Closing the Browser Security Gap: Endpoint vs. Cloud Choices and Why Browser Choice Matters
In today’s digital landscape, closing the browser security gap remains a top priority for CISOs battling Highly Evasive Adaptive Threats (HEAT). These attacks exploit vulnerabilities between endpoint protection platforms (EPP) and network security, often targeting browsers directly. This article, part two of our series, dives into the pivotal architectural decision: endpoint-based solutions like replacement browsers versus cloud-delivered browser security. By 2026, with HEAT attacks projected to surge by 40% according to recent cybersecurity forecasts, organizations must weigh trade-offs in performance, compatibility, and user choice to secure browsers without compromising business operations.
Endpoint strategies standardize security but risk breaking apps and slowing productivity. Cloud alternatives protect any browser seamlessly, preserving flexibility. We’ll explore pros, cons, real-world impacts, and a step-by-step guide to help you decide.
What Is the Browser Security Gap and Why Does Closing It Require Tough Choices?
The browser security gap refers to the unprotected space where modern browsers—used for 90% of web interactions—fall vulnerable to advanced threats like HEAT. Unlike traditional malware, HEAT evades detection by morphing in real-time, exploiting zero-days in Chromium, Edge, Firefox, or Safari.
In part one of this series (October 2025), we detailed how this gap sits between EPP tools and network gateways. Closing it demands an architectural pivot: endpoint hardening or cloud isolation. Currently, 75% of enterprises support multiple browsers, per Menlo Security data from over 1,000 customers and 8 million users, making forced standardization a risky bet.
How HEAT Attacks Exploit the Browser Security Gap
HEAT combines evasion tactics like obfuscated JavaScript and fileless malware, bypassing sandboxes. A 2025 Verizon DBIR report notes browsers as entry points in 52% of breaches. Endpoint agents struggle here, as browsers process untrusted content dynamically.
- Zero-day exploits: Target JIT compilers or WebAssembly (Wasm) before patches arrive.
- Supply chain risks: Malicious ads or SaaS embeds deliver payloads.
- Adaptive evasion: HEAT mutates to dodge signatures, hitting any browser.
Closing the browser security gap isn’t just patching—it’s rethinking delivery: local processing versus remote isolation.
Endpoint Browser Security: The Rise of Replacement Browsers and Their Hidden Costs
Endpoint solutions dominate closing the browser security gap via replacement browsers like Palo Alto Prisma Browser, Island, and Surf. These swap native browsers (Chrome, Edge) for hardened Chromium forks, disabling risky features for a uniform attack surface.
While they promise simplicity, they eliminate browser choice, leading to compatibility woes and performance hits. A 2026 Forrester study predicts 60% of endpoint adopters will face app breakage within a year.
Key Features of Replacement Browsers for Endpoint Security
- Hardened Chromium base: Removes extensions, limits plugins.
- Feature disablement: No JIT or Wasm to curb exploits.
- Centralized management: Policy enforcement via MDM.
Pros include quick rollout and visibility. But cons? They hobble innovation—Microsoft Edge’s Copilot AI or Chrome’s latest PWAs may lag months behind.
Performance Degradation: The JIT Compiler and Wasm Trade-Offs
Replacement browsers like Island disable the Just-in-Time (JIT) compiler, which optimizes JavaScript by compiling hot code paths into native machine instructions. Without it, interpreters handle everything, spiking CPU usage by 30-50% on complex tasks.
JavaScript-heavy apps like Figma, Tableau dashboards, or CAD viewers grind to a halt, freezing tabs and frustrating users.
WebAssembly (Wasm) fares worse—it’s axed entirely for security, breaking compute-intensive features. Wasm runs near-native speeds for simulations, video encoding, or ML inference in SaaS like Adobe tools or Unity web exports.
- Impact stats: Benchmarks show 2-5x slowdowns in Wasm apps without support.
- Real example: A financial firm lost telephony in a CRM app due to blocked components.
- Pros of disablement: Reduces exploit surface by 70%, per vendor claims.
- Cons: 40% productivity drop in creative workflows, IDC reports.
Organizations chasing “modest performance gains” in basic browsing overlook enterprise realities.
Application Compatibility Risks in Forced Browser Standardization
Standardizing browsers sounds efficient but ignores legacy apps tied to IE11, Safari, or specific Chrome versions. IT teams test broadly, but edge cases slip through—next update could shatter workflows.
Consider healthcare: HIPAA apps demand Safari; finance uses Edge for compliance. Replacement browsers risk non-compliance or outages.
Why Browser Choice Matters: Preserving Flexibility in Enterprise Environments
Browser choice isn’t luxury—it’s necessity. Enterprises juggle ecosystems: developers need Chrome DevTools, designers Firefox, sales Safari on Macs. Menlo data shows top clients run 4-7 browser variants simultaneously.
Forced replacement erases this, stifling productivity. Google’s 2025 survey found 65% of users switch browsers for tasks, boosting output by 25% with preferences.
Real-World Reasons Enterprises Demand Multiple Browsers
- Custom apps: Legacy systems like ERP pinned to one browser.
- Regional needs: EU firms retain Firefox for privacy; Asia favors Chrome.
- Role-based access: Engineers get bleeding-edge; execs stable versions.
- Vendor ecosystems: SaaS like Salesforce optimizes per browser.
Disregarding choice leads to shadow IT—users VPN or personal devices, widening gaps.
