Comcast Settles for $1.5 Million Over FCC Investigation Related to Vendor Data Breach
Comcast has reached a settlement of $1.5 million with the Federal Communications Commission (FCC) in response to a significant data breach involving a third-party vendor. This breach compromised the personal information of hundreds of thousands of customers, raising serious concerns about the security protocols surrounding customer data when managed by external entities. The incident, which originated with a vendor named Financial, has sparked discussions about the vulnerabilities associated with outsourcing data management.
Understanding the Data Breach Incident
The data breach that led to Comcast’s settlement was not an isolated event but rather part of a growing trend where third-party vendors become the weak link in data security. In this case, the breach exposed sensitive information, including names, addresses, and potentially financial details of customers. Such incidents highlight the critical need for robust security measures when companies rely on external vendors to handle customer data.
What Happened During the Breach?
In 2026, it was revealed that the breach occurred due to inadequate security practices at the vendor’s facilities. The compromised data was not only sensitive but also extensive, affecting a significant portion of Comcast’s customer base. The FCC’s investigation uncovered that the vendor failed to implement necessary safeguards, which ultimately led to the exposure of customer information.
Impact on Customers and Comcast
The fallout from this breach has been substantial. Customers affected by the data exposure faced potential risks, including identity theft and fraud. For Comcast, the financial implications were immediate, culminating in the $1.5 million settlement. This incident serves as a reminder of the importance of data security and the potential repercussions when companies fail to protect customer information.
Why Did the FCC Get Involved?
The FCC’s involvement was prompted by the need to ensure that telecommunications companies adhere to strict data protection regulations. The commission’s investigation aimed to assess whether Comcast had taken adequate steps to safeguard customer data and whether the company had fulfilled its obligations under federal law.
Regulatory Framework and Compliance
Currently, telecommunications companies are required to comply with various regulations designed to protect consumer data. The FCC’s actions in this case underscore the importance of compliance and the potential consequences of failing to meet these standards. Companies must not only protect their own systems but also ensure that their vendors are equally vigilant in safeguarding sensitive information.
Vendor Management and Data Security Best Practices
To prevent similar incidents in the future, companies must adopt comprehensive vendor management strategies. Here are some best practices to consider:
- Conduct Thorough Risk Assessments: Evaluate the security measures of potential vendors before entering into contracts.
- Implement Strong Data Protection Policies: Ensure that vendors adhere to strict data protection protocols.
- Regular Audits and Monitoring: Conduct periodic audits of vendor security practices to identify vulnerabilities.
- Establish Clear Communication Channels: Maintain open lines of communication with vendors regarding data security issues.
- Train Employees: Educate employees about the importance of data security and the role of third-party vendors.
Pros and Cons of Outsourcing Data Management
Outsourcing data management can offer several advantages, but it also comes with its own set of challenges. Here’s a breakdown of the pros and cons:
Advantages
- Cost Efficiency: Outsourcing can reduce operational costs associated with data management.
- Access to Expertise: Vendors often have specialized knowledge and resources that can enhance data security.
- Focus on Core Business: Companies can concentrate on their primary operations while leaving data management to experts.
Disadvantages
- Loss of Control: Companies may have less oversight over how their data is managed.
- Increased Risk: Relying on third parties can introduce vulnerabilities if the vendor’s security measures are inadequate.
- Reputational Damage: Data breaches can harm a company’s reputation, even if the breach originated with a vendor.
Current Trends in Data Security and Vendor Management
The latest research indicates that businesses are increasingly prioritizing data security in their vendor management strategies. In 2026, many organizations are adopting advanced technologies such as artificial intelligence and machine learning to enhance their security measures. These technologies can help identify potential threats and vulnerabilities in real-time, allowing companies to respond swiftly to any issues.
Emerging Technologies in Data Protection
Several emerging technologies are shaping the future of data protection:
- Artificial Intelligence: AI can analyze vast amounts of data to detect anomalies and potential breaches.
- Blockchain: This technology offers a decentralized approach to data management, enhancing security and transparency.
