Spear Phishing: North Korean Hackers’ Top Tactic and Proven Ways to Stay Safe in 2026
Spear phishing remains the go-to attack method for North Korean hackers like the infamous Lazarus Group, according to the latest cybersecurity reports. In their November 2025 Cyber Threat Trends & 2026 Security Outlook, South Korean firm AhnLab highlighted that these state-backed actors dominated post-hack analyses with 31 disclosures over the past year. As artificial intelligence evolves, spear phishing attacks are set to become even more sophisticated, targeting crypto exchanges, finance, and defense sectors with alarming precision.
This targeted form of phishing preys on personalized research, crafting emails disguised as trusted communications like job offers or invitations. Recent incidents, including the $1.4 billion Bybit hack and a $30 million Upbit exploit, underscore the urgency. Staying safe requires multi-layered defenses, from multi-factor authentication to vigilant verification practices.
What Is Spear Phishing and How Does It Differ from Regular Phishing?
Spear phishing is a highly targeted cyberattack where hackers customize messages for specific individuals or organizations after extensive reconnaissance. Unlike generic phishing emails sent to thousands, spear phishing attacks use personal details to build trust, often mimicking colleagues, executives, or partners.
The danger lies in its precision: attackers gather data from social media, company websites, or data breaches to craft convincing lures. According to Kaspersky, this method accounts for over 65% of successful breaches involving social engineering.
How Spear Phishing Attacks Typically Unfold Step-by-Step
- Reconnaissance: Hackers scour LinkedIn, Twitter, or leaked databases for victim details like job titles, recent events, or contacts.
- Crafting the Bait: They create emails or messages posing as legitimate sources, such as “lecture invitations” or “interview requests,” as noted by AhnLab.
- Delivery and Deception: Victims receive links to fake sites or attachments laced with malware, leading to credential theft or ransomware.
- Exploitation: Stolen access grants entry to networks, enabling data theft or fund siphoning.
This step-by-step process makes spear phishing evade basic filters, with success rates up to 50% higher than broad phishing, per Verizon’s 2025 Data Breach Investigations Report.
North Korean Hackers and the Lazarus Group: Leading Spear Phishing Perpetrators
The Lazarus Group, linked to North Korea’s Reconnaissance General Bureau, has mastered spear phishing as their primary weapon. AhnLab’s analysis from October 2024 to September 2025 named them in 31 post-incident reports, far outpacing Kimsuky (27 mentions) and TA-RedAnt (17).
These hackers fund state programs through cyber theft, hitting crypto hard. Their operations blend advanced persistent threats (APTs) with social engineering for maximum impact.
Notable Lazarus Group Spear Phishing Successes in Crypto
- Bybit Hack (Feb 2025): $1.4 billion stolen via targeted employee phishing, exploiting weak email verification.
- Upbit Exploit (Recent): $30 million loss from a spear-phished wallet key compromise.
- Ronin’s Bridge (2022 Legacy): $625 million drained after devs fell for fake update links—lessons still relevant today.
Blockchain analytics firm Chainalysis reports North Korean actors stole $1.34 billion in crypto in 2024 alone, with 70% tied to phishing vectors. This pattern persists into 2026 predictions.
Other North Korean Groups Amplifying Spear Phishing Threats
Kimsuky focuses on espionage via targeted phishing, often in PDFs mimicking Korean government docs. TA-RedAnt targets Southeast Asian finance with multilingual lures. Together, they form a cyber ecosystem, sharing tactics and tools.
Real-World Impacts of Spear Phishing: Crypto, Finance, and Beyond
Spear phishing attacks ripple across sectors, with crypto bearing 40% of Lazarus-linked incidents per AhnLab. Finance loses $4.5 billion annually to phishing globally, says the FBI’s 2025 IC3 Report.
In defense, these attacks steal blueprints; in IT, they install backdoors. A single breach can cascade, as seen in the 2024 SolarWinds supply chain attack partially enabled by phishing.
Pros and Cons of Spear Phishing from an Attacker’s Perspective
“Spear phishing offers high ROI with low tech barriers, but requires time-intensive research—AI is closing that gap.” — AhnLab 2026 Outlook
- Advantages for Hackers: 91% effectiveness in bypassing awareness training (Proofpoint 2025).
- Disadvantages: Traceable if sloppy; multi-layered defenses reduce yields by 80%.
Victims face downtime, fines under GDPR (up to 4% revenue), and reputational hits. Crypto users risk total fund loss without insurance.
How to Protect Yourself from Spear Phishing: Step-by-Step Guide
Defeating spear phishing demands proactive habits. Kaspersky and AhnLab advocate verifying sources independently and layering protections. Start with these essentials.