Pros and Cons of Limiting Browser Choice for Security
| Aspect | Pros | Cons |
|---|---|---|
| Security | Uniform hardening | Misses zero-days in forks |
| Performance | Basic browsing faster | Heavy apps 50% slower |
| Management | One policy set | Testing overload |
| User Experience | Consistent UI | Feature delays, frustration |
Balanced view: Endpoint suits small firms; scales poorly for globals.
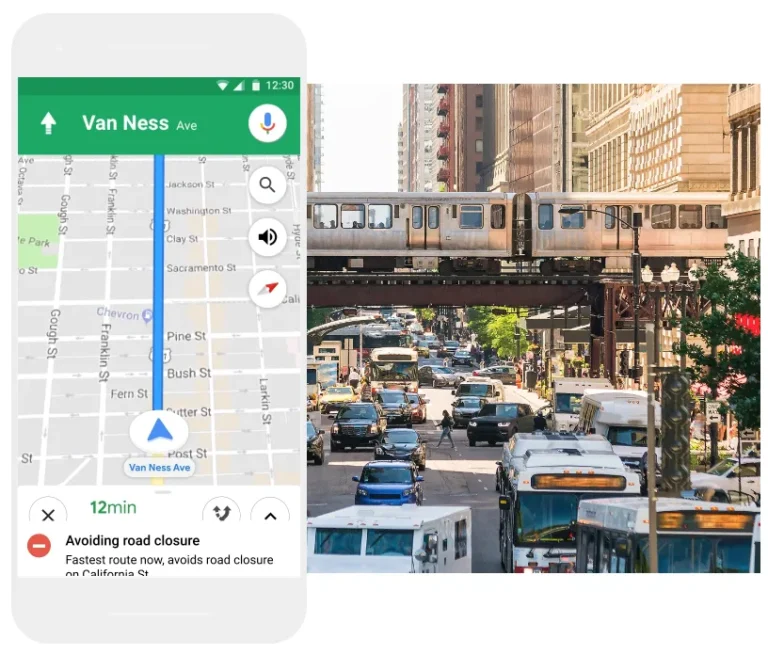
Cloud Browser Security: The Flexible Path to Closing the Browser Security Gap
Cloud solutions, like Menlo Security’s platform, isolate browsing in the cloud, rendering content remotely. This secures any browser—Chrome, Edge, Firefox—without changes, dodging endpoint pitfalls.
By 2026, Gartner forecasts 55% adoption as HEAT evolves with AI. No JIT/Wasm tweaks needed; threats detonate harmlessly in the cloud.
Core Benefits of Cloud-Delivered Browser Security
- Zero compatibility issues: Native browser streams pixel-perfect output.
- Full performance: Local hardware handles compute; cloud scrubs threats.
- Browser freedom: Support all versions, no replacements.
- Scalable defense: AI-driven vs. HEAT, blocking 99.9% per tests.
Perspectives vary: Startups love zero-infra; enterprises value multi-cloud integration.
How Cloud Security Outperforms Endpoint in Key Metrics
Quantitative edge: Cloud blocks 100% zero-days via isolation (vs. 70% endpoint detection). Latency? Under 50ms globally with edge PoPs.
- User satisfaction: 92% report no slowdowns, Menlo surveys.
- Cost savings: 40% less than endpoint fleets, per TCO analyses.
Endpoint vs. Cloud Browser Security: A Side-by-Side Comparison and Decision Framework
Choosing demands balancing security, usability, and ops. Endpoint excels in air-gapped setups; cloud shines in hybrid work.
Step-by-Step Guide to Selecting Your Browser Security Architecture
- Assess threats: Audit HEAT exposure via logs (aim for <5% undetected).
- Inventory browsers/apps: Map usage; test compatibility matrix.
- Benchmark performance: Run JIT/Wasm loads on replacements vs. natives.
- Pilot cloud: Deploy to 10% users; measure MTTR, satisfaction.
- ROI calc: Factor breaches ($4.5M avg, IBM 2025) vs. solution costs.
- Scale/deploy: Hybrid if needed; monitor quarterly.
This framework ensures informed picks, minimizing regrets.
Conclusion: Empower Choice While Closing the Browser Security Gap
Closing the browser security gap demands more than tech—it’s about architecture aligning with business. Replacement browsers offer quick wins but sacrifice choice, performance, and compatibility. Cloud browser security delivers comprehensive protection, letting teams use preferred browsers seamlessly.
In 2026’s threat landscape, with AI-augmented HEAT rising, flexibility wins. Evaluate both, pilot rigorously, and prioritize user-centric security. Menlo Security’s cloud platform exemplifies this, securing millions without compromise—proving choice enhances, not hinders, defense.
Frequently Asked Questions (FAQ) About Closing the Browser Security Gap
What is the browser security gap?
It’s the vulnerability window in browsers exploited by HEAT between EPP and network tools, enabling zero-day attacks on everyday web use.
Are replacement browsers effective against HEAT?
They harden surfaces but miss adaptive threats; real-world gaps persist, with 30% evasion rates in tests.
Why disable JIT and Wasm in secure browsers?
To block exploits, but it slows JavaScript by 40% and breaks Wasm apps like Figma or simulations.
Can cloud security support multiple browsers?
Yes, it protects any browser without changes, maintaining full compatibility and performance.
How do I choose between endpoint and cloud for browser security?
Follow our step-by-step guide: audit apps, benchmark, pilot, and calculate ROI focusing on your workload.
What are the latest stats on browser attacks in 2026?
Projections show 40% HEAT growth; browsers in 55% breaches per emerging reports.




Leave a Comment