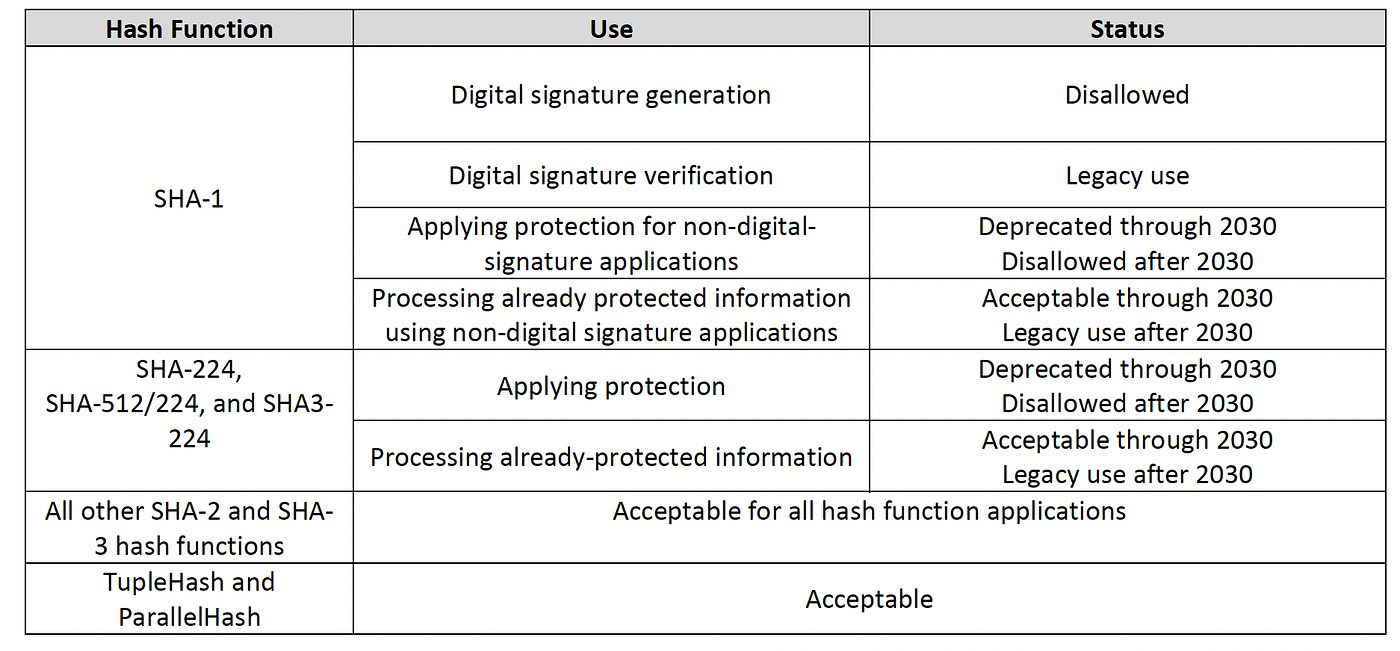
- Encryption Advances: New encryption methods are being developed to protect sensitive data both at rest and in transit.
Frequently Asked Questions (FAQ)
What was the reason for Comcast’s $1.5 million settlement?
The settlement was a result of a data breach at a third-party vendor that exposed the personal information of many Comcast customers, prompting an FCC investigation.
How can companies protect themselves from vendor-related data breaches?
Companies can protect themselves by conducting thorough risk assessments, implementing strong data protection policies, and regularly auditing their vendors’ security practices.
What are the consequences of a data breach for companies?
Consequences can include financial penalties, reputational damage, and potential legal action from affected customers.
Why is vendor management important for data security?
Effective vendor management ensures that third-party companies adhere to the same data protection standards as the primary organization, reducing the risk of data breaches.
What trends are shaping the future of data security?
Current trends include the adoption of AI and machine learning for threat detection, the use of blockchain for secure data management, and advancements in encryption technologies.
In conclusion, the Comcast data breach serves as a critical reminder of the importance of data security in today’s interconnected world. As companies increasingly rely on third-party vendors, they must prioritize robust security measures to protect sensitive customer information and maintain trust in their services.

Leave a Comment