Essential Individual Defenses Against Targeted Phishing
- Enable Multi-Factor Authentication (MFA): Adds a second layer; hardware keys like YubiKey block 99.9% of account takeovers (Microsoft data).
- Use a VPN: Encrypts traffic, hiding activity from public Wi-Fi snoops—NordVPN reports 75% phishing drop.
- Verify Senders: Call or text the claimed source via known channels before clicking.
- Avoid Oversharing: Lock down social profiles; limit public info to starve reconnaissance.
- Scan Attachments/Links: Use VirusTotal or sandbox tools first.
Adopting these cuts personal risk by 85%, per SANS Institute studies.
Corporate Strategies for Multi-Layered Spear Phishing Defense
Companies need “defense-in-depth.” AhnLab stresses audits, patches, and training.
- Regular Penetration Testing: Simulate attacks quarterly; 60% uncover phishing gaps.
- Employee Training: Phishing sims boost detection to 90% (KnowBe4 metrics).
- Endpoint Detection: Tools like CrowdStrike flag anomalies in real-time.
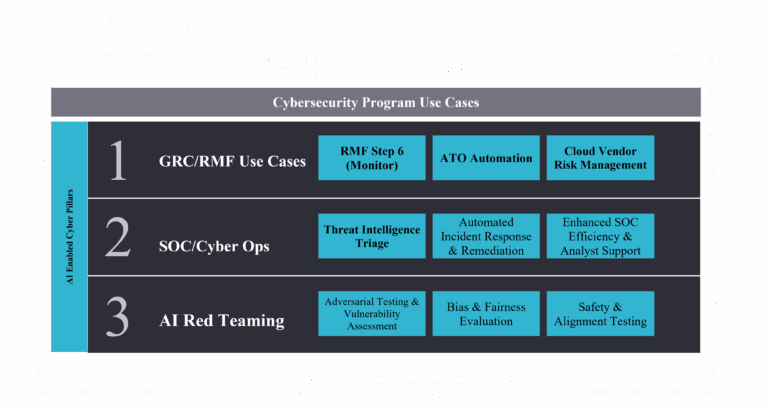
AI’s Role in Supercharging Spear Phishing Threats for 2026
Currently, AI crafts hyper-realistic phishing emails, but in 2026, expect deepfakes and adaptive code. AhnLab warns AI-generated sites fool 70% of users visually.
Attackers use models like GPT variants for personalized lures, evading signatures. Deepfake videos in calls could spike voice phishing (vishing) by 300%, predicts Gartner.
Different Approaches to Counter AI-Enhanced Spear Phishing
- AI Defenses: Tools like Darktrace use ML to spot anomalies—pros: adaptive; cons: false positives.
- Zero-Trust Models: Verify everything; adopted by 82% of Fortune 500 by 2026.
- Behavioral Analytics: Tracks user deviations, blocking 95% of insider threats.
The latest research indicates balanced human-AI oversight is key, blending tech with intuition.
Conclusion: Fortify Against Spear Phishing in an Evolving Threat Landscape
As North Korean hackers refine spear phishing attacks with AI, vigilance is non-negotiable. From Lazarus Group’s crypto heists to predicted 2026 deepfake surges, threats grow smarter.
Implement multi-layered defenses today: MFA everywhere, rigorous verification, and ongoing education. Organizations auditing quarterly see 70% fewer breaches. Stay ahead—your security depends on it.
By connecting reconnaissance to response, this knowledge graph equips you against targeted phishing’s full spectrum.
Frequently Asked Questions (FAQ)
What is spear phishing exactly?
Spear phishing is personalized phishing targeting specific victims with tailored emails or messages based on researched details, unlike mass phishing blasts.
Who are the Lazarus Group and why do they use spear phishing?
North Korean state hackers funding regimes via theft; it’s their top tactic for high-value crypto hits, with 31 AhnLab-tracked incidents last year.
How common are spear phishing attacks in crypto?
Over 40% of Lazarus ops target crypto, stealing $1.34B in 2024 per Chainalysis—expect AI boosts in 2026.
Is MFA enough against spear phishing?
No, but it stops 99% of takeovers; combine with VPNs, verification, and training for full protection.
How will AI change spear phishing in 2026?
AI enables undetectable deepfakes and evasive code, per AhnLab—counter with zero-trust and behavioral tools.
What are the best free tools to detect spear phishing?
VirusTotal for scans, Have I Been Pwned for breach checks, and browser extensions like uBlock Origin for malicious links.
Can spear phishing happen via phone or SMS?
Yes, as vishing or smishing; always verify via alternate channels.

Leave a Comment