Smart Home Security: Understanding Vulnerabilities and Protection Strategies
Welcome back, aspiring cyberwarriors!
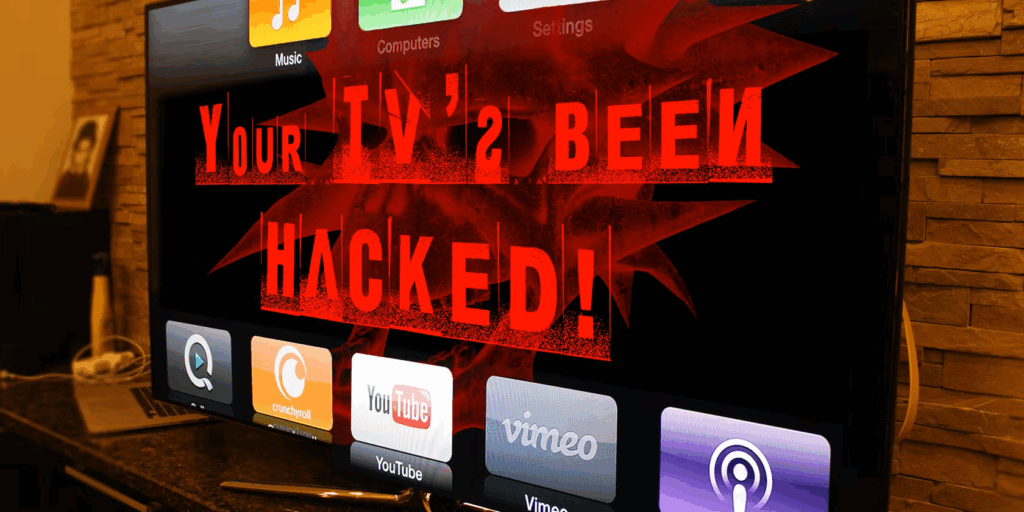
In today’s digital landscape, smart homes are becoming increasingly prevalent. These interconnected devices, while offering convenience and efficiency, have also emerged as prime targets for cybercriminals. The primary reason for this vulnerability lies in their often inadequate security measures. In 2025, the number of attacks on connected devices surged by an astonishing 400%, with the average cost of a data breach reaching $5.4 million. This alarming trend highlights the urgent need for awareness and education regarding smart home security.
Over the course of this comprehensive three-day workshop, we will delve into the various security weaknesses associated with smart home devices and the protocols that govern them. Our goal is to equip participants with the knowledge necessary to identify vulnerabilities and implement effective security measures.
Course Outline
- Introduction to Smart Home Devices
- Understanding Weak Authentication in Smart Home Devices
- RFID Technology and Smart Home Security
- Bluetooth and Bluetooth Low Energy Vulnerabilities
- Wi-Fi Security Risks and Exploitation
- LoRa Technology Vulnerabilities
- IP Camera Security Flaws
- Zigbee Protocol Vulnerabilities
- Wireless Technology Jamming in Smart Homes
- Exploiting IoT Devices to Access Personal Computers
- Strategies for Securing Your Smart Home
This workshop is part of our Subscriber Pro training package.
Understanding Smart Home Devices
Smart home devices encompass a wide range of technologies designed to enhance convenience and efficiency in our daily lives. These include smart speakers, thermostats, security cameras, and lighting systems, all of which can be controlled remotely via smartphones or voice commands. However, the very features that make these devices appealing also introduce significant security risks.
What Makes Smart Home Devices Vulnerable?
Several factors contribute to the vulnerability of smart home devices:
- Weak Default Passwords: Many devices come with factory-set passwords that are easy to guess or find online.
- Inadequate Software Updates: Manufacturers often neglect to provide timely updates, leaving devices exposed to known vulnerabilities.
- Insufficient Encryption: Data transmitted between devices and their control apps may not be adequately encrypted, making it easier for attackers to intercept.
- Limited User Awareness: Many users lack knowledge about securing their devices, leading to poor security practices.
Weak Authentication on Smart Home Devices
Authentication is a critical aspect of smart home security. Weak authentication methods can allow unauthorized users to gain access to devices and networks.
Common Authentication Issues
Some prevalent authentication issues include:
- Use of Simple Passwords: Users often choose easily guessable passwords, making it simple for attackers to breach accounts.
- Lack of Two-Factor Authentication: Many devices do not support two-factor authentication, which adds an extra layer of security.
- Inconsistent Authentication Protocols: Different devices may use varying authentication methods, complicating security efforts.
RFID Technology and Smart Home Security
Radio Frequency Identification (RFID) technology is commonly used in smart home devices for access control and automation. While convenient, RFID systems can be susceptible to various attacks.
RFID Vulnerabilities
Some of the vulnerabilities associated with RFID technology include:
- Eavesdropping: Attackers can intercept RFID signals to gain unauthorized access.
- Relay Attacks: Attackers can use relay devices to extend the range of RFID signals, allowing them to bypass security measures.
- Cloning: RFID tags can be cloned, enabling unauthorized duplication of access credentials.
