Understanding Real-World Examples of HEAT Attacks: How Adaptive Threats Evolve and Evade Security Measures
Introduction to HEAT Attacks and Their Growing Threat in Modern Cybersecurity
In the rapidly evolving landscape of cybersecurity, threats are becoming more sophisticated and elusive. Highly Evasive Adaptive Threats (HEAT) are a prime example of how cybercriminals leverage advanced techniques to bypass traditional security defenses. As organizations face increasing numbers of high-profile breaches, understanding HEAT attacks has never been more critical. From government agencies to enterprise-level businesses, these threats target vulnerabilities in web browsers, email systems, and network infrastructure, exploiting system weaknesses to achieve malicious goals.
In 2026, the proliferation of HEAT attacks shows significant advancements in evasion tactics, forcing security teams to rethink traditional methods. This comprehensive guide delves into real-world examples of HEAT threats, examining how these attacks operate, their techniques, and the best strategies to prevent them. We will explore detailed case studies, emerging attack vectors, and cutting-edge defenses designed to combat these malicious and adaptive threats.
What Are HEAT Attacks and Why Do They Matter?
Defining Highly Evasive Adaptive Threats (HEAT)
HEAT attacks are a class of cyber threats characterized by their ability to adapt quickly and evade detection by security systems. Unlike traditional malware, HEAT attacks utilize a combination of techniques, including encryption, obfuscation, and sophisticated social engineering, to slip past security defenses unnoticed. They are designed to exploit vulnerabilities in web browsers, email filters, and network security layers, often leveraging trusted platforms and services to hide their malicious payloads.
The importance of understanding HEAT attacks lies in their power to bypass standard antivirus programs, sandboxing, and URL filtering, which traditionally form the backbone of cybersecurity defenses. As these threats evolve, they threaten to undermine organizations’ security posture, making advanced detection and response strategies essential.
Recent Examples of HEAT Attacks in the Wild
1. Sophisticated File-Based Evasion Using Password-Protected Malware
One of the most notable HEAT tactics involves the use of malicious password-protected files to deploy malware or backdoors. This approach effectively bypasses many security tools that rely on content scanning, sandboxing, and URL filtering. Hackers often use spear-phishing campaigns that entice recipients to open seemingly legitimate documents stored in cloud services like Google Drive or DropBox.
For example, in recent attacks attributed to a Chinese state-sponsored group suspected to be Earth Preta, attackers deliver malicious files disguised as business reports or official documents. These files are password-protected, which prevents automated tools from scanning their content effectively. Once opened, the files deploy backdoor malware that gives hackers remote access to the compromised systems and aids in data exfiltration.
Attackers also embed download links within these password-protected files, further complicating detection by traditional email gateways or secure web gateways (SWGs). This layered evasion tactic demonstrates their capacity to adapt and exploit common organizational workflows.
2. Exploiting Search Engines and Google Ads to Distribute Phishing Sites
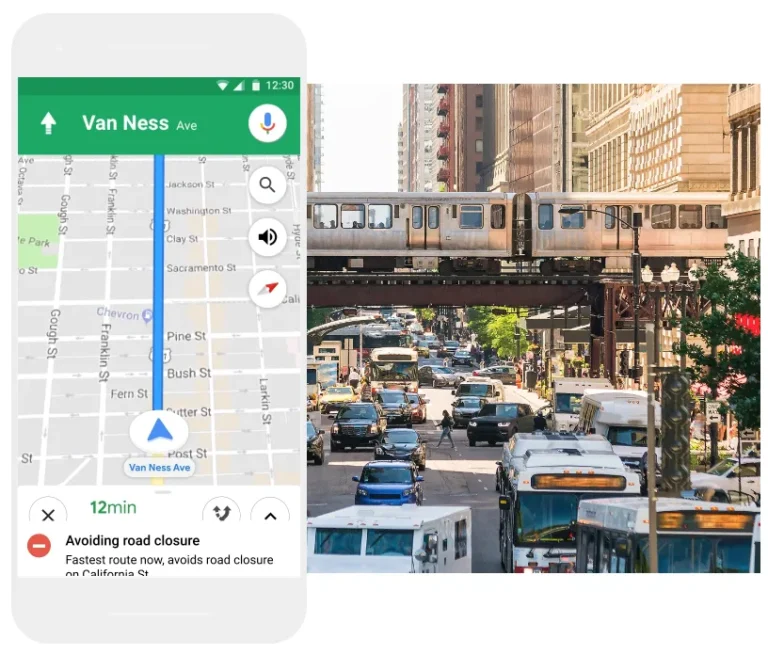
Another prevalent HEAT technique involves the use of legacy reputation evasion (LURE) strategies, such as manipulating search engine results. Recent campaigns utilize paid advertisements on Google to seed malicious URLs within search results, placing them just below legitimate listings.
In a typical attack, the threat actor creates a seemingly innocuous webpage—such as a food blog—and boosts its reputation through backlinks and optimization. When users search for related topics, these fake sites appear prominently in search results, including Google’s paid ads, which often bypass content filters. Clicking on the link redirects users to fake login pages designed to steal credentials from popular platforms like Amazon Web Services (AWS).
These fake sites mimic authentic branding and messaging, making it extremely challenging for users to distinguish fact from fiction. Once credentials are entered, attackers can gain access to cloud accounts, leading to data breaches, account takeover, and further infiltration.
