Exploiting Trust: How Cybercriminals Manipulate Remote Monitoring Tools for Attacks
In the evolving landscape of cybersecurity, the misuse of Remote Monitoring and Management (RMM) tools has emerged as a significant threat. Cybercriminals are increasingly weaponizing these trusted IT resources, such as Atera and ConnectWise, to bypass security measures and maintain persistent access to systems. This article delves into the mechanics of these attacks, the groups involved, and the strategies organizations can employ to mitigate these risks.
The Growing Threat of RMM Tool Exploitation
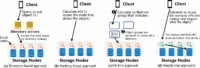
Currently, attackers are leveraging legitimate RMM tools to execute sophisticated cyberattacks. These tools, designed for IT support and management, are often overlooked by traditional security systems due to their trusted status. This exploitation poses a severe risk, as it allows attackers to operate undetected while masquerading as legitimate IT activities.
Understanding the Problem
The core issue lies in the inherent trust associated with RMM tools. Because these applications are digitally signed and recognized as legitimate software, they are not flagged by detection mechanisms such as Endpoint Detection and Response (EDR) systems or local replacement browsers. Attackers exploit this trust by using the RMM’s console and native system commands, such as PowerShell, to carry out their malicious activities without raising alarms.
High-Value Targets for Cybercriminals
Several notorious groups have adopted this technique, including:
- MuddyWater: An advanced persistent threat (APT) group linked to Iranian state-sponsored activities.
- Qilin: A ransomware gang known for its aggressive tactics.
These groups utilize RMM tools to establish a foothold within targeted organizations, enabling them to execute further exploits, including data theft and ransomware deployment.
The Attack Chain: How RMM Exploitation Occurs
The attack process typically begins with one of the following methods:
- Email Phishing: Attackers may use mass or spear-phishing campaigns to trick users into revealing credentials or downloading malicious attachments.
- Exploiting Vulnerabilities: Cybercriminals may take advantage of unpatched vulnerabilities within RMM tools, such as Authenticode Stuffing or Evilconwi, to gain unauthorized access.
Once inside, the RMM tool acts as a covert backdoor, allowing attackers to maintain persistent access to the network. This access can lead to the sale of initial access to other malicious actors, deployment of ransomware, and execution of various critical exploits.
The Consequences of RMM Misuse
The ramifications of RMM tool exploitation are severe. Organizations may face:
- Data breaches resulting in sensitive information exposure.
- Financial losses due to ransomware payments and recovery efforts.
- Reputational damage that can affect customer trust and business relationships.
Mitigating the Risks: How Menlo Security Addresses RMM Exploitation
Menlo Security has developed innovative solutions to combat the misuse of RMM tools. Their approach highlights the limitations of traditional detection-based security systems, such as EDR and antivirus software, which often fail to identify these sophisticated attacks.
Menlo HEAT Shield AI: A Game Changer
Menlo’s HEAT Shield AI, powered by Google Gemini, offers a proactive defense mechanism. Unlike conventional systems that rely on signatures and indicators of compromise (IoCs), this advanced technology employs multimodal reasoning to analyze both visual and structural elements of web pages. This capability allows it to:
- Instantly block social engineering attacks before they can execute.
- Cut off the attack chain before the trusted tool is launched.
By focusing on the intent behind actions rather than merely identifying known threats, Menlo Security provides a robust defense against the exploitation of RMM tools.
The RMM Misuse Playbook: How Attackers Operate
Understanding the tactics employed by cybercriminals is crucial for organizations aiming to protect themselves. Here are key strategies attackers use when leveraging RMM tools:
1. Utilizing Trusted Software
Attackers often begin by using legitimate RMM tools as a first-stage payload. Since these tools are trusted and digitally signed, they do not trigger malware alerts. This allows attackers to execute commands without immediate detection.
2. Running Native Commands
Instead of installing external malicious software, attackers utilize the RMM’s console to run native commands like PowerShell or net.exe. This approach mimics the behavior of a systems administrator performing routine maintenance, further obscuring their malicious intent.
3. Leveraging Encrypted Protocols
RMM tools typically communicate using standard, often encrypted protocols. This makes it challenging for security systems to differentiate between legitimate and malicious activities, allowing attackers to operate under the radar.
Identifying Specific Groups and Their Techniques
Several groups have been identified as frequent users of RMM exploitation techniques:
MuddyWater
This Iranian APT group has been linked to various cyberattacks utilizing RMM tools. Their operations often involve sophisticated phishing campaigns and exploitation of unpatched vulnerabilities.
Qilin
Known for its aggressive ransomware tactics, Qilin has also been observed using RMM tools to gain unauthorized access to networks, leading to significant data breaches.
Best Practices for Organizations to Protect Against RMM Exploitation
To safeguard against the misuse of RMM tools, organizations should consider implementing the following best practices:
1. Regular Software Updates
Ensure that all RMM tools and associated software are regularly updated to patch known vulnerabilities. This reduces the risk of exploitation by cybercriminals.
2. Employee Training
Conduct regular training sessions to educate employees about phishing tactics and the importance of verifying the legitimacy of requests for sensitive information.
3. Implement Multi-Factor Authentication (MFA)
Utilizing MFA can add an additional layer of security, making it more difficult for attackers to gain unauthorized access even if they obtain user credentials.
4. Monitor Network Activity
Establish robust monitoring systems to detect unusual activity associated with RMM tools. This can help identify potential breaches before they escalate.
5. Employ Advanced Security Solutions
Consider investing in advanced security solutions, such as Menlo Security’s HEAT Shield AI, which can provide proactive defenses against sophisticated attacks.
Conclusion: The Importance of Vigilance in Cybersecurity
As cyber threats continue to evolve, organizations must remain vigilant in their cybersecurity efforts. The exploitation of RMM tools represents a significant challenge, but with the right strategies and technologies in place, it is possible to mitigate these risks effectively. By understanding the tactics employed by cybercriminals and implementing robust security measures, organizations can protect themselves from becoming victims of these sophisticated attacks.
Frequently Asked Questions (FAQ)
What are RMM tools?
Remote Monitoring and Management (RMM) tools are software applications that allow IT professionals to manage and monitor systems remotely. They are designed to facilitate efficient IT support and maintenance.
How do attackers exploit RMM tools?
Attackers exploit RMM tools by using them as trusted software to gain unauthorized access to networks. They execute commands through the RMM console, making their activities appear legitimate.
What are the risks associated with RMM tool exploitation?
The risks include data breaches, financial losses due to ransomware, and reputational damage to organizations.
How can organizations protect themselves from RMM exploitation?
Organizations can protect themselves by regularly updating software, training employees, implementing multi-factor authentication, monitoring network activity, and employing advanced security solutions.
What is Menlo Security’s HEAT Shield AI?
Menlo Security’s HEAT Shield AI is an advanced security solution that uses multimodal reasoning to analyze web page elements and block social engineering attacks before they can execute.


Leave a Comment