components. This could include information stealers designed to plunder saved browser credentials, banking details, or sensitive documents. In several analyzed cases, attackers used modular malware that adapts based on the victim’s system—checking for antivirus software, virtual environments, or business applications before deploying next-stage tools.
Stage 3: Lateral Movement and Data Exfiltration
With access secured, attackers move laterally across the network, seeking valuable data—client databases, financial records, employee Personally Identifiable Information (PII), or intellectual property. Some campaigns have been found deploying ransomware as a final payload, encrypting files and demanding payment in cryptocurrency, turning a data theft incident into a operational crisis.
Real-World Impacts on Indian Businesses
The consequences of falling victim extend far beyond a simple security incident. For businesses, the fallout can be financial, reputational, and legal.
Financial and Operational Damage
Direct financial losses from fraud, ransomware payments, or regulatory fines can be devastating, especially for SMEs. Indirect costs include system downtime, IT forensic services, and increased insurance premiums. A mid-sized manufacturing firm in Pune recently reported a 72-hour shutdown after a tax-themed phishing email led to a ransomware infection, costing an estimated ₹2.3 crore in lost productivity and recovery.
Reputational Harm and Loss of Trust
When customer or employee data is breached, trust erodes rapidly. Clients may take their business elsewhere, and partners might reconsider agreements. In regulated industries, such as finance or healthcare, a data breach can also trigger mandatory disclosure laws, leading to public scrutiny and lasting brand damage.
Legal and Compliance Repercussions
India’s Digital Personal Data Protection Act, 2023 imposes strict requirements on data processors. A failure to secure sensitive information could result in significant penalties, alongside potential lawsuits from affected parties. Proving due diligence in cybersecurity practices is becoming a legal necessity, not just a best practice.
How to Defend Against Tax Phishing Attacks
Protection requires a multi-layered strategy combining technology, training, and vigilance.
Technological Safeguards
Implement advanced email filtering solutions that detect and quarantine phishing attempts. Use endpoint detection and response (EDR) tools to identify suspicious behavior early. Regularly update and patch all systems to close vulnerabilities that malware might exploit.
Employee Awareness and Training
Conduct simulated phishing exercises to teach staff how to recognize malicious emails. Encourage a culture where employees report suspicious messages without fear of blame. Regular training sessions—especially before peak seasons like tax filing—can significantly reduce click-through rates.
Incident Response Planning
Have a clear, tested incident response plan that outlines steps to take if a breach occurs. This should include isolation of affected systems, notification procedures, and engagement with cybersecurity experts and legal counsel.
Conclusion: Vigilance Is Non-Negotiable
As tax authorities digitize services and deadlines loom, cybercriminals will continue to refine their tactics. The multi-stage malware campaigns targeting India’s ITR filers are a stark reminder that in cybersecurity, complacency is the enemy. By understanding the threat landscape, investing in robust defenses, and fostering a culture of security awareness, businesses and individuals can navigate tax season without falling prey to these sophisticated schemes. The responsibility is collective; staying informed and proactive is the best refund you can secure this season.
Frequently Asked Questions (FAQ)
How can I verify if an income tax email is genuine?
Genuine emails from the Income Tax Department usually come from an official @incometaxindia.gov.in domain. Avoid clicking links in unsolicited emails; instead, log in directly to the official e-filing portal independently to check for notifications. Look for spelling errors, generic greetings, or urgent demands—these are common red flags.
What should I do if I accidentally clicked a phishing link?
Immediately disconnect your device from the internet to prevent further data transmission. Run a full antivirus scan, change all passwords—especially for email and banking—from a clean device, and monitor accounts for suspicious activity. If it’s a work device, inform your IT department right away.
Are small businesses really at risk, or only large corporations?
Small and medium businesses are often targeted precisely because they may have weaker security postures than large enterprises. Attackers see them as “low-hanging fruit.” In fact, over 60% of cyberattacks are aimed at SMEs, according to a recent report by the Global Cyber Alliance.
Can multi-stage malware be removed completely?
It depends on the depth of the infection. While antivirus software can remove many threats, deeply embedded malware may require professional incident response services to ensure complete eradication and to prevent reinfection. In severe cases, rebuilding systems from clean backups is the safest option.
How often do these tax phishing campaigns occur?
They are highly seasonal, peaking during tax filing deadlines (usually July-October for individuals, and varies for businesses). However, attackers run campaigns year-round, adjusting lures to align with other financial events or government announcements.

Leave a Comment