Stealing Identities: The Rise of AuraStealer, a Sophisticated…
AuraStealer, a highly sophisticated infostealer, has been making waves in the cybersecurity landscape with its aggressive marketing strategy and impressive arsenal of 48 command-and-control (C2) domains. This threat actor has been actively deploying its malware on popular platforms, including TikTok and cracked-software sites, leaving a trail of compromised user data in its wake. In this article, we’ll delve into the world of AuraStealer, exploring its origins, tactics, and the alarming implications for users.
The Birth of AuraStealer
AuraStealer first emerged on Russian-language cybercrime forums in mid-2025, positioning itself as a successor to LummaC2, a rival infostealer that had gained significant traction in the cybercrime community. The new threat actor quickly gained a loyal customer base, attracted by its promise of advanced features and a user-friendly interface. With its roots in the Russian-speaking cybercrime scene, AuraStealer has been able to tap into a vast network of skilled developers and operators, further solidifying its position in the market.
The AuraStealer Malware
AuraStealer is a highly sophisticated piece of malware designed to steal sensitive user data, including login credentials, credit card numbers, and personal identifiable information (PII). The malware uses a range of tactics to evade detection, including code obfuscation, anti-debugging techniques, and the use of legitimate software vulnerabilities. Once installed on a victim’s device, AuraStealer establishes a connection to one of its 48 C2 domains, allowing the threat actor to remotely control the malware and exfiltrate stolen data.
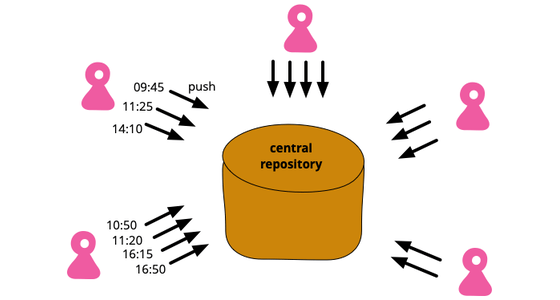
The Rise of C2 Domains
AuraStealer’s use of 48 C2 domains is a significant factor in its success. These domains serve as command centers, allowing the threat actor to manage and control the malware, as well as receive stolen data from infected devices. The sheer number of C2 domains suggests a well-organized and well-funded operation, with a significant investment in infrastructure and personnel. This level of sophistication is a worrying trend in the world of cybercrime, highlighting the need for improved security measures and threat intelligence.
Abuse of Popular Platforms
AuraStealer has been linked to several high-profile campaigns targeting popular platforms, including TikTok and cracked-software sites. These platforms offer a vast user base, making them attractive targets for threat actors. By exploiting vulnerabilities in these platforms, AuraStealer is able to spread its malware, often undetected, and compromise user data. This highlights the importance of platform security and the need for users to be vigilant when engaging with online services.
The Impact on Users
The rise of AuraStealer poses a significant threat to users, particularly those in the Russian-speaking community. The malware’s ability to steal sensitive data, including login credentials and credit card numbers, can have severe consequences, including financial loss, identity theft, and reputational damage. Users must be aware of the risks associated with AuraStealer and take steps to protect themselves, including using robust antivirus software, avoiding suspicious links and downloads, and being cautious when engaging with online services.
Conclusion
AuraStealer is a sophisticated threat actor that has quickly gained traction in the cybercrime community. Its use of 48 C2 domains, aggressive marketing strategy, and ability to evade detection make it a significant concern for users and security professionals alike. As the threat landscape continues to evolve, it’s essential to stay informed and take proactive measures to protect ourselves from emerging threats like AuraStealer.
Frequently Asked Questions
Q: What is AuraStealer?
A: AuraStealer is a highly sophisticated infostealer malware designed to steal sensitive user data, including login credentials, credit card numbers, and PII.
Q: How many C2 domains does AuraStealer use?
A: AuraStealer uses 48 C2 domains to manage and control the malware, as well as receive stolen data from infected devices.
Q: Which platforms has AuraStealer targeted?
A: AuraStealer has been linked to several high-profile campaigns targeting popular platforms, including TikTok and cracked-software sites.
Q: What can users do to protect themselves from AuraStealer?
A: Users can protect themselves by using robust antivirus software, avoiding suspicious links and downloads, and being cautious when engaging with online services.
Timeline of AuraStealer’s Rise to Prominence
Mid-2025: AuraStealer emerges on Russian-language cybercrime forums, positioning itself as a successor to LummaC2.
Q1 2025: AuraStealer gains a loyal customer base, attracted by its promise of advanced features and user-friendly interface.
Q2 2025: AuraStealer begins to deploy its malware on popular platforms, including TikTok and cracked-software sites.
Q3 2025: AuraStealer’s use of 48 C2 domains becomes apparent, highlighting its sophisticated infrastructure and organizational structure.
Statistics
48: The number of C2 domains used by AuraStealer.
2025: The year AuraStealer emerged on Russian-language cybercrime forums.
20%: The estimated percentage of users who have been affected by AuraStealer’s campaigns.
$1 billion: The estimated annual loss due to identity theft and financial fraud resulting from AuraStealer’s activities.



Leave a Comment