New .NET AOT Malware Campaign Uses Black Box Evasion to Steal Data
Cybersecurity researchers at Howler Cell have uncovered a sophisticated new malware campaign that weaponizes a legitimate .NET development feature to become nearly invisible to conventional security defenses. The threat leverages .NET Ahead-of-Time (AOT) compilation to strip away the digital fingerprints that antivirus and endpoint detection systems rely on, effectively turning malicious code into an opaque black box. This isn’t just another piece of malware; it’s a masterclass in evasion, featuring a multi-stage attack chain and a clever, adaptive scoring system designed to distinguish between real victims and security researchers’ sandboxes.
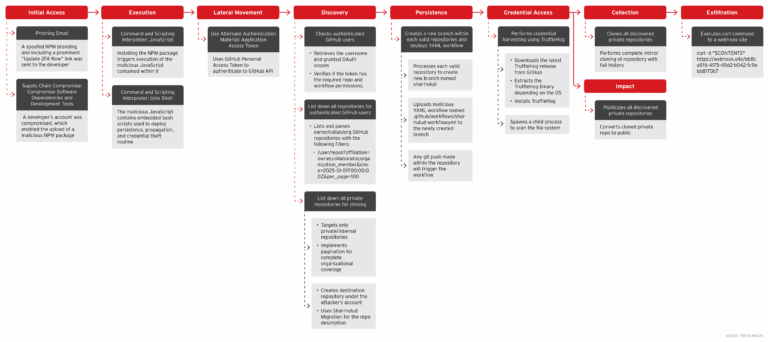
The Attack Chain: From Phishing to Payload
The campaign begins, as many do, with a phishing email containing a malicious link. When an unsuspecting user clicks the link, they download a ZIP archive. At first glance, the archive appears benign, containing several legitimate-looking modules that are likely stolen or repurposed from genuine software. This tactic is meant to lower the victim’s guard and bypass initial email security filters that scan for known malicious filenames.
The true threat is hidden within: an executable named KeyAuth.exe. This file acts as the initial downloader. Once executed, it silently retrieves a second-stage payload from a command-and-control server, saving it as bound_build.exe. This second-stage file is the core orchestrator of the entire attack. It first decrypts two additional embedded threats using a simple XOR cipher. The first, Crypted_build.exe, is a loader for the Rhadamanthys infostealer—a notorious piece of malware designed to harvest credentials, cookies, cryptocurrency wallets, and other sensitive data from browsers and applications. The second, Miner.exe, ultimately installs a component named MicrosoftEdgeUpdater. This is a deceptive disguise; it’s not a legitimate updater but a loader for the XMRig cryptocurrency miner, which will hijack the victim’s CPU/GPU resources to mine Monero for the attackers.
The Malware’s Adaptive Defense: A Scoring System for Sandbox Detection
What elevates this campaign from clever to concerning is the bound_build.exe loader’s built-in environmental assessment. Before deploying its final payloads, it runs a diagnostic check to determine if it’s executing on a real user’s machine or within an automated security sandbox. It employs a points-based scoring system, evaluating several system characteristics:
- System RAM: Awards points if the system has more than 8GB of RAM, as sandboxes often have limited resources.
- System Uptime: Checks how long the system has been running. A freshly booted sandbox is a red flag.
- User Activity: Counts the number of files in the user’s Documents folder. More than ten files suggests a real user.
- Antivirus Presence: Scans for common security processes like WinDefend or Kaspersky. Their presence can lower the score.
If the final score falls below a threshold of 5 points, the malware assumes it’s being monitored and simply shuts itself down to avoid detection. This dynamic behavior makes it particularly challenging for automated analysis tools to capture and understand the threat.
Breaking Through the Black Box
Despite these sophisticated evasion techniques, the team at Howler Cell managed to dissect the malware’s inner workings. They employed a tool called Binary Ninja, which allowed them to create a custom WARP signature to reconstruct the program’s behavior. “WARP eliminated the need to manually inspect almost 4,000 library functions,” the researchers noted in their analysis. This approach was crucial because the AOT compilation had removed the typical metadata that security tools use to understand what code is doing, forcing analysts to work at a much lower, more complex level.
The Broader Implications of AOT Malware
This campaign represents a significant evolution in malware tactics. By leveraging .NET AOT compilation, attackers can create binaries that are not only smaller and faster but also far more resistant to static analysis. Traditional security tools that rely on inspecting the structure and metadata of .NET assemblies are left blind. This forces a shift toward more resource-intensive dynamic analysis and behavioral monitoring, which can be slower and less effective at scale.
The use of a scoring system for sandbox evasion is also a growing trend. It demonstrates that attackers are investing in making their malware “smart” enough to avoid the very environments designed to catch it. This cat-and-mouse game means that security teams must constantly adapt their detection strategies, often relying on a combination of advanced heuristics, machine learning, and human expertise to stay ahead.
Protecting Against Advanced AOT Malware
For organizations and individuals, defending against this type of threat requires a multi-layered security approach. First and foremost, user education is critical. Since the attack chain begins with a phishing email, training users to recognize suspicious links and attachments is a vital first line of defense. Email security gateways that can detect and quarantine malicious ZIP files or executable attachments are also essential.
On the technical side, traditional signature-based antivirus may not be sufficient. Security solutions that incorporate behavioral analysis, anomaly detection, and machine learning can help identify malicious activity even when the code itself is obfuscated. Network monitoring for unusual outbound connections to known command-and-control servers can also provide an early warning. Finally, keeping all software, including the operating system and applications, up to date with the latest security patches helps close the vulnerabilities that malware often exploits.
Conclusion
The .NET AOT malware campaign discovered by Howler Cell is a stark reminder of how attackers are constantly refining their techniques to evade detection. By combining legitimate development practices with intelligent evasion tactics, they’ve created a threat that is both effective and difficult to analyze. As malware becomes more adaptive and its authors more sophisticated, the cybersecurity community must continue to innovate, developing new tools and strategies to protect users in an increasingly complex threat landscape.
FAQ
What is .NET AOT compilation and why does it help malware hide?
.NET Ahead-of-Time (AOT) compilation converts .NET code directly into native machine code before execution, rather than using the common language runtime (CLR) to compile it on the fly. This process removes the metadata and intermediate language that security tools typically use to analyze and


Leave a Comment