Bluetooth and Bluetooth Low Energy Vulnerabilities
Bluetooth technology, particularly Bluetooth Low Energy (BLE), is widely used in smart home devices for communication. However, it is not without its security flaws.
Bluetooth Vulnerabilities
Key vulnerabilities associated with Bluetooth include:
- Bluejacking: Sending unsolicited messages to nearby Bluetooth devices.
- Bluesnarfing: Unauthorized access to information on a Bluetooth-enabled device.
- Bluetooth Spoofing: Attackers can impersonate legitimate devices to gain access to networks.
Wi-Fi Security Risks and Exploitation
Wi-Fi networks are integral to the functionality of smart home devices. However, they can also be a significant point of vulnerability.
Common Wi-Fi Vulnerabilities
Some common Wi-Fi security risks include:
- Weak Encryption Protocols: Using outdated encryption methods like WEP can expose networks to attacks.
- Open Networks: Unsecured Wi-Fi networks can be easily accessed by attackers.
- Rogue Access Points: Attackers can set up fake access points to intercept data.
LoRa Technology Vulnerabilities
Long Range (LoRa) technology is increasingly used in smart home applications for its low power consumption and long-range capabilities. However, it also presents unique security challenges.
LoRa Vulnerabilities
Key vulnerabilities associated with LoRa technology include:
- Data Interception: Attackers can intercept LoRa signals if not properly encrypted.
- Device Spoofing: Unauthorized devices can impersonate legitimate LoRa devices.
- Network Attacks: Attackers can disrupt LoRa networks, causing service outages.
IP Camera Security Flaws
IP cameras are a popular component of smart home security systems. However, they can also be a significant security risk if not properly secured.
Common IP Camera Vulnerabilities
Some common vulnerabilities associated with IP cameras include:
- Default Credentials: Many IP cameras come with default usernames and passwords that are rarely changed.
- Unsecured Streaming: Without proper encryption, video feeds can be intercepted.
- Firmware Vulnerabilities: Outdated firmware can expose cameras to known exploits.
Zigbee Protocol Vulnerabilities
Zigbee is a popular wireless communication protocol used in smart home devices. While it offers advantages in low power consumption, it also has vulnerabilities.
Zigbee Vulnerabilities
Key vulnerabilities associated with Zigbee include:
- Weak Encryption: Some Zigbee devices use weak encryption methods, making them susceptible to attacks.
- Network Sniffing: Attackers can intercept Zigbee communications if not properly secured.
- Device Interoperability Issues: Inconsistent security measures across devices can create vulnerabilities.
Wireless Technology Jamming in Smart Homes
Jamming is a technique used by attackers to disrupt wireless communications in smart homes. This can lead to significant security risks.
Impacts of Wireless Jamming
Some potential impacts of wireless jamming include:
- Disruption of Security Systems: Jamming can disable alarms and surveillance systems.
- Loss of Control: Users may lose control over smart devices, leading to potential safety hazards.
- Data Loss: Jamming can result in the loss of critical data transmitted between devices.
Exploiting IoT Devices to Access Personal Computers
Attackers can leverage vulnerabilities in IoT devices to gain access to personal computers and networks.
Common Attack Vectors
Some common methods used by attackers include:
- Device Compromise: Gaining control of an IoT device to launch attacks on connected networks.
- Phishing Attacks: Using compromised devices to send phishing emails to users.
- Malware Distribution: Installing malware on IoT devices to spread to other connected devices.
Strategies for Securing Your Smart Home
To protect your smart home from potential threats, consider implementing the following strategies:
- Change Default Passwords: Always change default passwords to strong, unique ones.
- Enable Two-Factor Authentication: Use two-factor authentication wherever possible to enhance security.
- Regularly Update Firmware: Keep all devices updated with the latest firmware to patch vulnerabilities.
- Use Strong Encryption: Ensure that all communications are encrypted to protect data.
- Secure Your Wi-Fi Network: Use strong passwords and WPA3 encryption for your Wi-Fi network.
- Monitor Device Activity: Regularly check for unusual activity on your devices.
By following these strategies, you can significantly enhance the security of your smart home and protect against potential cyber threats.
Frequently Asked Questions (FAQ)
What are the most common vulnerabilities in smart home devices?
The most common vulnerabilities include weak default passwords, inadequate software updates, insufficient encryption, and limited user awareness.
How can I secure my smart home devices?
To secure your smart home devices, change default passwords, enable two-factor authentication, regularly update firmware, use strong encryption, and monitor device activity.
What is the impact of weak authentication on smart home security?
Weak authentication can allow unauthorized users to gain access to devices and networks, leading to potential data breaches and security incidents.
Are all smart home devices equally vulnerable?
No, the level of vulnerability varies by device and manufacturer. Some devices have stronger security measures than others.
What should I do if I suspect my smart home device has been compromised?
If you suspect a compromise, disconnect the device from the network, change passwords, and perform a factory reset. Consider consulting a cybersecurity professional for further assistance.




Leave a Comment