Charming Kitten Leak Exposes Key Operatives, Front Companies, and a Global Security Breach
Recently, a substantial leak has shed light on the covert operations of Charming Kitten, also known as APT35—a notorious cyber espionage group linked to Iran. The leak includes details about operational personnel, their salaries, front companies, and links to broader geopolitical activities. This information not only deepens our understanding of Iran’s cyber capabilities but also uncovers the scale of its global influence and strategic objectives. In this comprehensive analysis, we’ll explore the significance of these revelations, what they mean for international cybersecurity, and the lessons organizations should learn to bolster their defenses.
Understanding the Charming Kitten Operations
What is Charming Kitten? An Introduction
Charming Kitten is a clandestine Iranian cyber espionage group that has been active since at least the early 2010s. Known by various aliases such as APT35, the group primarily targets political dissidents, foreign governments, academic institutions, and media outlets worldwide. Their sophisticated phishing tactics, malware campaigns, and social engineering strategies make them one of the most persistent Iranian threat actors.
What sets Charming Kitten apart is their ability to blend cyber espionage with psychological operations, often tailoring attacks to exploit geopolitical tensions. Their operations have delved deep into information theft, reconnaissance, and influence campaigns, making them a formidable adversary in the digital realm.
Major Revelations from the Leak
Complete Salary Records of Operatives: Unveiling the Inner Circle
The leaked documents provide what is perhaps the most revealing aspect—full salary records of the group’s operatives. This data supplies insight into the organizational structure, roles, and resource allocation within Charming Kitten. For example, key personnel involved in spear-phishing campaigns or malware development are now identified with their compensation details, indicating how Iran invests in cyber capabilities.
This transparency challenges the myth of covert cyber groups operating in shadows. Knowing the financial backing and staffing levels exposes potential vulnerabilities and helps cybersecurity professionals understand the group’s capacities. For instance, higher salaries might correlate with more experienced hackers capable of deploying advanced malware strains or executing complex operations.
Expanded Surveillance Platform Capabilities
The leak also reveals significant enhancements in Charming Kitten’s surveillance infrastructure. They have developed or acquired advanced tools capable of intercepting communications, exploiting zero-day vulnerabilities, and deploying malware across diverse platforms. These capabilities enable broad monitoring of targets’ digital activities with unprecedented precision.
For example, the leaked data details new versions of malware tailored for different operating systems—Windows, macOS, Linux, and mobile devices—highlighting the group’s intent to cover as many communication channels as possible. This expansion signifies a strategic shift toward more comprehensive spying, which could threaten government officials, NGOs, and journalists globally.
A Classified 2004 Document Connecting Iran’s IAEA Materials to Targeted Assassinations
Perhaps the most shocking revelation involves a classified document from 2004 that links Iran’s obtaining of International Atomic Energy Agency (IAEA) inspection materials with Department 40’s alleged targeted assassination program. This document suggests that Iran may have used cyber espionage to facilitate physical operations—an indication of a disturbing convergence between cyber and kinetic warfare.
This connection emphasizes the evolving nature of modern espionage, where digital intelligence gathering can directly inform covert physical actions. Such insights compel global security agencies to rethink the boundaries of cyber-physical tactics and strengthen cross-domain intelligence sharing.
Implications of the Leak for Global Cybersecurity
Understanding the Threat Landscape
The detailed exposure of Charming Kitten’s operational staff, tools, and strategic links broadens our perspective on Iran’s cyber capabilities. It reveals a well-organized, well-funded operation capable of complex, multi-layered espionage activities supporting national security objectives.
Furthermore, the leak emphasizes the importance of threat intelligence sharing among nations and organizations. Real-time alerts about such leaks can help defense teams adapt their policies to counteract evolving tactics used by APT groups.
The Geopolitical Context
Iran’s cyber operations aim to influence political developments, steal sensitive data, and sometimes even target individuals for physical harm. The leak underscores Iran’s growing ambition to leverage cyber tools to achieve strategic goals beyond traditional military means. Countries with high-profile targets, such as Israel, the United States, and European nations, must be particularly vigilant.
Lessons for Organizations and Governments
Organizations should double down on cybersecurity protocols, focusing especially on phishing defense, malware detection, and internal threat monitoring. Governments need to invest in intelligence sharing and develop resilient cyber infrastructures to counteract sophisticated groups like Charming Kitten.
