The Domain Name System (DNS) is essential for translating domain names into IP addresses to connect users to websites. Among its data types, DNS TXT records are designed to hold text information but have recently become a covert channel for hackers to hide and deliver malware. Instead of using traditional file hosting, attackers fragment malicious files—like executables—into small parts and encode them in DNS TXT records.
This method is difficult to detect because DNS traffic is often trusted and less scrutinized than other data flows. The malware can remain hidden within DNS records until the records expire or are overwritten, allowing persistent, decentralized storage. This approach poses serious challenges for cybersecurity teams, as standard malware scans typically don’t inspect DNS data for suspicious content. Understanding how malware exploits DNS TXT records is vital for developing more effective network defenses.
Understanding DNS TXT Records and Their Legitimate Uses
DNS TXT records were originally created to store human-readable text within the Domain Name System. They provide a flexible way for domain owners to attach arbitrary text information to a domain. This versatility has made TXT records valuable for a variety of legitimate tasks in managing and securing online assets.
What Are DNS TXT Records?
TXT records are DNS entries that hold text data associated with a domain name. Unlike A or AAAA records, which map domain names to IP addresses, TXT records can contain any text string limited by size constraints. Network administrators use these records to publish data such as verification codes, network policies, or cryptographic keys.
Common Legitimate Uses of TXT Records
Several important internet standards rely on DNS TXT records for validation and security:
- SPF (Sender Policy Framework): TXT records specify which mail servers are authorized to send emails on behalf of a domain. This helps reduce email spoofing and phishing.
- DKIM (DomainKeys Identified Mail): Public cryptographic keys for verifying signed emails are published in TXT records.
- DMARC (Domain-based Message Authentication, Reporting & Conformance): Domains publish policies to instruct email receivers how to handle unauthenticated mail.
- Domain Verification: Services like Google, Microsoft, and others ask domain owners to add TXT records for ownership verification.
- Network Configuration: Some systems use TXT records to distribute configuration parameters or service metadata.
These examples highlight the critical role TXT records play in securing email communication and enabling domain-based identity verification.
How TXT Records Deliver Data
At their core, TXT records store small strings of text. When queried, DNS servers return those strings to clients. Since DNS operates on a distributed global scale with widespread caching, TXT records can quickly propagate information worldwide.
The structure allows for multiple TXT strings per record or multiple TXT records per domain, accommodating different needs or protocols simultaneously. However, size limits on DNS responses keep TXT records relatively small, encouraging the use of multiple records to store larger data.
Why Understanding Legitimate Use Matters
Recognizing the legitimate uses of TXT records sets the foundation for spotting misuse. Because TXT records can hold any text, attackers exploit them to hide or transfer data covertly. Knowing what typical TXT records look like—for example, SPF or DKIM records—helps identify anomalies that might indicate hidden malware or data fragments stored in DNS records.
This knowledge is essential in assessing potential DNS-based threats and understanding when a TXT record might be carrying something out of the ordinary.
Understanding the basics of DNS TXT records and their accepted purposes helps ground further discussions on how attackers abuse this flexibility to sneak malicious files into DNS infrastructure. This section lays the groundwork for seeing beyond standard uses and identifying suspicious activity.
Techniques for Hiding Malware in DNS TXT Records
Hackers use clever methods to hide malware inside DNS TXT records, turning a system meant for text information into a secret vault for malicious files. Understanding these techniques is key to spotting and stopping this kind of threat. Attackers convert files into an encoded format and spread them across DNS records so they can be retrieved later without raising suspicion.
File Partitioning and Hexadecimal Encoding in DNS
Malware authors start by breaking their files into smaller pieces. Since DNS TXT records have size limits, attackers divide a file, such as an executable (.exe), into manageable chunks. Each chunk is then converted from its original binary form into a hexadecimal string. This transformation allows the file data to be stored as plain text inside TXT records.
To keep everything in order, hackers use iterated subdomains, assigning each fragment a number or sequence value in the subdomain itself. For example, subdomains might be named 1.example.com, 2.example.com, and so on, each holding a different piece of the file in their TXT records. When these are queried in sequence, the original file can be reconstructed by converting the hex strings back into binary and joining the fragments.