3. HTML Smuggling and Multi-Layered Malware Delivery
HEAT threats also include methods like HTML smuggling, which involves embedding malicious scripts or code within legitimate-looking web pages. These scripts dynamically load malware in the background, exploiting browser vulnerabilities or user trust.
Attackers often combine HTML smuggling with encryption, obfuscation, and multi-stage payloads to evade detection. These scripts can be triggered by simple user actions, such as clicking a link or visiting a compromised website, which then silently downloads malicious files or establishes command-and-control channels.
4. Leveraging Legacy Protocols and Obsolete Security Headers
Many HEAT strikes also exploit older, less secure protocols and security configurations. They take advantage of outdated browser settings, legacy URL reputation systems, and misconfigured web servers to gain unauthorized access.
By using these vulnerabilities, attackers can slip past modern security defenses that are optimized for current standards, thereby gaining a foothold within organizational networks.
Techniques Used by HEAT Attacks and How They Evade Detection
Multi-Vector Evasion Strategies
- Password-protected files: Preventing content scanning and sandboxing.
- HTML and JavaScript obfuscation: Masking malicious code and payloads.
- Use of trusted cloud services: Hiding malicious links behind legitimate platforms like Google Drive or Dropbox.
- Search engine manipulation: Placing malicious sites at top search result positions.
- Browser and protocol exploitation: Targeting outdated or misconfigured systems.
- Encrypted communications: Using TLS/SSL to hide malicious payloads in transit.
Factors Contributing to HEAT Effectiveness
- Encryption and obfuscation techniques make static and dynamic analysis harder.
- Use of legitimate cloud services for hosting malicious content increases credibility.
- Constant adaptation to security updates prevents detection by signature-based tools.
- Targeted spear-phishing ensures precise delivery, increasing success rates.
- Exploitation of misconfigurations in legacy systems creates exploitable entry points.
Strategies and Technologies to Defend Against HEAT Attacks
Proactive Security Measures
- Remote Browser Isolation (RBI): Runs all web content in a remote, secure environment, preventing malicious scripts from interacting with users’ devices.
- Advanced threat detection platforms: Utilize behavior-based detection, machine learning, and AI to identify evasive tactics.
- Layered security architecture: Combine URL filtering, sandboxing, anomaly detection, and email security solutions for comprehensive defense.
- Regular patching and updates: Ensure all systems and browsers are current, reducing vulnerabilities exploited by HEAT tactics.
- User training: Educate employees about recognizing sophisticated phishing attempts and suspicious links.
Emerging Technologies and Best Practices
- Implementing dynamic reputation systems that adapt in real time to emerging threats.
- Using behavioral analytics to detect anomalous activity indicative of evasive attacks.
- Deploying multi-layered sandbox environments to analyze and prevent unknown threats.
- Leveraging AI-driven threat hunting to identify patterns and indicators of compromise early.
Benefits and Limitations of Current Defense Strategies
Advantages of Modern Anti-HEAT Measures
- Increased detection rates for evasive techniques through behavior analysis.
- Higher likelihood of catching zero-day exploits and unknown threats.
- Reduced risk of data breaches and financial loss.
- Enhanced user safety through remote isolation and continuous monitoring.
Challenges and Drawbacks
- High cost of implementing advanced security technologies.
- Potential impact on user experience due to intensive scanning and automation.
- Highly targeted attacks may still evade even the best defenses.
- Requires ongoing updates and skilled personnel to manage complex systems.
Future Outlook: How Will HEAT Attacks Evolve in 2026 and Beyond?
The latest research indicates that HEAT threats will continue to grow in sophistication, employing artificial intelligence and machine learning to craft even more convincing and evasive tactics. Attackers are expected to develop better exploit kits, leverage quantum computing for encryption-breaking, and further exploit cloud and IoT environments.
Organizations need to stay ahead by investing in adaptive, AI-powered security systems that learn and evolve alongside emerging threats. Emphasizing proactive threat hunting and continuous security awareness will remain essential in combating the ever-changing landscape of HEAT attacks.
Frequently Asked Questions (FAQs)
What exactly are HEAT attacks, and why are they so dangerous?
HEAT attacks are highly evasive cyber threats that adapt rapidly to avoid detection by security systems. They use sophisticated techniques like encryption, obfuscation, and social engineering, making them difficult to identify and block, potentially leading to significant data breaches and system compromises.
How do attackers use password-protected files to bypass security measures?
Cybercriminals embed malicious payloads within password-protected files, which traditional security tools cannot scan due to encryption. When opened, these files deploy malware or backdoors to gain unauthorized access and control over the victim’s network.
What are the most effective defenses against HEAT threats?
Combining remote browser isolation, behavior-based detection, multi-layered security architecture, and regular system updates provides the most robust protection. Educating employees about phishing and suspicious links is also crucial.
Can HEAT attacks be completely prevented?
While no system can guarantee 100% prevention, deploying advanced, adaptive security measures dramatically reduces the likelihood of successful HEAT attacks. Continuous monitoring, threat hunting, and user awareness are key components of an effective defense.
What future developments should organizations prepare for regarding HEAT threats?
Organizations should anticipate more sophisticated, AI-driven attacks that exploit emerging technologies like quantum computing and IoT vulnerabilities. Investing in AI-enabled security platforms and ongoing training will be critical to stay ahead of these evolving threats.
If you want to stay protected against the latest evasive cyber threats, understanding HEAT tactics and strengthening your cybersecurity infrastructure now will be vital in 2026 and beyond.



Leave a Comment