Evilginx Attack Campaigns: A Deep Dive into Session Cookie Theft and MFA Bypass
Security researchers are issuing urgent warnings about a rising wave of cyberattacks leveraging Evilginx, an attacker-in-the-middle (MitM) phishing toolkit that intercepts login flows to steal session cookies and circumvent multi-factor authentication (MFA) protections. The threat is particularly acute within educational institutions, where attackers are demonstrating alarming success rates. Evilginx operates with surgical precision by positioning itself between a user and a legitimate website, effectively impersonating the target and capturing sensitive credentials. This sophisticated attack vector is proving remarkably effective, highlighting vulnerabilities in even seemingly secure systems and demanding immediate attention from security professionals and end-users alike. The increasing prevalence of these campaigns underscores a critical shift in attacker tactics, moving beyond simple credential harvesting to exploit session management and bypass established security layers.
Understanding Evilginx: The Attacker’s Toolkit
Evilginx isn’t a new tool; it’s been around for several years. However, its recent resurgence and adaptation to bypass modern security measures, particularly MFA, have made it a significant threat. Developed by a threat actor known as StarRoot, Evilginx is a powerful and versatile framework designed to facilitate advanced phishing attacks. It’s more than just a simple phishing page; it’s a complete ecosystem for credential theft and session hijacking. Unlike traditional phishing attacks that rely on tricking users into entering their credentials directly on a fake website, Evilginx intercepts the authentication process itself, allowing attackers to steal session cookies and gain unauthorized access to user accounts.
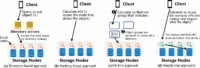
How Evilginx Works: A Step-by-Step Breakdown
- Initial Phishing Stage: The attack begins with a targeted phishing email or SMS message designed to lure victims to a malicious website. This website is often a near-perfect replica of a legitimate login page (e.g., Microsoft, Google, a university portal).
- MitM Interception: When a user enters their credentials on the fake login page, Evilginx intercepts the request. It then dynamically generates a legitimate login page for the target website, effectively acting as a man-in-the-middle.
- Session Cookie Theft: After the user successfully authenticates on the dynamically generated page, Evilginx steals the session cookie. This cookie is a small piece of data that allows the attacker to impersonate the user without needing their username or password.
- MFA Bypass: This is where Evilginx truly shines. Because the attacker now possesses the session cookie, they can use it to access the user’s account without triggering the MFA challenge. The session cookie effectively validates the user’s identity to the server.
- Account Takeover: With access to the session cookie, the attacker can seamlessly log in to the user’s account and perform actions as if they were the legitimate user.
Key Features of Evilginx
- Dynamic Login Page Generation: Automatically creates a legitimate login page based on the target website, making it harder for users to detect the attack.
- Session Cookie Theft: The core functionality – stealing session cookies to bypass authentication.
- MFA Bypass Capabilities: Exploits session cookies to circumvent multi-factor authentication.
- Customizable Phishing Templates: Allows attackers to create highly targeted and convincing phishing pages.
- Proxy Support: Can operate through proxies to obfuscate the attacker’s location.
- Data Exfiltration: Provides mechanisms for attackers to exfiltrate stolen data.
The Rise of Evilginx Campaigns: Recent Trends and Targets
While Evilginx has been around for a while, recent campaigns have demonstrated a significant increase in sophistication and targeting. The focus on educational institutions is particularly concerning, as these organizations often hold sensitive student and faculty data. The success rate in these campaigns is alarming, suggesting that current security measures are not always sufficient to protect against this type of attack. According to recent reports from cybersecurity firms like Proofpoint and CrowdStrike, Evilginx campaigns have been observed targeting universities in North America and Europe, with attackers seeking access to student records, financial information, and research data.
Targeting Educational Institutions: Why the Focus?
Several factors contribute to the attractiveness of educational institutions as targets:
- Large User Base: Universities have a large and diverse user base, increasing the potential for successful attacks.
- Sensitive Data: They hold a wealth of sensitive data, including student records, financial information, and research data.
- Often Under-Resourced Security Teams: Compared to large corporations, universities often have smaller and less well-resourced security teams.
- Complex IT Environments: University IT environments can be complex and difficult to secure, providing attackers with more opportunities to exploit vulnerabilities.