This method works like a puzzle, where each subdomain holds a piece, and the order is tracked through the naming convention. Until the DNS server clears or overwrites these records, the file stays “hidden” in plain sight, dispersed across the DNS infrastructure.
Real-World Examples of Malware in DNS TXT Records
Security researchers have documented cases of this technique in the wild. Between 2021 and 2022, several DNS TXT records were discovered containing fragments of executable files. These records started with the “magic bytes” of a Windows executable file header, a telltale sign that an .exe file was being stored.
One notable case involved domains under felix.stf.whitetreecollective[.]com. Researchers found hundreds of subdomains named with incrementing integers. Each subdomain’s TXT record held a fragment of an executable in hexadecimal form. The consistent subdomain pattern made it clear that the attackers were using DNS to fragment and store a malicious .exe file systematically.
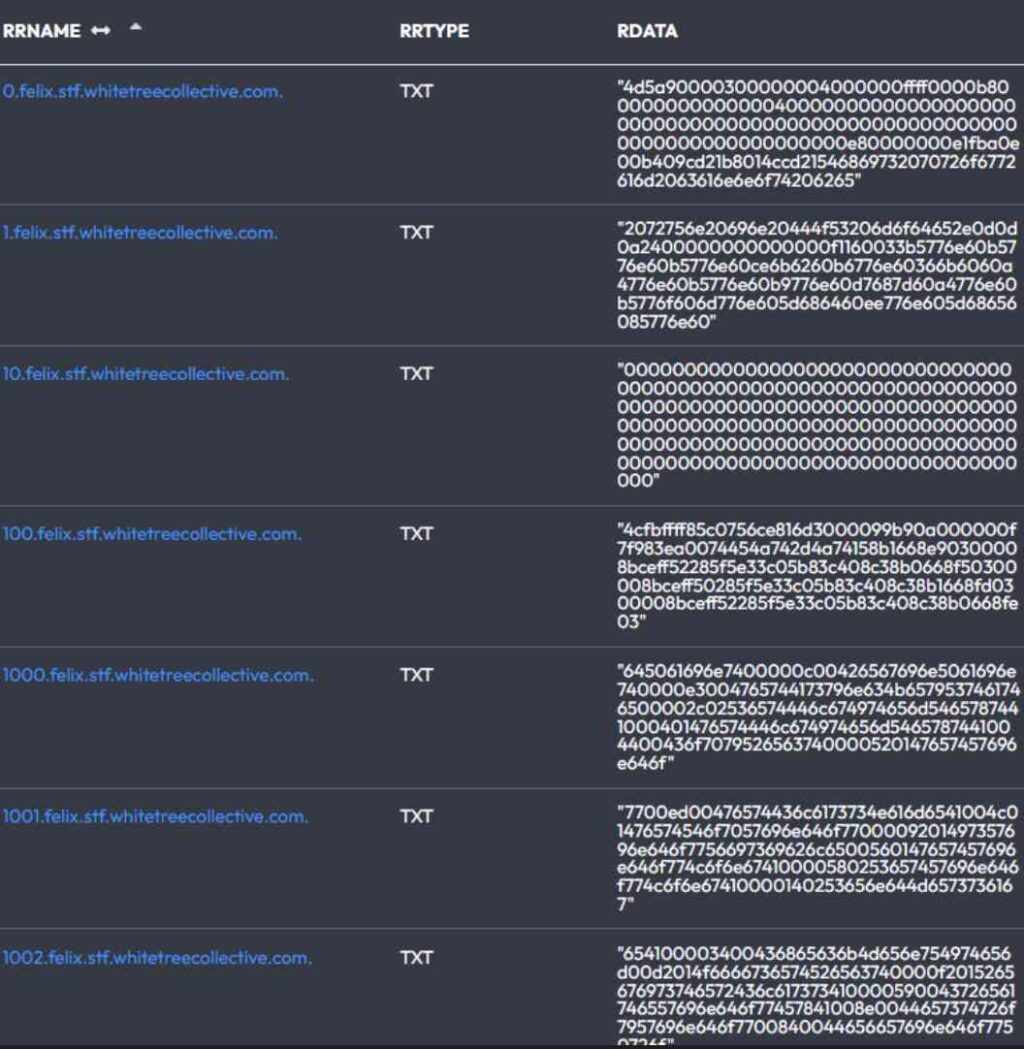
Across multiple domains, the same executable header was present, showing that this was a repeated tactic, not an isolated incident. This approach makes detection difficult because traditional security tools rarely inspect DNS TXT records for such payloads.
