Understanding Zero-Day Vulnerabilities: A Comprehensive Guide to Cybersecurity Risks
In the ever-evolving landscape of cybersecurity, the term “zero day” holds immense significance. It refers to a newly identified vulnerability that cybercriminals exploit before software developers have the opportunity to address it. This situation presents a formidable challenge to digital security, as organizations must remain vigilant against threats that can emerge without warning.
The Concept of Zero-Day Vulnerabilities
A zero-day vulnerability is defined as a security flaw that is exploited by hackers before it is known to the software developers. This term essentially marks the moment of discovery, indicating that a new threat is actively being used against unsuspecting users. However, the reality of zero-day vulnerabilities is more complex; numerous vulnerabilities may exist undetected, lurking in the digital realm like hidden traps.
Understanding the Implications
The implications of zero-day vulnerabilities are profound. When a zero-day exploit is discovered, it can lead to significant security breaches, data theft, and system compromises. For instance, recent vulnerabilities identified in Microsoft Exchange (ZDI-23-1578, ZDI-23-1579, ZDI-23-1580, ZDI-23-1581) allowed for remote code execution, showcasing the potential damage that can arise from such exploits.
The Spectrum of Zero-Day Vulnerabilities
Zero-day vulnerabilities can vary dramatically in their severity. Some may be minor glitches that pose little risk, while others can be critical vulnerabilities that threaten an organization’s entire infrastructure. Understanding this spectrum is essential for organizations to prioritize their security efforts effectively.
- Minor Vulnerabilities: These may cause inconvenience but are unlikely to lead to serious breaches.
- Moderate Vulnerabilities: These can lead to unauthorized access but may require specific conditions to be exploited.
- Critical Vulnerabilities: These pose an immediate threat, potentially allowing attackers to gain full control over systems.
Examples of Recent Zero-Day Vulnerabilities
In 2026, the cybersecurity landscape witnessed several notable zero-day vulnerabilities:
- Microsoft Exchange Vulnerabilities: As mentioned earlier, these vulnerabilities allowed for remote code execution, impacting countless organizations.
- Adobe Flash Player Exploit: A critical flaw that enabled attackers to execute arbitrary code on affected systems.
- Google Chrome Vulnerability: A zero-day exploit that allowed attackers to bypass security measures and execute malicious scripts.
Mitigating the Risks of Zero-Day Vulnerabilities
As technology advances, so does the risk associated with zero-day vulnerabilities. Organizations must adopt proactive measures to mitigate these risks effectively. Understanding your attack surface is crucial in this endeavor.
Strategies for Risk Mitigation
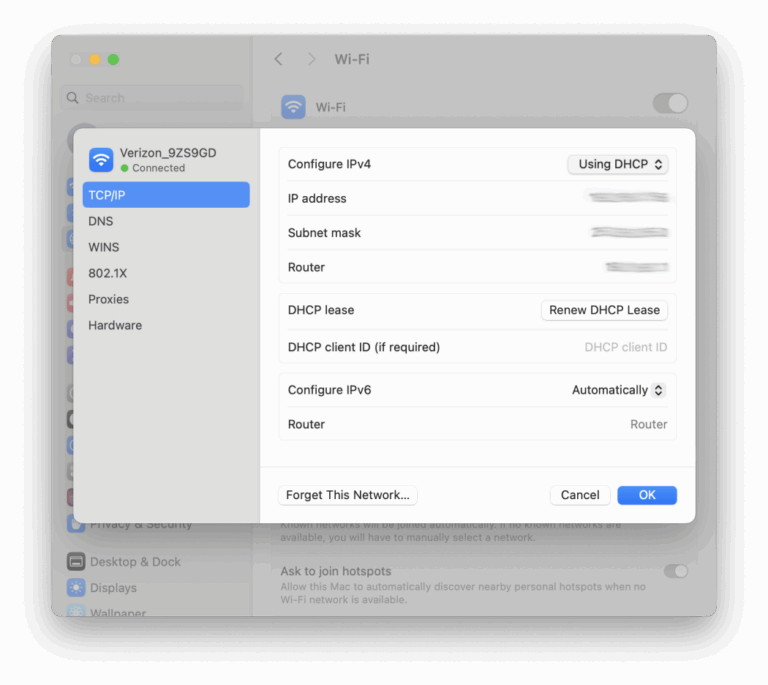
- Implement Monitoring and Detection: Utilize advanced monitoring tools to identify suspicious activities and anomalous behavior.
- Reduce the Attack Surface: Limit the number of entry points into your systems to make it more challenging for attackers to exploit vulnerabilities.
- Regular Software Updates: Ensure that all software is up-to-date to minimize the risk of exploitation.
- Employee Training: Educate employees about cybersecurity best practices to reduce the likelihood of human error leading to breaches.
The Importance of Collaboration in Cybersecurity
Collaboration is vital in the ongoing battle against zero-day threats. By sharing information, resources, and best practices, the cybersecurity community can strengthen defenses and mitigate the impact of these hidden dangers.
Building a Collaborative Cybersecurity Environment
Organizations can foster collaboration in several ways:
- Information Sharing: Participate in industry forums and share insights about emerging threats and vulnerabilities.
- Joint Training Exercises: Conduct joint training sessions with other organizations to enhance response strategies.
- Collaborative Research: Engage in research initiatives to develop new tools and techniques for identifying and mitigating zero-day vulnerabilities.
Addressing Browser-Based Zero-Day Exploits
Traditional security tools often struggle to combat the evolving threat of browser-based zero-day exploits. These vulnerabilities can be particularly insidious, as they may not be detected until after an attack has occurred.
Innovative Solutions for Browser Security
Menlo Security offers a unique approach that transcends the capabilities of legacy defenses. Their solutions, including the Menlo Secure Cloud Browser and Menlo HEAT Shield, utilize innovative isolation techniques to neutralize threats effectively.
By executing web content in a secure cloud environment, Menlo Security protects users from the most evasive attacks. This proactive isolation ensures that even if a new zero-day vulnerability is discovered, users remain shielded from its effects.
Conclusion
In conclusion, understanding zero-day vulnerabilities is crucial for organizations aiming to protect their digital assets. By recognizing the spectrum of these vulnerabilities, implementing effective risk mitigation strategies, fostering collaboration, and adopting innovative security solutions, organizations can enhance their defenses against the ever-present threat of zero-day exploits. As the cybersecurity landscape continues to evolve, staying informed and proactive will be key to safeguarding against these hidden dangers.
Frequently Asked Questions (FAQ)
What is a zero-day vulnerability?
A zero-day vulnerability is a security flaw that is exploited by hackers before the software developers are aware of it, posing significant risks to digital security.
How can organizations mitigate zero-day vulnerabilities?
Organizations can mitigate zero-day vulnerabilities by implementing monitoring tools, reducing their attack surface, regularly updating software, and training employees on cybersecurity best practices.
What are some examples of recent zero-day vulnerabilities?
Recent examples include vulnerabilities in Microsoft Exchange, Adobe Flash Player, and Google Chrome, which allowed for remote code execution and other malicious activities.
Why is collaboration important in cybersecurity?
Collaboration is essential in cybersecurity as it enables organizations to share information, resources, and best practices, strengthening defenses against emerging threats.
How does Menlo Security address browser-based zero-day exploits?
Menlo Security uses innovative isolation techniques in their Secure Cloud Browser and HEAT Shield to protect users from browser-based zero-day exploits by executing web content in a secure environment.



Leave a Comment