Recent Campaign Examples
Several high-profile Evilginx campaigns have been reported recently:
- University of Washington (2023): A sophisticated Evilginx campaign targeted the University of Washington, resulting in the theft of sensitive student data.
- Multiple UK Universities (2024): Reports indicate ongoing campaigns targeting several UK universities, with attackers focusing on stealing login credentials and financial information.
- Targeted Attacks on Faculty and Staff: Attackers are increasingly targeting faculty and staff members with access to more sensitive data and systems.
Mitigation Strategies: Protecting Against Evilginx Attacks
Defending against Evilginx attacks requires a layered approach that addresses both technical vulnerabilities and user awareness. Simply relying on MFA alone is no longer sufficient, as Evilginx effectively bypasses this security measure. Organizations need to implement a combination of technical controls and user education to effectively mitigate the risk.
Technical Controls
- Implement Web Application Firewalls (WAFs): WAFs can help detect and block malicious traffic, including Evilginx attacks.
- Monitor Network Traffic for Anomalies: Look for unusual traffic patterns that may indicate a MitM attack.
- Implement Strong Session Management Policies: Use short session timeouts and regularly rotate session cookies.
- Implement Browser Isolation: Isolate web browsing activity in a secure container to prevent attackers from stealing session cookies.
- Use Endpoint Detection and Response (EDR) Solutions: EDR solutions can detect and respond to malicious activity on endpoints.
- Implement Certificate Pinning: This helps prevent attackers from using fraudulent SSL/TLS certificates.
User Awareness Training
- Educate Users About Phishing Attacks: Train users to recognize and avoid phishing emails and websites.
- Emphasize the Importance of Verifying Website URLs: Users should always verify the URL of a website before entering their credentials.
- Promote the Use of Password Managers: Password managers can help users create and store strong, unique passwords.
- Regular Security Awareness Testing: Conduct simulated phishing attacks to test user awareness and identify areas for improvement.
The Future of Evilginx and the Evolving Threat Landscape
The Evilginx toolkit is likely to continue evolving, with attackers developing new techniques to bypass security measures. The increasing sophistication of phishing attacks, coupled with the widespread adoption of MFA, makes it crucial for organizations to stay ahead of the curve. We can expect to see attackers leveraging AI and machine learning to create even more convincing phishing campaigns and automate the exploitation process. The rise of Evilginx highlights the need for a proactive and adaptive security posture, one that continuously monitors for new threats and adapts to the evolving threat landscape. Furthermore, the increasing availability of these tools on the dark web lowers the barrier to entry for less sophisticated attackers, potentially leading to a wider range of Evilginx-based attacks.
Frequently Asked Questions (FAQ)
What is the difference between Evilginx and traditional phishing? Evilginx is a more sophisticated form of phishing that intercepts the authentication process itself, allowing attackers to steal session cookies and bypass MFA. Traditional phishing relies on tricking users into entering their credentials directly on a fake website.
Is MFA completely useless against Evilginx? No, MFA is still a valuable security measure, but it’s not a silver bullet. Evilginx can bypass MFA by stealing session cookies, which effectively validate the user’s identity to the server.
How can I tell if I’ve been targeted by an Evilginx attack? It can be difficult to detect an Evilginx attack. However, you may notice unusual activity in your online accounts, such as unauthorized logins or changes to your settings.
What should I do if I suspect I’ve been targeted by an Evilginx attack? Immediately change your passwords for all of your online accounts, and contact your organization’s IT security team.
What are the legal implications of using Evilginx? Using Evilginx for malicious purposes is illegal and can result in severe penalties.
What are the key statistics regarding Evilginx attacks? While precise figures are difficult to obtain, reports indicate a significant increase in Evilginx campaigns over the past year, with educational institutions being a primary target. Success rates are reported to be alarmingly high, often exceeding 50% in targeted campaigns.
What is StarRoot? StarRoot is the threat actor believed to be responsible for developing and distributing the Evilginx toolkit. Their motives and affiliations remain largely unknown.
Disclaimer: This article is for informational purposes only and should not be considered professional security advice. Always consult with a qualified security professional for guidance on protecting your organization from cyber threats.


Leave a Comment