Photo by Mikhail Nilov
The use of DNS TXT records as a covert storage space for malware fragments opens up a new front in malware detection and prevention. It is critical for defenders to recognize these patterns and apply DNS traffic analysis techniques that go beyond traditional network security measures.
Security Risks and Challenges in Detecting DNS TXT Record Malware
The use of DNS TXT records to hide malware creates serious security risks that are hard to detect. Because DNS traffic is essential for internet functioning, it often goes unchecked, giving attackers a hiding place for malicious files. This covert approach allows malware to persist quietly in DNS infrastructure, posing a challenge for defenders who rely on traditional network security tools.
Persistent and Hard-to-Detect Storage
One key risk is the persistent nature of malware stored in DNS TXT records. Since files are broken into small fragments and stored as hexadecimal strings across multiple subdomains, the malicious payload can remain accessible for as long as the DNS records exist. This method resembles hiding pieces of a puzzle scattered across a landscape only a few know how to piece back together.
Unlike files on a server that can be scanned or deleted, DNS records are often overlooked in security sweeps. As a result, malware hidden in TXT records can evade detection for extended periods, especially if security teams do not analyze DNS traffic deeply.
Fragmentation and Encoding Hide Behavior
Attackers split executable files into many small chunks encoded in hexadecimal and spread them across various DNS TXT records. This fragmentation makes it difficult for standard detection tools to recognize the presence of malware. Each TXT record looks like random text, which blends with legitimate DNS data.
The use of iterated subdomains, often numbered sequentially, helps organize fragments but also adds complexity for defenders. Reconstructing the original file requires collecting all fragments in the right order, a process typically outside the scope of conventional threat detection.
DNS TXT Records Are Overlooked by Traditional Security Tools
Most network security systems focus on monitoring HTTP, FTP, or email traffic, while DNS requests and responses are considered low risk and get less scrutiny. This gap creates a blind spot where malware can hide effectively.
Furthermore, signature-based antivirus or intrusion detection systems rarely scan DNS TXT records for executable file headers or unusual data patterns. Since attackers use well-known file magic numbers (like .exe headers) encoded in DNS, new detection methods need to be applied that understand this behavior inside DNS traffic.
High Volume and Legitimate Use Obscure Malicious Activity
DNS TXT records serve multiple legitimate purposes, including email security protocols and domain verification. The high volume of normal TXT queries generates a noisy background that makes spotting suspicious payloads even harder. Security teams face the challenge of distinguishing between harmless TXT records and those that carry malicious files.
This problem is amplified when attackers mimic legitimate subdomain patterns or blend malware fragments with normal DNS text data, increasing the chance that their activity remains undetected.
Challenges in Response and Remediation
Once malware is discovered in DNS TXT records, removing it can be complicated. Attackers may control multiple domains and subdomains, requiring extensive coordination with domain administrators and DNS providers to purge malicious records. DNS caching further delays the removal effect, allowing malware fragments to persist in networks even after cleanup efforts begin.
The distributed and decentralized nature of DNS infrastructure means that traditional containment strategies do not apply straightforwardly, making response times longer and mitigation more difficult.
Understanding these risks and detection challenges is crucial for improving defenses against malware hidden in DNS TXT records. Security teams must adopt specialized tools and techniques focused on DNS traffic analysis to identify suspicious patterns and prevent attackers from exploiting the DNS system as a covert storage channel.
Protective Measures and Best Practices to Counter DNS-based Malware
The increase in malware hidden within DNS TXT records demands a clear and focused defense approach. Since attackers exploit DNS infrastructure to store and deliver harmful files, organizations must adopt strategies that extend beyond traditional security tools. Protecting your network means monitoring DNS traffic more carefully, improving detection capabilities, and managing DNS configurations wisely. The following sections outline practical steps to reduce the risk of DNS-based malware and strengthen your overall security posture.
Strengthen DNS Traffic Monitoring and Analysis
Standard security systems often overlook DNS traffic or treat it as safe, but this creates a vulnerability. Monitoring DNS requests and responses in depth helps catch suspicious patterns associated with malware fragments stored in TXT records. Key practices include:
- Implement DNS logging: Collect detailed logs of DNS queries and responses for later analysis.