Pros and Cons of the Revealed Operations
Pros (from a strategic perspective)
- Gathering Critical Intelligence: The group’s ability to infiltrate high-value targets provides valuable insights into geopolitical developments.
- Potential Deterrent Effect: exposing their infrastructure may discourage future attacks.
- Enhanced Understanding of Cyber Warfare: The leak helps security professionals recognize emerging tactics and technologies.
Cons (for global security)
- Erosion of Operational Security: Leaks compromise the confidentiality of offensive cyber tools, making future operations riskier.
- Possible Retaliatory Actions: Iran or affiliated groups may escalate cyber and physical threats in response.
- Increased Cyber Threats: Knowledge of their capabilities can motivate other malicious actors to adopt similar tactics.
Looking Ahead: The Future of Iran’s Cyber Operations
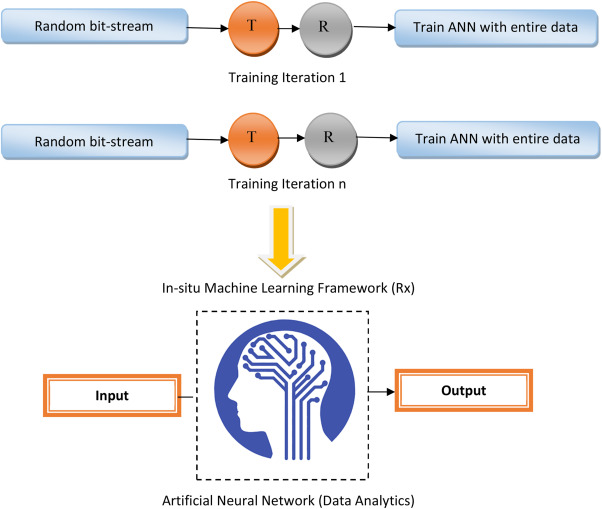
The leak signals a paradigm shift in understanding Iran’s cyber strategy. Expect continued sophistication, with possible expansion into new domains such as artificial intelligence and quantum computing. Iran’s tactical evolution underscores the need for proactive, adaptive defenses in the face of emerging threats.
Moreover, broader international cooperation is crucial to counter threats from state-sponsored groups. Sharing intelligence, enhancing cyber resilience, and establishing norms for responsible state behavior could mitigate the damage from future leaks or cyber-attacks.
Conclusion
The Charming Kitten leak has cast a spotlight on Iran’s cyber espionage prowess—exposing operational details, revealing financial backing, and even hinting at physical-world ambitions linked to cyber intelligence. As the cyber threat landscape continues to evolve rapidly, organizations and governments must learn from these revelations to prioritize security, resilience, and cooperation. By understanding the tactics, capabilities, and ambitions of groups like Charming Kitten, stakeholders can better prepare for the complex challenges ahead in safeguarding global stability and digital integrity.
Frequently Asked Questions
What are the main goals of Charming Kitten?
Charming Kitten primarily aims to conduct espionage, steal sensitive political and technological data, influence public opinion, and sometimes support Iran’s strategic and diplomatic interests worldwide.
How has the leak impacted global cybersecurity efforts?
The leak has provided invaluable insights into the operational structure of Charming Kitten, helping cybersecurity teams identify potential vulnerabilities and improve their defensive strategies against Iranian cyber threats.
Can other nation-states leverage this leak to improve their cyber defenses?
Absolutely. International security organizations and individual nations can analyze the leak to adapt their threat models, enhance threat detection protocols, and bolster resilience against similar cyber espionage campaigns.
Is Iran likely to escalate its cyber activities following this leak?
There is a possibility that Iran might double down on its cyber operations or even retaliate, emphasizing the need for heightened vigilance and proactive defense measures.
What steps should organizations take to protect themselves from similar threats?
Organizations should regularly update software, train employees on phishing awareness, implement multi-factor authentication, and develop robust incident response plans. Additionally, maintaining up-to-date threat intelligence can significantly reduce the risk of compromise.
In an era where cyber warfare blurs the lines between digital and physical domains, understanding who stands behind these operations and what their capabilities are becomes vital. The Charming Kitten leak is a wake-up call for all stakeholders committed to safeguarding their digital borders and national security.


Leave a Comment