- Use pattern recognition: Detect unusual DNS TXT records, such as those containing hexadecimal strings or executable file headers, which could indicate malware.
- Track subdomain activity: Watch for domains with many iterated or sequential subdomains, a sign of file fragmentation across DNS.
- Leverage DNS threat intelligence: Incorporate external threat feeds that identify malicious domains or unusual DNS behavior.
Adopting these measures helps uncover hidden malware and supports faster incident response.
Apply DNS Security Extensions and Controls
Securing the DNS environment itself reduces the chances of attackers adding or manipulating DNS TXT records for malicious purposes. Essential controls include:
- DNSSEC (Domain Name System Security Extensions): Enables validation of DNS data authenticity and integrity to prevent spoofing and unauthorized record changes.
- Access restrictions: Limit who can modify DNS records to trusted administrators only.
- Regular audits: Periodically review DNS zone files to verify that all TXT records serve legitimate purposes and remove outdated or suspicious entries.
- Use split DNS setups: Separate internal and external DNS traffic to reduce exposure of sensitive records.
These steps harden DNS infrastructure and limit attackers’ ability to exploit it for malware storage.
Employ DNS Firewalling and Filtering Solutions
DNS firewalls act as a gatekeeper, blocking access to known malicious domains or preventing suspicious DNS responses. Effective DNS filtering can disrupt malware retrieval via DNS TXT records before harm occurs:
- Block suspicious domains: Use DNS filtering services to deny queries to domains known for hosting malware or unusual DNS TXT records.
- Set response size limits: Limit DNS response sizes to reduce the feasibility of large file fragments being sent.
- Disable unnecessary TXT records: Remove TXT records that are no longer needed to reduce attack surface.
- Integrate with endpoint protection: Coordinate DNS filtering with endpoint security to identify and isolate infected devices attempting to fetch malware via DNS.
DNS firewalling provides an additional security layer to stop attacks early.
Educate Teams and Update Incident Response Plans
DNS-based malware is still a relatively new challenge, so awareness and preparation are essential. Security teams need to understand how malware hides in DNS TXT records and develop plans to respond effectively:
- Train analysts: Teach security staff to recognize suspicious DNS patterns and investigate anomalies in DNS traffic.
- Update detection tools: Ensure SIEM systems and threat hunting tools can support DNS TXT record inspection and file reconstruction when needed.
- Establish clear protocols: Define steps for containment, remediation, and recovery if DNS-based malware is found.
- Coordinate with DNS providers: Maintain relationships with DNS registrars and hosting providers for quick cooperation in removing malicious DNS records.
Prepared and informed teams reduce the time attackers have to operate undetected.
Maintain Good DNS Hygiene and Domain Management
Finally, ongoing DNS management practices help limit risks:
- Use strong authentication: Protect DNS management interfaces with multi-factor authentication.
- Regularly rotate DNS records: Refresh TXT and other DNS records to reduce persistence of malware fragments.
- Monitor domain registrations: Watch for suspicious domain patterns or new registrations that mimic your assets or known malicious infrastructure.
- Limit recursive DNS: Configure DNS servers to restrict recursive queries to trusted clients only.
Good hygiene keeps your DNS environment clean and less attractive for abuse.

Photo by picjumbo.com
By combining these protective measures, organizations can reduce the risk that malware hidden in DNS TXT records will evade detection and persist. Strengthening DNS monitoring, securing DNS infrastructure, and educating security teams form the foundation of a solid defense against this emerging threat.
Conclusion
Malware hidden in DNS TXT records represents a sophisticated threat that exploits a trusted part of internet infrastructure. By fragmenting malicious files and encoding them in DNS TXT records, attackers create persistent, hard-to-detect payloads that evade traditional security tools. This method challenges defenders to rethink their approach to DNS traffic monitoring and incorporate specialized techniques for identifying unusual patterns in DNS data.
Staying vigilant against this form of attack requires continuous updates to detection systems and strict DNS management practices. Organizations that enhance DNS logging, apply access controls, and educate security teams will be better positioned to spot and stop malware in DNS records. Protecting DNS infrastructure is essential to maintaining a secure network environment as attackers find new ways to misuse it.



Leave a Comment